Hot Topics - Messmer The Brain House
Hot Topics - Messmer The Brain House
Hot Topics - Messmer The Brain House
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Mission organization<br />
Putting a lock on security<br />
BY JIM PORELL<br />
This just in: Another tape with thousands<br />
of consumers’ personal data was lost off the<br />
back of a truck. In a related story, a new<br />
Trojan horse has been detected that has<br />
given hackers access to incredible amounts<br />
of business information. Fear and trepidation<br />
ensue for the online consumer. Brand<br />
images and value are lost based on perceived<br />
mismanagement of security and privacy. Each<br />
day, the complexity of securing a business<br />
seems more challenging than the day before.<br />
Chaos reigns in the complexity of<br />
IT infrastructures<br />
Fifty years ago, monolithic computers were<br />
introduced with punch cards and tape<br />
drives to address data processing needs.<br />
<strong>The</strong>y took up a huge, physically secured<br />
raised floor with tremendous cooling and<br />
energy needs. <strong>The</strong> capabilities of those<br />
1950’s era computers are less than the<br />
processing and storage capabilities of<br />
the iPod today. In fact, the evolution of<br />
laptops and PDAs has created a portable<br />
computing infrastructure that has<br />
eliminated most of the physical security<br />
value of the “glass house” environments of<br />
the past.<br />
Today the Internet and the complexity<br />
of offerings within Windows ® and Linux<br />
desktops have created additional security<br />
exposures. Many of the tried and true<br />
mainframe security capabilities no longer<br />
appear relevant to this on demand world.<br />
What’s a business supposed to do to<br />
combat these losses? Well, panic is not one<br />
of the actions, though sometimes it seems<br />
that way.<br />
Infrastructure simplification<br />
Many times, a business will look at each<br />
server type, individually, for managing<br />
security. <strong>The</strong> mainframe team operates<br />
independently from the desktop team,<br />
which is independent of the networking<br />
team. Yet, when all these systems are<br />
interconnected, they’re really overseeing<br />
an enterprise view of security or just a<br />
collection of ill fitted piece parts? In a<br />
security conscious business, looking at the<br />
workflow, from end to end, can yield some<br />
simplifying assumptions that will reduce<br />
operational risk. It will be combinations<br />
of virtualization, open standards and<br />
collaboration across communities that can<br />
help the business simplify.<br />
4 February 2006 z/OS HOT TOPICS Newsletter, Issue 14<br />
Avoiding tortured data flow<br />
In many enterprises, managing the<br />
personally identifiable information<br />
associated with a consumer is paramount<br />
to maintaining a successful brand image.<br />
New government regulations provide<br />
penalties and/or costly actions for the<br />
inadvertent or unauthorized disclosure of<br />
such information.<br />
So how can a business avoid that risk?<br />
Well, the first thing to do is look at how<br />
many copies of the data exist and examine<br />
the overall workflow. In the client/server<br />
era, with all the cheap computing out<br />
there, it seemed that copying the data<br />
or moving it to the applications was cost<br />
effective.<br />
Now, in the on demand and privacy<br />
conscious world, bringing the applications<br />
to the data can be more economically<br />
feasible. <strong>The</strong>re will certainly be copies of<br />
data that can’t be avoided.<br />
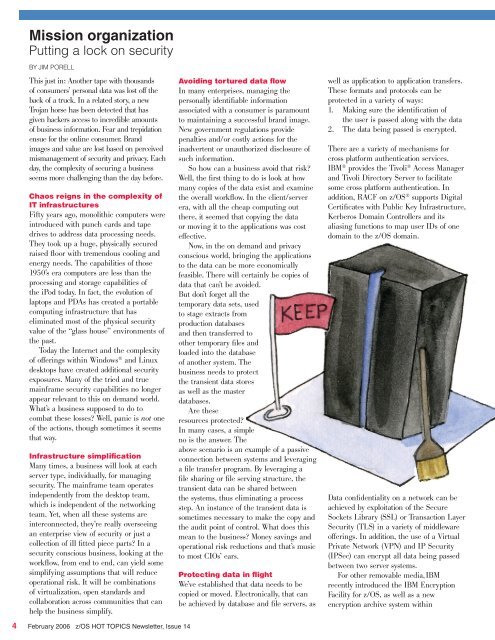
But don’t forget all the<br />
temporary data sets, used<br />
to stage extracts from<br />
production databases<br />
and then transferred to<br />
other temporary files and<br />
loaded into the database<br />
of another system. <strong>The</strong><br />
business needs to protect<br />
the transient data stores<br />
as well as the master<br />
databases.<br />
Are these<br />
resources protected?<br />
In many cases, a simple<br />
no is the answer. <strong>The</strong><br />
above scenario is an example of a passive<br />
connection between systems and leveraging<br />
a file transfer program. By leveraging a<br />
file sharing or file serving structure, the<br />
transient data can be shared between<br />
the systems, thus eliminating a process<br />
step. An instance of the transient data is<br />
sometimes necessary to make the copy and<br />
the audit point of control. What does this<br />
mean to the business? Money savings and<br />
operational risk reductions and that’s music<br />
to most CIOs’ ears.<br />
Protecting data in flight<br />
We’ve established that data needs to be<br />
copied or moved. Electronically, that can<br />
be achieved by database and file servers, as<br />
well as application to application transfers.<br />
<strong>The</strong>se formats and protocols can be<br />
protected in a variety of ways:<br />
1. Making sure the identification of<br />
the user is passed along with the data<br />
2. <strong>The</strong> data being passed is encrypted.<br />
<strong>The</strong>re are a variety of mechanisms for<br />
cross platform authentication services.<br />
IBM ® provides the Tivoli ® Access Manager<br />
and Tivoli Directory Server to facilitate<br />
some cross platform authentication. In<br />
addition, RACF on z/OS ® supports Digital<br />
Certificates with Public Key Infrastructure,<br />
Kerberos Domain Controllers and its<br />
aliasing functions to map user IDs of one<br />
domain to the z/OS domain.<br />
Data confidentiality on a network can be<br />
achieved by exploitation of the Secure<br />
Sockets Library (SSL) or Transaction Layer<br />
Security (TLS) in a variety of middleware<br />
offerings. In addition, the use of a Virtual<br />
Private Network (VPN) and IP Security<br />
(IPSec) can encrypt all data being passed<br />
between two server systems.<br />
For other removable media,IBM<br />
recently introduced the IBM Encryption<br />
Facility for z/OS, as well as a new<br />
encryption archive system within