Security - Telenor
Security - Telenor
Security - Telenor
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
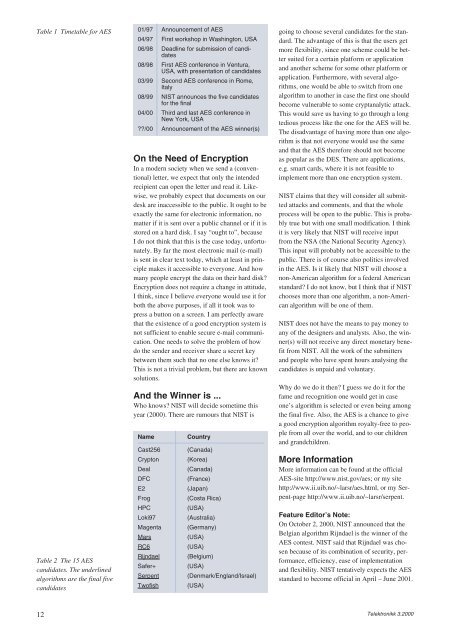
Table 1 Timetable for AES<br />
Table 2 The 15 AES<br />
candidates. The underlined<br />
algorithms are the final five<br />
candidates<br />
12<br />
01/97 Announcement of AES<br />
04/97 First workshop in Washington, USA<br />
06/98 Deadline for submission of candidates<br />
08/98 First AES conference in Ventura,<br />
USA, with presentation of candidates<br />
03/99 Second AES conference in Rome,<br />
Italy<br />
08/99 NIST announces the five candidates<br />
for the final<br />
04/00 Third and last AES conference in<br />
New York, USA<br />
??/00 Announcement of the AES winner(s)<br />
On the Need of Encryption<br />
In a modern society when we send a (conventional)<br />
letter, we expect that only the intended<br />
recipient can open the letter and read it. Likewise,<br />
we probably expect that documents on our<br />
desk are inaccessible to the public. It ought to be<br />
exactly the same for electronic information, no<br />
matter if it is sent over a public channel or if it is<br />
stored on a hard disk. I say “ought to”, because<br />
I do not think that this is the case today, unfortunately.<br />
By far the most electronic mail (e-mail)<br />
is sent in clear text today, which at least in principle<br />
makes it accessible to everyone. And how<br />
many people encrypt the data on their hard disk?<br />
Encryption does not require a change in attitude,<br />
I think, since I believe everyone would use it for<br />
both the above purposes, if all it took was to<br />
press a button on a screen. I am perfectly aware<br />
that the existence of a good encryption system is<br />
not sufficient to enable secure e-mail communication.<br />
One needs to solve the problem of how<br />
do the sender and receiver share a secret key<br />
between them such that no one else knows it?<br />
This is not a trivial problem, but there are known<br />
solutions.<br />
And the Winner is ...<br />
Who knows? NIST will decide sometime this<br />
year (2000). There are rumours that NIST is<br />
Name Country<br />
Cast256 (Canada)<br />
Crypton (Korea)<br />
Deal (Canada)<br />
DFC (France)<br />
E2 (Japan)<br />
Frog (Costa Rica)<br />
HPC (USA)<br />
Loki97 (Australia)<br />
Magenta (Germany)<br />
Mars (USA)<br />
RC6 (USA)<br />
Rijndael (Belgium)<br />
Safer+ (USA)<br />
Serpent (Denmark/England/Israel)<br />
Twofish (USA)<br />
going to choose several candidates for the standard.<br />
The advantage of this is that the users get<br />
more flexibility, since one scheme could be better<br />
suited for a certain platform or application<br />
and another scheme for some other platform or<br />
application. Furthermore, with several algorithms,<br />
one would be able to switch from one<br />
algorithm to another in case the first one should<br />
become vulnerable to some cryptanalytic attack.<br />
This would save us having to go through a long<br />
tedious process like the one for the AES will be.<br />
The disadvantage of having more than one algorithm<br />
is that not everyone would use the same<br />
and that the AES therefore should not become<br />
as popular as the DES. There are applications,<br />
e.g. smart cards, where it is not feasible to<br />
implement more than one encryption system.<br />
NIST claims that they will consider all submitted<br />
attacks and comments, and that the whole<br />
process will be open to the public. This is probably<br />
true but with one small modification. I think<br />
it is very likely that NIST will receive input<br />
from the NSA (the National <strong>Security</strong> Agency).<br />
This input will probably not be accessible to the<br />
public. There is of course also politics involved<br />
in the AES. Is it likely that NIST will choose a<br />
non-American algorithm for a federal American<br />
standard? I do not know, but I think that if NIST<br />
chooses more than one algorithm, a non-American<br />
algorithm will be one of them.<br />
NIST does not have the means to pay money to<br />
any of the designers and analysts. Also, the winner(s)<br />
will not receive any direct monetary benefit<br />
from NIST. All the work of the submitters<br />
and people who have spent hours analysing the<br />
candidates is unpaid and voluntary.<br />
Why do we do it then? I guess we do it for the<br />
fame and recognition one would get in case<br />
one’s algorithm is selected or even being among<br />
the final five. Also, the AES is a chance to give<br />
a good encryption algorithm royalty-free to people<br />
from all over the world, and to our children<br />
and grandchildren.<br />
More Information<br />
More information can be found at the official<br />
AES-site http://www.nist.gov/aes; or my site<br />
http://www.ii.uib.no/~larsr/aes.html, or my Serpent-page<br />
http://www.ii.uib.no/~larsr/serpent.<br />
Feature Editor’s Note:<br />
On October 2, 2000, NIST announced that the<br />
Belgian algorithm Rijndael is the winner of the<br />
AES contest. NIST said that Rijndael was chosen<br />
because of its combination of security, performance,<br />
efficiency, ease of implementation<br />
and flexibility. NIST tentatively expects the AES<br />
standard to become official in April – June 2001.<br />
Telektronikk 3.2000