You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>THE</strong> KORDLLBOT BACKDOOR FAMILY<br />
KorDllbot is a family of small/medium size trojans that usually are configured to be installed as services.<br />
Samples can vary a great deal in functionality - from just listening on a port and accepting commands, to harvesting<br />
data, to actively spreading over SMB. This functionality seems almost modular, using different encryption and<br />
encoding methods and different C&C command words. Build environment for the early generations was typically<br />
Visual Studio 6.<br />
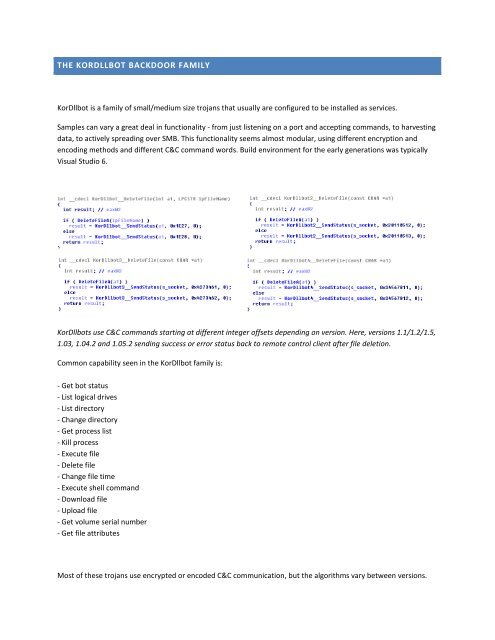
KorDllbots use C&C commands starting at different integer offsets depending on version. Here, versions 1.1/1.2/1.5,<br />
1.03, 1.04.2 and 1.05.2 sending success or error status back to remote control client after file deletion.<br />
Common capability seen in the KorDllbot family is:<br />
- Get bot status<br />
- List logical drives<br />
- List directory<br />
- Change directory<br />
- Get process list<br />
- Kill process<br />
- Execute file<br />
- Delete file<br />
- Change file time<br />
- Execute shell command<br />
- Download file<br />
- Upload file<br />
- Get volume serial number<br />
- Get file attributes<br />
Most of these trojans use encrypted or encoded C&C communication, but the algorithms vary between versions.