Designing a security policy to protect your ... - Schneider Electric
Designing a security policy to protect your ... - Schneider Electric
Designing a security policy to protect your ... - Schneider Electric
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>Designing</strong> a <strong>security</strong> <strong>policy</strong> <strong>to</strong><br />
<strong>protect</strong> <strong>your</strong> au<strong>to</strong>mation solution<br />
September 2009 / White paper<br />
by Dan DesRuisseaux<br />
1
White paper: <strong>Designing</strong> a <strong>security</strong> <strong>policy</strong> <strong>to</strong> <strong>protect</strong> <strong>your</strong> au<strong>to</strong>mation solution<br />
Contents<br />
Executive Summary ................................................... p 3<br />
Introduction................................................................. p 4<br />
Security Guidelines .................................................... p 7<br />
Conclusion ................................................................. p 13<br />
2
White paper: <strong>Designing</strong> a <strong>security</strong> <strong>policy</strong> <strong>to</strong> <strong>protect</strong> <strong>your</strong> au<strong>to</strong>mation solution<br />
Executive summary<br />
Network <strong>security</strong> for au<strong>to</strong>mation solutions is a concept that has been<br />
getting increased attention over the last decade. In the past, <strong>security</strong><br />
was not a major concern because au<strong>to</strong>mation systems utilized<br />
proprietary components and were isolated from other networks within<br />
the business.<br />
Today, many au<strong>to</strong>mation systems are comprised of commercial off the<br />
shelf components, including Ethernet networking and Windows<br />
operating systems. In addition, legacy products are being updated <strong>to</strong><br />
operate in these new network environments.<br />
The consequence is that formerly closed systems are suddenly<br />
connected <strong>to</strong> open enterprise networks and the Internet, exposing<br />
improperly <strong>protect</strong>ed systems <strong>to</strong> modern IT threats.<br />
3
White paper: <strong>Designing</strong> a <strong>security</strong> <strong>policy</strong> <strong>to</strong> <strong>protect</strong> <strong>your</strong> au<strong>to</strong>mation solution<br />
Introduction<br />
Security threats can be initiated from 4 different sources. Each source<br />
is defined below along with an example of a recent incident that<br />
illustrates the threat.<br />
> Targeted External Attack – The CIA revealed that cyber attacks<br />
on utilities have caused at least one power outage affecting<br />
multiple cities.<br />
> Random External Attack – The “Slammer Worm” penetrated a<br />
nuclear power plant and disabled a safety moni<strong>to</strong>ring system for<br />
nearly 5 hours. The worm entered through an interconnected<br />
contrac<strong>to</strong>r’s network, bypassing the firewall.<br />
> Internal Malicious Attack – A disgruntled former contrac<strong>to</strong>r gained<br />
access <strong>to</strong> the control system of a sewage treatment facility in<br />
Australia and flooded the surrounding area with millions of litres<br />
of untreated sewage.<br />
> Internal Networking/ Configuration Issue – A data s<strong>to</strong>rm initiated<br />
by a PLC at a nuclear power plant required opera<strong>to</strong>rs <strong>to</strong> shut<br />
down the reac<strong>to</strong>r after two water pumps failed.<br />
One way <strong>to</strong> address solution <strong>security</strong> is through the implementation of<br />
secure products. Secure products take two forms. The first is <strong>security</strong><br />
features implemented in classic au<strong>to</strong>mation products. Examples<br />
include authentication and <strong>security</strong> logging in a PLC. The second form<br />
is stand-alone products developed specifically <strong>to</strong> address solution<br />
<strong>security</strong>. Examples include firewalls and intrusion detection software.<br />
It is important <strong>to</strong> note that secure products by themselves will not<br />
enable a secure solution. Companies also need <strong>to</strong> implement a<br />
comprehensive <strong>security</strong> <strong>policy</strong>. A <strong>security</strong> <strong>policy</strong> states the <strong>security</strong><br />
objectives and guidelines that must be in place <strong>to</strong> ensure solution<br />
<strong>security</strong>. A company’s <strong>security</strong> <strong>policy</strong> should be a living document, not<br />
a static <strong>policy</strong>.<br />
4
