- Page 2 and 3:
Newnes is an imprint of Elsevier 30
- Page 4 and 5:
vi Contents 4.8 Diversity Technique
- Page 6 and 7:
viii Contents Chapter 13: Managing
- Page 8 and 9:
x Contents 20.8 Summary ...........
- Page 10 and 11:
About the Authors Steven Arms (Chap
- Page 12 and 13:
About the Authors xv Timothy Stapko
- Page 14 and 15:
Part 1 Wireless Technology
- Page 16:
4 Chapter 1 Probably the most promi
- Page 21:
Wireless Fundamentals 9 standards a
- Page 24 and 25:
12 Chapter 1 classroom, provided th
- Page 26 and 27:
14 Chapter 1 for multimedia applica
- Page 28 and 29:
16 Chapter 1 is installed on their
- Page 30 and 31:
18 Chapter 1 ● Switching off the
- Page 32 and 33:
20 Chapter 1 Power Consumption The
- Page 34:
22 Chapter 2 Table 2.1 : The seven
- Page 37 and 38:
Wireless Network Logical Architectu
- Page 39 and 40:
Wireless Network Logical Architectu
- Page 41 and 42:
Wireless Network Logical Architectu
- Page 44 and 45:
32 Chapter 2 Layer 2 Data link laye
- Page 47 and 48:
Wireless Network Logical Architectu
- Page 49:
Wireless Network Logical Architectu
- Page 52 and 53:
40 Chapter 2 guidelines for impleme
- Page 56 and 57:
44 Chapter 2 while asynchronous tra
- Page 58:
46 Chapter 2 networks running other
- Page 68 and 69:
56 Chapter 3 3.3.2 Access Points Th
- Page 71 and 72:
Wireless Network Physical Architect
- Page 75 and 76:
Wireless Network Physical Architect
- Page 81 and 82:
Wireless Network Physical Architect
- Page 83 and 84:
Wireless Network Physical Architect
- Page 85:
Table 3.9 : Wireless MAN devices an
- Page 88 and 89:
CHAPTER 4 Radio Communication Basic
- Page 90 and 91:
Radio Communication Basics 79 In th
- Page 92:
Radio Communication Basics 81 Also
- Page 95 and 96:
84 Chapter 4 sight, diffraction gai
- Page 97 and 98:
86 Chapter 4 40 Path gain vs. Dista
- Page 99 and 100:
88 Chapter 4 environment, we distin
- Page 101 and 102:
90 Chapter 4 100 10 Percent error 1
- Page 103 and 104:
92 Chapter 4 It isn’t necessary t
- Page 105 and 106:
94 Chapter 4 Thus, a minimum of cir
- Page 107 and 108:
Urban 96 Chapter 4 Noise and its so
- Page 110 and 111:
Radio Communication Basics 99 1 0 1
- Page 112 and 113:
Radio Communication Basics 101 Tabl
- Page 114 and 115:
Radio Communication Basics 103 As l
- Page 116 and 117:
Radio Communication Basics 105 ●
- Page 118 and 119:
Radio Communication Basics 107 Thes
- Page 120 and 121:
Radio Communication Basics 109 cons
- Page 122 and 123:
Radio Communication Basics 111 Prea
- Page 124 and 125:
Radio Communication Basics 113 thes
- Page 126 and 127:
Radio Communication Basics 115 maxi
- Page 128 and 129:
Radio Communication Basics 117 Phas
- Page 130 and 131:
Radio Communication Basics 119 Sign
- Page 132 and 133:
Radio Communication Basics 121 freq
- Page 134 and 135:
Radio Communication Basics 123 Mixe
- Page 136 and 137:
Radio Communication Basics 125 show
- Page 138 and 139:
Radio Communication Basics 127 4.10
- Page 140 and 141:
Radio Communication Basics 129 In c
- Page 142 and 143:
Radio Communication Basics 131 Freq
- Page 144 and 145:
Radio Communication Basics 133 Ther
- Page 146 and 147:
Radio Communication Basics 135 4.11
- Page 148 and 149:
CHAPTER 5 Infrared Communication Ba
- Page 150:
Infrared Communication Basics 139 R
- Page 154 and 155:
CHAPTER 6 Wireless LAN Standards St
- Page 156:
Wireless LAN Standards 145 Standard
- Page 162 and 163:
Wireless LAN Standards 151 In passi
- Page 164 and 165:
Wireless LAN Standards 153 6.3 802.
