You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
IS NOW<br />
Combining thermal security cameras with video management systems.<br />
www.flir.com<br />
Untitled-20 1 18/02/16 10:18<br />
rules on breach reporting:<br />
Operators of essential services<br />
such as utilities, hospitals<br />
and the railways will be<br />
expected to meet new rules on<br />
network security – including reporting<br />
breaches within 72 hours – months<br />
before sector-specific guidance is<br />
issued by Government, according to a<br />
consultation document.<br />
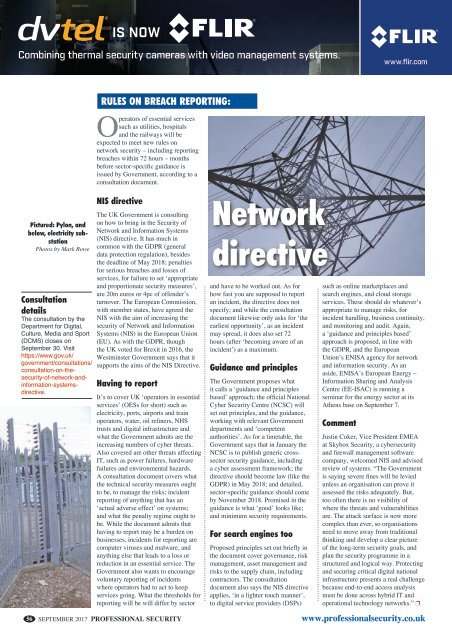
Pictured: Pylon, and<br />
below, electricity substation<br />
Photos by Mark Rowe<br />
Consultation<br />
details<br />
The consultation by the<br />
Department for Digital,<br />
Culture, Media and Sport<br />
(DCMS) closes on<br />
September 30. Visit<br />
https://www.gov.uk/<br />
government/consultations/<br />
consultation-on-thesecurity-of-network-andinformation-systemsdirective.<br />
56<br />
NIS directive<br />
The UK Government is consulting<br />
on how to bring in the Security of<br />
Network and Information Systems<br />
(NIS) directive. It has much in<br />
common with the GDPR (general<br />
data protection regulation), besides<br />
the deadline of May 2018; penalties<br />
for serious breaches and losses of<br />
services, for failure to set ‘appropriate<br />
and proportionate security measures’,<br />
are 20m euros or 4pc of offender’s<br />
turnover. The European Commission,<br />
with member states, have agreed the<br />
NIS with the aim of increasing the<br />
security of Network and Information<br />
Systems (NIS) in the European Union<br />
(EU). As with the GDPR, though<br />
the UK voted for Brexit in 2016, the<br />
Westminster Government says that it<br />
supports the aims of the NIS Directive.<br />
Having to report<br />
It’s to cover UK ‘operators in essential<br />
services’ (OESs for short) such as<br />
electricity, ports, airports and train<br />
operators, water, oil refiners, NHS<br />
trusts and digital infrastructure and<br />
what the Government admits are the<br />
increasing numbers of cyber threats.<br />
Also covered are other threats affecting<br />
IT, such as power failures, hardware<br />
failures and environmental hazards.<br />
A consultation document covers what<br />
the technical security measures ought<br />
to be, to manage the risks; incident<br />
reporting of anything that has an<br />
‘actual adverse effect’ on systems;<br />
and what the penalty regime ought to<br />
be. While the document admits that<br />
having to report may be a burden on<br />
businesses, incidents for reporting are<br />
computer viruses and malware, and<br />
anything else that leads to a loss or<br />
reduction in an essential service. The<br />
Government also wants to encourage<br />
voluntary reporting of incidents<br />
where operators had to act to keep<br />
services going. What the thresholds for<br />
reporting will be will differ by sector<br />
SEPTEMBER 2017 PROFESSIONAL SECURITY<br />
Network<br />
directive<br />
and have to be worked out. As for<br />
how fast you are supposed to report<br />
an incident, the directive does not<br />
specify; and while the consultation<br />
document likewise only asks for ‘the<br />
earliest opportunity’, as an incident<br />
may spread, it does also set 72<br />
hours (after ‘becoming aware of an<br />
incident’) as a maximum.<br />
Guidance and principles<br />
The Government proposes what<br />
it calls a ‘guidance and principles<br />
based’ approach; the official National<br />
Cyber Security Centre (NCSC) will<br />
set out principles, and the guidance,<br />
working with relevant Government<br />
departments and ‘competent<br />
authorities’. As for a timetable, the<br />
Government says that in January the<br />
NCSC is to publish generic crosssector<br />
security guidance, including<br />
a cyber assessment framework; the<br />
directive should become law (like the<br />
GDPR) in May 2018; and detailed,<br />
sector-specific guidance should come<br />
by November 2018. Promised in the<br />
guidance is what ‘good’ looks like;<br />
and minimum security requirements.<br />
For search engines too<br />
Proposed principles set out briefly in<br />
the document cover governance, risk<br />
management, asset management and<br />
risks to the supply chain, including<br />
contractors. The consultation<br />
document also says the NIS directive<br />
applies, ‘in a lighter touch manner’,<br />
to digital service providers (DSPs)<br />
such as online marketplaces and<br />
search engines, and cloud storage<br />
services. These should do whatever’s<br />
appropriate to manage risks, for<br />
incident handling, business continuity,<br />
and monitoring and audit. Again,<br />
a ‘guidance and principles based’<br />
approach is proposed, in line with<br />
the GDPR, and the European<br />
Union’s ENISA agency for network<br />
and information security. As an<br />
aside, ENISA’s European Energy –<br />
Information Sharing and Analysis<br />
Centre (EE-ISAC) is running a<br />
seminar for the energy sector at its<br />
Athens base on September 7.<br />
Comment<br />
Justin Coker, Vice President EMEA<br />
at Skybox Security, a cybersecurity<br />
and firewall management software<br />
company, welcomed NIS and advised<br />
review of systems. “The Government<br />
is saying severe fines will be levied<br />
unless an organisation can prove it<br />
assessed the risks adequately. But,<br />
too often there is no visibility of<br />
where the threats and vulnerabilities<br />
are. The attack surface is now more<br />
complex than ever, so organisations<br />
need to move away from traditional<br />
thinking and develop a clear picture<br />
of the long-term security goals, and<br />
plan the security programme in a<br />
structured and logical way. Protecting<br />
and securing critical digital national<br />
infrastructure presents a real challenge<br />
because end-to-end access analysis<br />
must be done across hybrid IT and<br />
operational technology networks.” p<br />
www.professionalsecurity.co.uk