AIS300 - Scheme of Work - Scholarly Commons Home
AIS300 - Scheme of Work - Scholarly Commons Home
AIS300 - Scheme of Work - Scholarly Commons Home
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
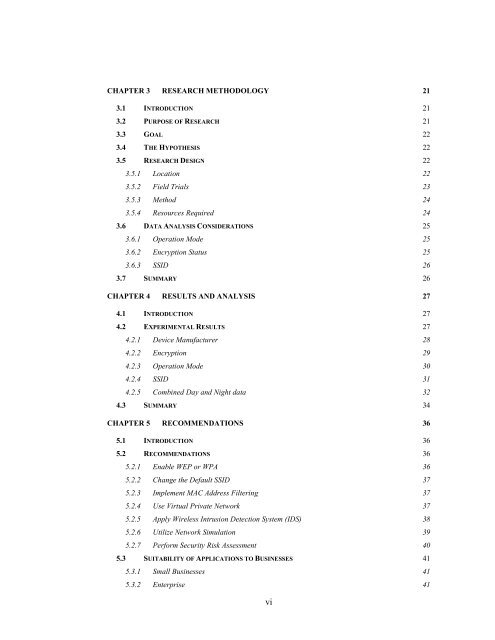
CHAPTER 3 RESEARCH METHODOLOGY 21<br />
3.1 INTRODUCTION 21<br />
3.2 PURPOSE OF RESEARCH 21<br />
3.3 GOAL 22<br />
3.4 THE HYPOTHESIS 22<br />
3.5 RESEARCH DESIGN 22<br />
3.5.1 Location 22<br />
3.5.2 Field Trials 23<br />
3.5.3 Method 24<br />
3.5.4 Resources Required 24<br />
3.6 DATA ANALYSIS CONSIDERATIONS 25<br />
3.6.1 Operation Mode 25<br />
3.6.2 Encryption Status 25<br />
3.6.3 SSID 26<br />
3.7 SUMMARY 26<br />
CHAPTER 4 RESULTS AND ANALYSIS 27<br />
4.1 INTRODUCTION 27<br />
4.2 EXPERIMENTAL RESULTS 27<br />
4.2.1 Device Manufacturer 28<br />
4.2.2 Encryption 29<br />
4.2.3 Operation Mode 30<br />
4.2.4 SSID 31<br />
4.2.5 Combined Day and Night data 32<br />
4.3 SUMMARY 34<br />
CHAPTER 5 RECOMMENDATIONS 36<br />
5.1 INTRODUCTION 36<br />
5.2 RECOMMENDATIONS 36<br />
5.2.1 Enable WEP or WPA 36<br />
5.2.2 Change the Default SSID 37<br />
5.2.3 Implement MAC Address Filtering 37<br />
5.2.4 Use Virtual Private Network 37<br />
5.2.5 Apply Wireless Intrusion Detection System (IDS) 38<br />
5.2.6 Utilize Network Simulation 39<br />
5.2.7 Perform Security Risk Assessment 40<br />
5.3 SUITABILITY OF APPLICATIONS TO BUSINESSES 41<br />
5.3.1 Small Businesses 41<br />
5.3.2 Enterprise 41<br />
vi