- Page 166 and 167:
Wireless LAN Standards 155 Modulati
- Page 168 and 169:
Wireless LAN Standards 157 Table 6.
- Page 170:
Wireless LAN Standards 159 short da
- Page 174 and 175:
Wireless LAN Standards 163 6.4.2 Sp
- Page 176 and 177:
Wireless LAN Standards 165 Table 6.
- Page 178 and 179:
Wireless LAN Standards 167 6.4.3.2
- Page 180:
Wireless LAN Standards 169 Modulati
- Page 184 and 185:
Wireless LAN Standards 173 formed i
- Page 186 and 187:
CHAPTER 7 Wireless Sensor Networks
- Page 188 and 189:
Wireless Sensor Networks 177 wirele
- Page 190:
Wireless Sensor Networks 179 Figure
- Page 193:
182 Chapter 7 It is expected that o
- Page 196 and 197:
Wireless Sensor Networks 185 Additi
- Page 198 and 199:
Wireless Sensor Networks 187 a trai
- Page 200 and 201:
Wireless Sensor Networks 189 7. Mor
- Page 202 and 203:
CHAPTER 8 Attacks and Risks John Ri
- Page 204 and 205:
Attacks and Risks 195 In addition t
- Page 206 and 207:
Attacks and Risks 197 total complai
- Page 208 and 209:
Attacks and Risks 199 attributed to
- Page 210 and 211:
Attacks and Risks 201 3. receives,
- Page 212 and 213:
Attacks and Risks 203 undetected an
- Page 214 and 215:
Attacks and Risks 205 Step 3 : Iden
- Page 216 and 217:
Attacks and Risks 207 14. U.S. Depa
- Page 218 and 219:
210 Chapter 9 9.1 What Is Security?
- Page 220 and 221:
212 Chapter 9 Alice (manager) Bob (
- Page 222:
214 Chapter 9 the security policy s
- Page 226 and 227:
218 Chapter 9 Figure 9.4 : Enigma M
- Page 231 and 232:
Security Defined 223 form of authen
- Page 235 and 236:
Security Defined 227 to provide sec
- Page 238:
230 Chapter 9 key hidden from the p
- Page 241 and 242:
234 Chapter 10 Before we get starte
- Page 243 and 244:
236 Chapter 10 cryptography, using
- Page 245 and 246:
238 Chapter 10 A lot of cryptograph
- Page 247 and 248:
240 Chapter 10 suspicious involveme
- Page 249 and 250:
242 Chapter 10 to ensure that the p
- Page 251 and 252:
244 Chapter 10 that we may discover
- Page 253 and 254:
246 Chapter 10 10.5.1 SSH Sharing m
- Page 256 and 257:
Standardizing Security 249 is estab
- Page 258 and 259:
252 Chapter 11 was an internal proj
- Page 260:
254 Chapter 11 authentication, so j
- Page 264:
258 Chapter 11 SSL Session record H
- Page 268:
262 Chapter 11 The client uses the
- Page 274 and 275:
268 Chapter 11 11.6 SSL in Practice
- Page 276 and 277:
270 Chapter 12 at some specific alg
- Page 278 and 279:
272 Chapter 12 ● ● ● ● ●
- Page 280 and 281:
274 Chapter 12 The reason the mecha
- Page 282 and 283:
276 Chapter 12 // Finally, finalize
- Page 284 and 285:
278 Chapter 12 technology for at le
- Page 286 and 287:
280 Chapter 12 asymmetric) are much
- Page 288 and 289:
282 Chapter 12 and time. Once they
- Page 290 and 291:
284 Chapter 12 optimizations we wil
- Page 292 and 293:
286 Chapter 12 The trick works beca
- Page 294:
288 Chapter 12 The other common sym
- Page 297 and 298:
Cryptography 291 in RSA is less sim
- Page 299 and 300:
CHAPTER 13 Managing Access John Rit
- Page 301 and 302:
Managing Access 295 13.1.3.2 Accoun
- Page 303 and 304:
Managing Access 297 of the session
- Page 305 and 306:
Managing Access 299 process of look