White paper: <strong>Designing</strong> a <strong>security</strong> <strong>policy</strong> <strong>to</strong> <strong>protect</strong> <strong>your</strong> au<strong>to</strong>mation solution<br />
Introduction (continued)<br />
A company should also conduct a vulnerability assessment prior <strong>to</strong><br />
creating their <strong>security</strong> <strong>policy</strong>. The vulnerability assessment is<br />
performed by reviewing the network architecture and auditing the<br />
equipment and software within the network. The assessment<br />
produces a document that defines and prioritizes the potential risks<br />
along with costs <strong>to</strong> address potential vulnerabilities.<br />
Many companies have defined and implemented <strong>security</strong> policies,<br />
while others have added <strong>security</strong> products (firewalls) but not<br />
addressed a <strong>security</strong> <strong>policy</strong>. This document is designed <strong>to</strong> assist<br />
companies in creating a <strong>security</strong> <strong>policy</strong> by providing a list of<br />
accepted <strong>security</strong> guidelines. Companies can review the list and<br />
select those that are suited <strong>to</strong> their application requirements.<br />
5
White paper: <strong>Designing</strong> a <strong>security</strong> <strong>policy</strong> <strong>to</strong> <strong>protect</strong> <strong>your</strong> au<strong>to</strong>mation solution<br />
A disgruntled former<br />
contrac<strong>to</strong>r gained<br />
access <strong>to</strong> the control<br />
system of a sewage<br />
treatment facility in<br />
Australia and flooded<br />
the surrounding area<br />
with millions of litres of<br />
untreated sewage.<br />
6
White paper: <strong>Designing</strong> a <strong>security</strong> <strong>policy</strong> <strong>to</strong> <strong>protect</strong> <strong>your</strong> au<strong>to</strong>mation solution<br />
Security Guidelines<br />
Many individual guidelines comprise a comprehensive <strong>security</strong> <strong>policy</strong>. Individual guidelines will be<br />
grouped in<strong>to</strong> sub-categories <strong>to</strong> simplify presentation.<br />
Physical Access <strong>to</strong> the Network<br />
One key <strong>to</strong> <strong>security</strong> involves restricting network access <strong>to</strong> specified personnel and equipment.<br />
> Critical infrastructure should be placed in a secure location (preferably a locked room) <strong>to</strong> prevent<br />
unauthorized access. Ensure that portals <strong>to</strong> critical infrastructure are closed and locked.<br />
> Disable all unused ports.<br />
> Do not let unauthorized lap<strong>to</strong>ps or memory sticks in<strong>to</strong> a secure location. If lap<strong>to</strong>ps or<br />
memory sticks are required, set up processes <strong>to</strong> ensure that all portable media are scanned<br />
for malware with up <strong>to</strong> date scanning software before allowing contact with a network host.<br />
Authentication/ Authorization<br />
Authentication refers <strong>to</strong> the verification process <strong>to</strong> confirm identification for the purpose of accessing<br />
network resources. Authorization refers <strong>to</strong> access permissions allowing users <strong>to</strong> connect with devices.<br />
This combination allows the system <strong>to</strong> restrict network access and ensure that only the right personnel are<br />
accessing network resources.<br />
> Each user should have a unique user name and password. User names and passwords<br />
should not be shared <strong>to</strong> enable easier tracking of system events.<br />
> Solutions must enable the creation, editing, and deletion of users while the system is active.<br />
> System must not provide a “back door” allowing bypass of authentication procedures.<br />
> Critical data like user names and passwords must be s<strong>to</strong>red in a secure data reposi<strong>to</strong>ry<br />
using encryption technology. Access rights <strong>to</strong> the reposi<strong>to</strong>ry require authentication and<br />
should be made available only <strong>to</strong> trusted personnel.<br />
> Implement password aging.<br />
> Passwords should be more than 8 characters, alphanumeric, and a mix of upper and lower<br />
case characters.<br />
> Staff should change default passwords on equipment.<br />
> Use switch port-based MAC address management <strong>to</strong> deny access <strong>to</strong> non-authorized users.<br />
> Remote authentication should use encryption technology <strong>to</strong> transfer user name and<br />
password through the system.<br />
7
White paper: <strong>Designing</strong> a <strong>security</strong> <strong>policy</strong> <strong>to</strong> <strong>protect</strong> <strong>your</strong> au<strong>to</strong>mation solution<br />
