You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
The contains a value between CSubTask.dwStartIP and CSubTask.dwEndIP,<br />
incremented by one for each subsequent packet transmitted. The value of , similarly,<br />
is between CSubTask.wStartPort and CSubTask.wEndPort, incremented by one for each new<br />
packet. If or exceed CSubTask.dwEndIP or CSubTask.<br />
wEndPort, respectively, their values begin again at CSubTask.dwStartIP and CSubTask.wStartPort,<br />
respectively. The value originates from the CSubTask.dwTargetIP. The<br />
value comes from the CSubTask.strActorRemarks value.<br />
Once constructed, CThreadAttack::PktAtk transmits the entire datagram to the target by calling<br />
CNetBase::Sendto. After transmitting the request, CThreadAttack::PktAtk will immediately generate<br />
another datagram in the same manner and repeat the process continuously until the termination<br />
signal occurs or the attack’s specified duration has been met.<br />
Note that while the previously defined attacks use CSubTask.dwStartIP/CSubTask.dwEndIP and<br />
CSubTask.wStartPort/CSubTask.wEndPort to specify fake source information, in the case of a DNS<br />
amplification attack it is necessary to have the fake source represent the real target of the attack. This<br />
is necessary because the DNS server will use the information to send back datagrams representing<br />
the answer to the query the attack generates.<br />
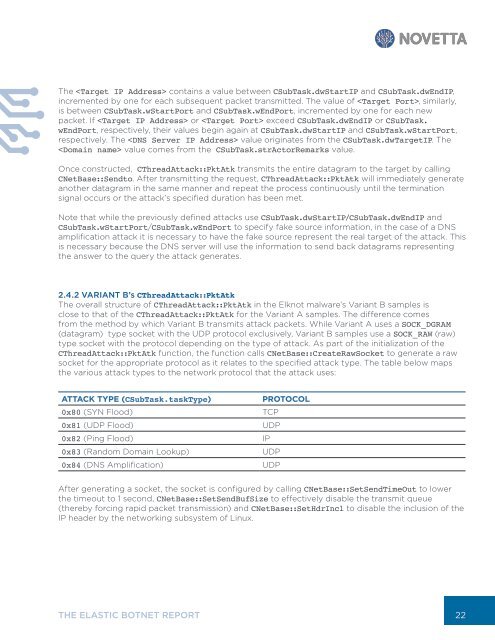
2.4.2 VARIANT B’s CThreadAttack::PktAtk<br />
The overall structure of CThreadAttack::PktAtk in the Elknot malware’s Variant B samples is<br />
close to that of the CThreadAttack::PktAtk for the Variant A samples. The difference comes<br />
from the method by which Variant B transmits attack packets. While Variant A uses a SOCK_DGRAM<br />
(datagram) type socket with the UDP protocol exclusively, Variant B samples use a SOCK_RAW (raw)<br />
type socket with the protocol depending on the type of attack. As part of the initialization of the<br />
CThreadAttack::PktAtk function, the function calls CNetBase::CreateRawSocket to generate a raw<br />
socket for the appropriate protocol as it relates to the specified attack type. The table below maps<br />
the various attack types to the network protocol that the attack uses:<br />
ATTACK TYPE (CSubTask.taskType)<br />
0x80 (SYN Flood)<br />
0x81 (UDP Flood)<br />
0x82 (Ping Flood)<br />
0x83 (Random Domain Lookup)<br />
0x84 (DNS Amplification)<br />
PROTOCOL<br />
TCP<br />
UDP<br />
IP<br />
UDP<br />
UDP<br />
After generating a socket, the socket is configured by calling CNetBase::SetSendTimeOut to lower<br />
the timeout to 1 second, CNetBase::SetSendBufSize to effectively disable the transmit queue<br />
(thereby forcing rapid packet transmission) and CNetBase::SetHdrIncl to disable the inclusion of the<br />
IP header by the networking subsystem of Linux.<br />
THE ELASTIC BOTNET REPORT<br />
22