ISO/IEC 21827
ISO/IEC 21827
ISO/IEC 21827
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
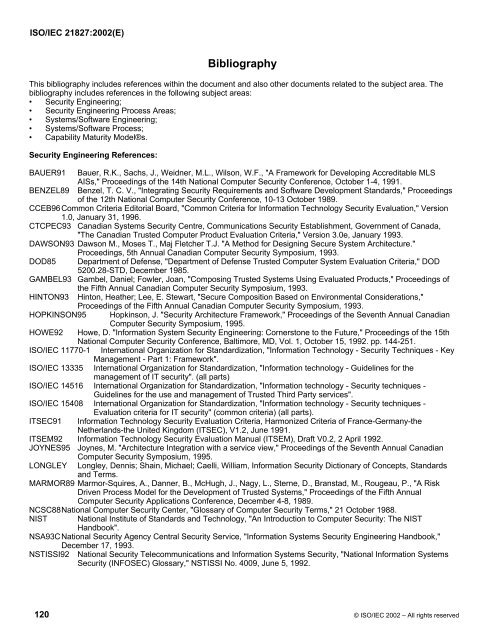
<strong>ISO</strong>/<strong>IEC</strong> <strong>21827</strong>:2002(E)<br />
Bibliography<br />
This bibliography includes references within the document and also other documents related to the subject area. The<br />
bibliography includes references in the following subject areas:<br />
• Security Engineering;<br />
• Security Engineering Process Areas;<br />
• Systems/Software Engineering;<br />
• Systems/Software Process;<br />
• Capability Maturity Model®s.<br />
Security Engineering References:<br />
BAUER91 Bauer, R.K., Sachs, J., Weidner, M.L., Wilson, W.F., "A Framework for Developing Accreditable MLS<br />
AISs," Proceedings of the 14th National Computer Security Conference, October 1-4, 1991.<br />
BENZEL89 Benzel, T. C. V., "Integrating Security Requirements and Software Development Standards," Proceedings<br />
of the 12th National Computer Security Conference, 10-13 October 1989.<br />
CCEB96Common Criteria Editorial Board, "Common Criteria for Information Technology Security Evaluation," Version<br />
1.0, January 31, 1996.<br />
CTCPEC93 Canadian Systems Security Centre, Communications Security Establishment, Government of Canada,<br />
"The Canadian Trusted Computer Product Evaluation Criteria," Version 3.0e, January 1993.<br />
DAWSON93 Dawson M., Moses T., Maj Fletcher T.J. "A Method for Designing Secure System Architecture."<br />
Proceedings, 5th Annual Canadian Computer Security Symposium, 1993.<br />
DOD85 Department of Defense, "Department of Defense Trusted Computer System Evaluation Criteria," DOD<br />
5200.28-STD, December 1985.<br />
GAMBEL93 Gambel, Daniel; Fowler, Joan, "Composing Trusted Systems Using Evaluated Products," Proceedings of<br />
the Fifth Annual Canadian Computer Security Symposium, 1993.<br />
HINTON93 Hinton, Heather; Lee, E. Stewart, "Secure Composition Based on Environmental Considerations,"<br />
Proceedings of the Fifth Annual Canadian Computer Security Symposium, 1993.<br />
HOPKINSON95 Hopkinson, J. "Security Architecture Framework," Proceedings of the Seventh Annual Canadian<br />
Computer Security Symposium, 1995.<br />
HOWE92 Howe, D. "Information System Security Engineering: Cornerstone to the Future," Proceedings of the 15th<br />
National Computer Security Conference, Baltimore, MD, Vol. 1, October 15, 1992. pp. 144-251.<br />
<strong>ISO</strong>/<strong>IEC</strong> 11770-1 International Organization for Standardization, "Information Technology - Security Techniques - Key<br />
Management - Part 1: Framework".<br />
<strong>ISO</strong>/<strong>IEC</strong> 13335 International Organization for Standardization, "Information technology - Guidelines for the<br />
management of IT security". (all parts)<br />
<strong>ISO</strong>/<strong>IEC</strong> 14516 International Organization for Standardization, "Information technology - Security techniques -<br />
Guidelines for the use and management of Trusted Third Party services".<br />
<strong>ISO</strong>/<strong>IEC</strong> 15408 International Organization for Standardization, "Information technology - Security techniques -<br />
Evaluation criteria for IT security" (common criteria) (all parts).<br />
ITSEC91 Information Technology Security Evaluation Criteria, Harmonized Criteria of France-Germany-the<br />
Netherlands-the United Kingdom (ITSEC), V1.2, June 1991.<br />
ITSEM92 Information Technology Security Evaluation Manual (ITSEM), Draft V0.2, 2 April 1992.<br />
JOYNES95 Joynes, M. "Architecture Integration with a service view," Proceedings of the Seventh Annual Canadian<br />
LONGLEY<br />
Computer Security Symposium, 1995.<br />
Longley, Dennis; Shain, Michael; Caelli, William, Information Security Dictionary of Concepts, Standards<br />
and Terms.<br />
MARMOR89 Marmor-Squires, A., Danner, B., McHugh, J., Nagy, L., Sterne, D., Branstad, M., Rougeau, P., "A Risk<br />
Driven Process Model for the Development of Trusted Systems," Proceedings of the Fifth Annual<br />
Computer Security Applications Conference, December 4-8, 1989.<br />
NCSC88National Computer Security Center, "Glossary of Computer Security Terms," 21 October 1988.<br />
NIST National Institute of Standards and Technology, "An Introduction to Computer Security: The NIST<br />
Handbook".<br />
NSA93CNational Security Agency Central Security Service, "Information Systems Security Engineering Handbook,"<br />
December 17, 1993.<br />
NSTISSI92<br />
National Security Telecommunications and Information Systems Security, "National Information Systems<br />
Security (INFOSEC) Glossary," NSTISSI No. 4009, June 5, 1992.<br />
120 © <strong>ISO</strong>/<strong>IEC</strong> 2002 – All rights reserved