Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
<strong>THE</strong> <strong>DESTOVER</strong> FAMILY<br />
<strong>DESTOVER</strong> “B076E058” BACKDOORS, FEB-JUNE 2014.<br />
This sub variant has been named “b076e058” based on the first portion of the RSA authentication key used for its<br />
server handshake.<br />
Most samples share the ChopString and XOR-A7 obfuscation functions with the Sony-associated malware<br />
eff542ac8e37db48821cb4e5a7d95c044fff27557763de3a891b40ebeb52cc55. They also declare API calls in the<br />
same way.<br />
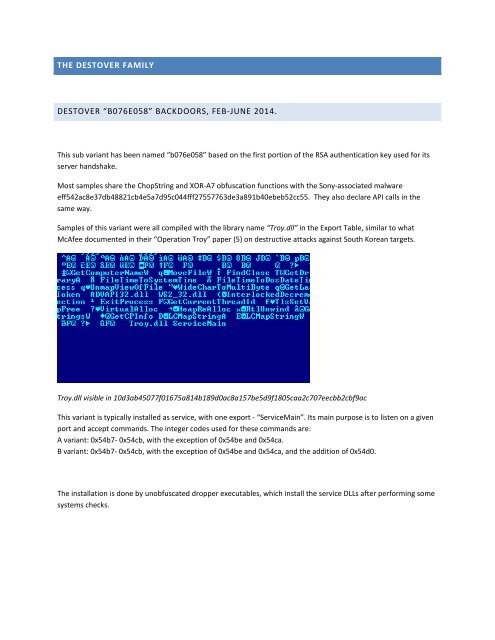
Samples of this variant were all compiled with the library name “Troy.dll” in the Export Table, similar to what<br />
McAfee documented in their “Operation Troy” paper (5) on destructive attacks against South Korean targets.<br />
Troy.dll visible in 10d3ab45077f01675a814b189d0ac8a157be5d9f1805caa2c707eecbb2cbf9ac<br />
This variant is typically installed as service, with one export - “ServiceMain”. Its main purpose is to listen on a given<br />
port and accept commands. The integer codes used for these commands are:<br />
A variant: 0x54b7- 0x54cb, with the exception of 0x54be and 0x54ca.<br />
B variant: 0x54b7- 0x54cb, with the exception of 0x54be and 0x54ca, and the addition of 0x54d0.<br />
The installation is done by unobfuscated dropper executables, which install the service DLLs after performing some<br />
systems checks.