International Cyber Terrorism
International Cyber Terrorism
International Cyber Terrorism
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
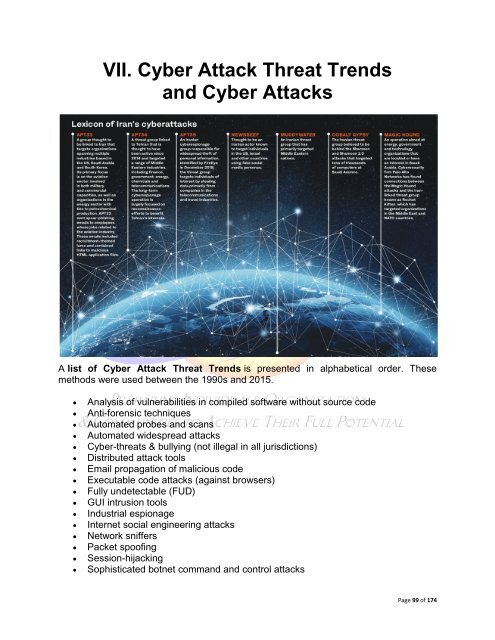
VII. <strong>Cyber</strong> Attack Threat Trends<br />
and <strong>Cyber</strong> Attacks<br />
A list of <strong>Cyber</strong> Attack Threat Trends is presented in alphabetical order. These<br />
methods were used between the 1990s and 2015.<br />
• Analysis of vulnerabilities in compiled software without source code<br />
• Anti-forensic techniques<br />
• Automated probes and scans<br />
• Automated widespread attacks<br />
• <strong>Cyber</strong>-threats & bullying (not illegal in all jurisdictions)<br />
• Distributed attack tools<br />
• Email propagation of malicious code<br />
• Executable code attacks (against browsers)<br />
• Fully undetectable (FUD)<br />
• GUI intrusion tools<br />
• Industrial espionage<br />
• Internet social engineering attacks<br />
• Network sniffers<br />
• Packet spoofing<br />
• Session-hijacking<br />
• Sophisticated botnet command and control attacks<br />
Page 99 of 174