> Limit software installation and execution privileges <strong>to</strong> specific employees. When risk is<br />
high, implement two and three fac<strong>to</strong>r authentication (password, physical device - smart key,<br />
and biometrics) or real-time confirmation by a second person.<br />
> Restrict user access <strong>to</strong> data archives.<br />
> Authentication should be required <strong>to</strong> modify product firmware.<br />
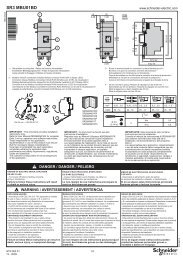
Network Design<br />
Vulnerability assessment will provide the data needed <strong>to</strong> create a<br />
secure network design. One key <strong>to</strong> securing the au<strong>to</strong>mation<br />
network is understanding the entry/connection points between it<br />
and the greater IT system. Potential connection points between<br />
networks include OPC servers, gateways, modems, and safety<br />
network connectivity.<br />
One key concept <strong>to</strong> network design is Defense in Depth. Defense<br />
in Depth is designed <strong>to</strong> <strong>protect</strong> control and safety systems. There<br />
is no single mechanism <strong>to</strong> <strong>protect</strong> against all types of attacks.<br />
Therefore it is best <strong>to</strong> create a series of <strong>protect</strong>ion layers designed <strong>to</strong> impede attackers. The<br />
layers also improve probability that attacks will be detected and repelled. Safety networks should<br />
be at least one layer deeper in a Defense in Depth architecture than the control network.<br />
> If the au<strong>to</strong>mation network connects <strong>to</strong> a larger corporate network, a “demilitarized zone”<br />
should be created <strong>to</strong> buffer common resources between the two networks. A demilitarized<br />
zone is a buffer between a trusted network and an untrusted network.<br />
The zone is separated by firewalls and routers.<br />
> Elements in the au<strong>to</strong>mation network or trusted zones within the network should be in a<br />
separate subnet from the greater network and should be isolated via a router and or firewall.<br />
> The firewall fronting the au<strong>to</strong>mation system should include an intrusion detection system.<br />
> If using multiple firewalls, consider centralized firewall policies.<br />
> It should be possible <strong>to</strong> easily isolate the au<strong>to</strong>mation network from the corporate network if<br />
an intrusion is detected.<br />
> Configure the network <strong>to</strong> eliminate requests from the control network <strong>to</strong> external computers.<br />
A firewall should block all connections from the outside.<br />
> Remove or disable all unrequired services from au<strong>to</strong>mation hosts.<br />
8
White paper: <strong>Designing</strong> a <strong>security</strong> <strong>policy</strong> <strong>to</strong> <strong>protect</strong> <strong>your</strong> au<strong>to</strong>mation solution<br />
> Utilize port restriction. For example, if you would like <strong>to</strong> allow an individual <strong>to</strong> program<br />
Modbus but not access the web server, then enable the device access <strong>to</strong> TCP port 502<br />
(Modbus) but not port 80.<br />
> Older Windows systems with limited <strong>security</strong> features should not be connected with an<br />
industrial system unless they are compartmentalized.<br />
> Examine contrac<strong>to</strong>r network access levels. Prevent un<strong>protect</strong>ed access <strong>to</strong> au<strong>to</strong>mation network.<br />
> Prevent incoming e-mail or Instant Messaging traffic <strong>to</strong> hosts in the au<strong>to</strong>mation network.<br />
Disable or do not install e-mail or IM clients on computers in the au<strong>to</strong>mation domain.<br />
Additionally, block corresponding pro<strong>to</strong>cols at the firewall.<br />
> Prohibit web browsing from hosts in the au<strong>to</strong>mation network. Prevent access by filtering at<br />
the firewall.<br />
> Provide internet access from a separate host on<br />
a different network than the au<strong>to</strong>mation network<br />
so that information and updates from the Internet<br />
Plant network<br />
Connection <strong>to</strong> supervisory<br />
and information systems<br />
can be obtained if the main network is down.<br />
> Prohibit drive sharing between hosts inside and<br />
outside the au<strong>to</strong>mation network. Enforce with<br />
firewalls.<br />
> If necessary, restrict ability for personnel <strong>to</strong><br />
Control network/<br />
Au<strong>to</strong>mation systems<br />
configure devices via the web.<br />
