Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
<strong>THE</strong> DOZER (AKA 7.7 DDOS) ATTACK<br />
The Dozer attack in July 2009 was one of the first attacks on South Korean targets that received international<br />
attention. DDOS bots were distributed with lists of sites to attack – notably various Korean websites covering<br />
government and bank functions, but also a great deal of US .gov, .mil and .com sites – including whitehouse.gov.<br />
This also involved wiping of hard disks of the infected computers.<br />
There is a known set of malware (7) connected with this incident.<br />
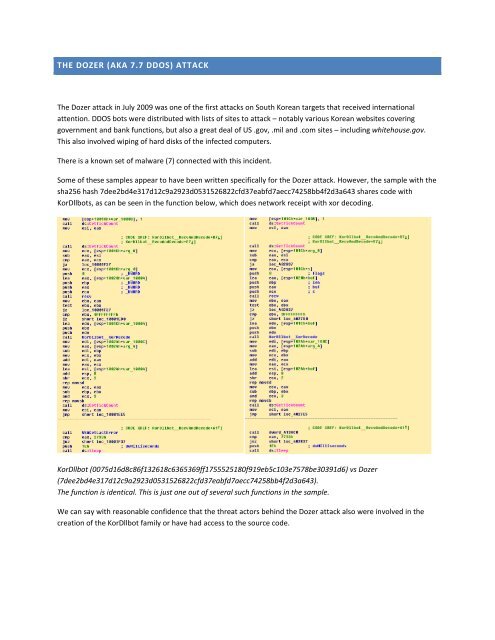
Some of these samples appear to have been written specifically for the Dozer attack. However, the sample with the<br />
sha256 hash 7dee2bd4e317d12c9a2923d0531526822cfd37eabfd7aecc74258bb4f2d3a643 shares code with<br />
KorDllbots, as can be seen in the function below, which does network receipt with xor decoding.<br />
KorDllbot (0075d16d8c86f132618c6365369ff1755525180f919eb5c103e7578be30391d6) vs Dozer<br />
(7dee2bd4e317d12c9a2923d0531526822cfd37eabfd7aecc74258bb4f2d3a643).<br />
The function is identical. This is just one out of several such functions in the sample.<br />
We can say with reasonable confidence that the threat actors behind the Dozer attack also were involved in the<br />
creation of the KorDllbot family or have had access to the source code.