AIS300 - Scheme of Work - Scholarly Commons Home
AIS300 - Scheme of Work - Scholarly Commons Home
AIS300 - Scheme of Work - Scholarly Commons Home
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
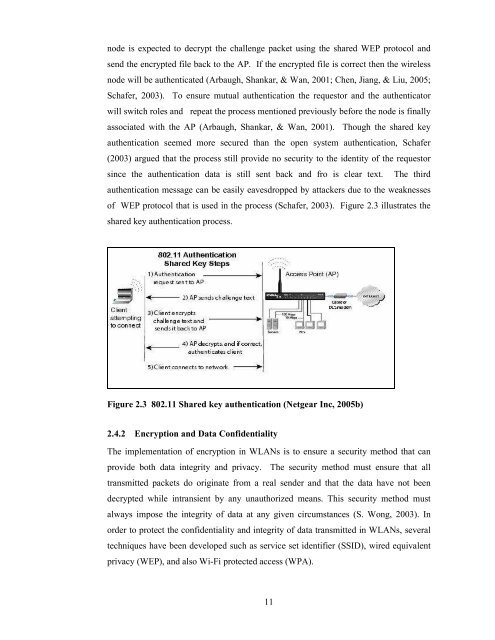
node is expected to decrypt the challenge packet using the shared WEP protocol and<br />
send the encrypted file back to the AP. If the encrypted file is correct then the wireless<br />
node will be authenticated (Arbaugh, Shankar, & Wan, 2001; Chen, Jiang, & Liu, 2005;<br />
Schafer, 2003). To ensure mutual authentication the requestor and the authenticator<br />
will switch roles and repeat the process mentioned previously before the node is finally<br />
associated with the AP (Arbaugh, Shankar, & Wan, 2001). Though the shared key<br />
authentication seemed more secured than the open system authentication, Schafer<br />
(2003) argued that the process still provide no security to the identity <strong>of</strong> the requestor<br />
since the authentication data is still sent back and fro is clear text. The third<br />
authentication message can be easily eavesdropped by attackers due to the weaknesses<br />
<strong>of</strong> WEP protocol that is used in the process (Schafer, 2003). Figure 2.3 illustrates the<br />
shared key authentication process.<br />
Figure 2.3 802.11 Shared key authentication (Netgear Inc, 2005b)<br />
2.4.2 Encryption and Data Confidentiality<br />
The implementation <strong>of</strong> encryption in WLANs is to ensure a security method that can<br />
provide both data integrity and privacy. The security method must ensure that all<br />
transmitted packets do originate from a real sender and that the data have not been<br />
decrypted while intransient by any unauthorized means. This security method must<br />
always impose the integrity <strong>of</strong> data at any given circumstances (S. Wong, 2003). In<br />
order to protect the confidentiality and integrity <strong>of</strong> data transmitted in WLANs, several<br />
techniques have been developed such as service set identifier (SSID), wired equivalent<br />
privacy (WEP), and also Wi-Fi protected access (WPA).<br />
11