> Prohibit direct transfer of files in<strong>to</strong> the control<br />
Fiber optic ring<br />
system. An intermediate staging server should<br />
Gateway<br />
Drive<br />
be used <strong>to</strong> scan all incoming data for malware.<br />
Modbus<br />
Digital signatures can help verify that the file<br />
Advantys OTB IP67 I/O Advantys STB Momentum Advantys OTB<br />
really originated from the assumed server and<br />
that it wasn’t modified between the scan and<br />
Figure above<br />
import in<strong>to</strong> the control system.<br />
Typical <strong>security</strong>-enabled au<strong>to</strong>mation network design<br />
> Firewalls should provide network address<br />
translation <strong>to</strong> <strong>protect</strong> the address data from the<br />
corporate network.<br />
> Use trained, authorized personnel <strong>to</strong> add/remove new devices <strong>to</strong>/from the control network.<br />
> Non essential services with known weaknesses should be offered on one of several<br />
redundant servers <strong>to</strong> reduce the effect of infection.<br />
Demilitarized zone<br />
9
White paper: <strong>Designing</strong> a <strong>security</strong> <strong>policy</strong> <strong>to</strong> <strong>protect</strong> <strong>your</strong> au<strong>to</strong>mation solution<br />
Remote Access<br />
Remote access should be enabled with the highest level of <strong>security</strong> available <strong>to</strong> the organization.<br />
Remote access should be provided with strong authentication, encryption, and, if possible,<br />
include the exchange and verification of certificates. Remote access policies should be<br />
restrictive, allowing the minimum number of rights for the minimum number of remote users.<br />
Remote access is typically provided through dial-up or VPN.<br />
> If remote access is provided by dial up, <strong>protect</strong>ion can be provided via:<br />
• Dial-out – connection initiated from inside the<br />
au<strong>to</strong>mation system.<br />
• Dial-in with Call-back – the remote user dials in<strong>to</strong> a<br />
server in the system which calls back <strong>to</strong> one of a<br />
limited set of pre-defined phone numbers.<br />
• Temporarily enabled Dial-in – the modem is enabled<br />
for a specific dial-in event. The modem connection is<br />
disabled when there is no intended use, either<br />
physically or by switching it off, or by software means.<br />
> VPN – The preferred way <strong>to</strong> provide remote access. If configuring safety or mission critical<br />
functions, organizations should define a fallback behaviour if there is a temporary loss of<br />
remote connection.<br />
> Enforce application settings on both the client and server <strong>to</strong> change well known port<br />
numbers frequently targeted by virus attacks.<br />
Wireless<br />
Many of the guidelines presented below require wireless devices <strong>to</strong> support specific <strong>security</strong><br />
features. The guidelines below can provide input <strong>to</strong> features required in wireless devices.<br />
> Place access points behind firewalls and use IPsec <strong>to</strong> prevent rogue access point access.<br />
> Network access points should be positioned and arranged such that the useful signal<br />
strength is limited as far as possible <strong>to</strong> within the physically secured perimeter. Directional<br />
antennas can assist in forming a wireless footprint.<br />
10
White paper: <strong>Designing</strong> a <strong>security</strong> <strong>policy</strong> <strong>to</strong> <strong>protect</strong> <strong>your</strong> au<strong>to</strong>mation solution<br />
> Many access points have the ability <strong>to</strong> define a list of approved clients (listed via MAC<br />
address). Undefined clients can not access the network. Network administra<strong>to</strong>rs should<br />
define approved clients. The ability <strong>to</strong> provision approved clients should be restricted <strong>to</strong><br />
key personnel.<br />
> Client devices must authenticate <strong>to</strong> enter the network. For authentication, use extensible<br />
authentication pro<strong>to</strong>cols such as EAP-TTLS, EAP-MSCHAPV2, or RADIUS.<br />
> Do not utilize WEP <strong>security</strong>. Use WPA-2 <strong>security</strong> in addition <strong>to</strong> AES-CCMP or equivalent<br />
encryption.<br />
> Do not broadcast SSIDs <strong>to</strong> prevent the network from showing up in wireless network<br />
scans. Also, do not enable ad-hoc connections.<br />
> Moni<strong>to</strong>r networks for denial of service attacks and alarm if detected.<br />
> Utilize frequency hopping radios <strong>to</strong> limit unauthorized access from external equipment.<br />
> Frequently review access logs <strong>to</strong> identify rogue devices and access points. Proactive<br />
review can provide early warning of intrusion attempts.<br />
Maintenance<br />
> Create procedures for dealing with <strong>security</strong> issues. Procedures include event identification,<br />
containment, root cause determination, resolution, and recurrence <strong>protect</strong>ion.<br />
> Moni<strong>to</strong>r system logs or use intrusion detection software <strong>to</strong> help anticipate attacks<br />
(configuration changes and creation of secondary accounts for example). Insure that there<br />
are no foreign IP addresses on <strong>your</strong> network or logs. If so, locate IP address origin and<br />
take action.<br />
> Create detailed plans defining how <strong>to</strong> recover from attack. Examples include warm standby<br />
backup hosts isolated from the network and system backups on swappable and bootable<br />
hard disks for immediate restart. Generate a list of personnel <strong>to</strong> be contacted if an incident<br />
occurs and keep copies of device configuration files, programs, and SCADA images.<br />
> Run virus checks on equipment on a regular basis. For critical infrastructure, scan<br />
communications <strong>to</strong> prevent viruses from accessing the platform.<br />
> Software can be updated via CD/DVD or file transfer. If CD/DVD, insure that the discs are<br />
of proper origin and are virus free. If downloaded via file, insure the authenticity of the file<br />
via certificates and digital signatures and insure they are virus free. All files should be<br />
s<strong>to</strong>red on a dedicated distribution server. Updates can only be administered by an<br />
authorized person operating inside the au<strong>to</strong>mation network.<br />
> Moni<strong>to</strong>r network traffic <strong>to</strong> enable early detection of possible data s<strong>to</strong>rms.<br />
> Test and approve software patches on standard machines that match the plant floor prior <strong>to</strong><br />
installing on live systems.<br />
11
White paper: <strong>Designing</strong> a <strong>security</strong> <strong>policy</strong> <strong>to</strong> <strong>protect</strong> <strong>your</strong> au<strong>to</strong>mation solution<br />
General Security Policy<br />
> Ensure that all <strong>security</strong> incidents are reported.<br />
> Hold regular audits of <strong>security</strong> <strong>policy</strong>.<br />
> Review incidents and new technologies <strong>to</strong> see if changes are required <strong>to</strong> existing policies.<br />
> For legacy systems where upgrades may have occurred over the years, obtain current<br />
documentation <strong>to</strong> ensure knowledge of what is operating in the network.<br />
> Test detection and alert systems.<br />
> Test disaster recovery implementations.<br />
> Perform background checks on personal with access <strong>to</strong> critical systems.<br />
> Review people-management practices including methods <strong>to</strong> escalate and resolve<br />
grievances <strong>to</strong> curb internally generated attacks.<br />
12
White paper: <strong>Designing</strong> a <strong>security</strong> <strong>policy</strong> <strong>to</strong> <strong>protect</strong> <strong>your</strong> au<strong>to</strong>mation solution<br />
Conclusion<br />
A well designed Security Policy is<br />
essential <strong>to</strong> secure <strong>your</strong> au<strong>to</strong>mation<br />
solution<br />
Au<strong>to</strong>mation networks using standards-based operating systems<br />
and networks require greater <strong>security</strong> than the proprietary<br />
systems used in decades past. Standards-based solutions can<br />
be secured using existing products and technologies. Products<br />
and technology alone can not effectively secure an au<strong>to</strong>mation<br />
solution; they must be deployed in conjunction with a <strong>security</strong><br />
<strong>policy</strong>. A well designed <strong>security</strong> <strong>policy</strong> coupled with diligent<br />
maintenance and oversight are essential <strong>to</strong> securing modern<br />
au<strong>to</strong>mation networks.<br />
13
White paper: <strong>Designing</strong> a <strong>security</strong> <strong>policy</strong> <strong>to</strong> <strong>protect</strong> <strong>your</strong> au<strong>to</strong>mation solution<br />
Make the most of <strong>your</strong> energy<br />
<strong>Schneider</strong> <strong>Electric</strong><br />
© 2009 <strong>Schneider</strong> <strong>Electric</strong>. All rights reserved.<br />
1 High Street<br />
North Andover, MA 01810 USA<br />
Phone: + 01 978 794 08000<br />
http://www.schneider-electric.com<br />
14<br />
Oc<strong>to</strong>ber 2009