- Page 307 and 308:
Managing Access 301 3. Deterrent, t
- Page 309 and 310:
Managing Access 303 administration
- Page 311 and 312:
Managing Access 305 Example of Elem
- Page 313 and 314:
Managing Access 307 the system bein
- Page 315 and 316:
Managing Access 309 13.2 Password M
- Page 317 and 318:
Managing Access 311 13.2.4 Password
- Page 319 and 320:
Managing Access 313 password is “
- Page 321 and 322:
Managing Access 315 2. U.S. Departm
- Page 323 and 324:
318 Chapter 14 The new legislation
- Page 325 and 326:
320 Chapter 14 of law enforcement a
- Page 327 and 328:
322 Chapter 14 Title IX, “ Improv
- Page 329 and 330:
324 Chapter 14 14.5.2 Obtaining Voi
- Page 331 and 332:
326 Chapter 14 [6] one applying to
- Page 333 and 334:
328 Chapter 14 computer networks; (
- Page 335 and 336:
330 Chapter 14 14.5.10 Deterrence a
- Page 337 and 338:
332 Chapter 14 now aggregate “ lo
- Page 339 and 340:
334 Chapter 14 computer forensic la
- Page 341 and 342:
336 Chapter 14 7. Known as the wire
- Page 343 and 344:
338 Chapter 15 and share enumerator
- Page 345 and 346:
340 Chapter 15 Because this individ
- Page 347 and 348:
342 Chapter 15 so on. Most of the s
- Page 349 and 350:
344 Chapter 15 15.4.1.4 AiroPeek NX
- Page 351 and 352:
346 Chapter 15 modify its content (
- Page 353 and 354:
348 Chapter 15 this data, the hacke
- Page 355 and 356:
350 Chapter 15 requesting access wi
- Page 357 and 358:
352 Chapter 15 corporate network fr
- Page 359 and 360:
354 Chapter 15 computer, especially
- Page 361 and 362:
356 Chapter 15 pigtail cables and v
- Page 363 and 364:
358 Chapter 15 One might think it w
- Page 365 and 366:
360 Chapter 15 Few WLAN discovery t
- Page 367 and 368:
CHAPTER 16 Security Policy George L
- Page 369 and 370:
Security Policy 365 Define a policy
- Page 371 and 372:
Part 3 Wireless Network Security
- Page 374 and 375:
Security in Traditional Wireless Ne
- Page 377 and 378:
374 Chapter 17 network. On the othe
- Page 379 and 380:
376 Chapter 17 Ki (128 bit), RAND (
- Page 381 and 382:
378 Chapter 17 protection. The abse
- Page 383 and 384:
380 Chapter 17 SRES to these challe
- Page 386:
Security in Traditional Wireless Ne
- Page 389 and 390:
386 Chapter 17 From a client’s (M
- Page 391 and 392:
388 Chapter 17 17.4.3 Authenticatio
- Page 393 and 394:
390 Chapter 17 Generate SQN Generat
- Page 395 and 396:
392 Chapter 17 Count-c Direction Co
- Page 397 and 398:
394 Chapter 17 Count-i Direction Co
- Page 399 and 400:
396 Chapter 17 MS SRNC VLR/SGSN 1.
- Page 401:
398 Chapter 17 provide confidential
- Page 405 and 406:
CHAPTER 18 Wireless LAN Security Pr
- Page 407 and 408:
Wireless LAN Security 405 retrospec
- Page 410 and 411:
408 Chapter 18 the former case, it
- Page 412:
410 Chapter 18 1 2 3 4 Station Acce
- Page 415 and 416:
Wireless LAN Security 413 18.4.5 Ps
- Page 417 and 418:
Wireless LAN Security 415 RC4 encry
- Page 419 and 420:
Wireless LAN Security 417 key-strea
- Page 421 and 422:
Wireless LAN Security 419 Frame hea
- Page 423 and 424:
Wireless LAN Security 421 with (or
- Page 425 and 426: Wireless LAN Security 423 The Wi-Fi
- Page 427 and 428: Wireless LAN Security 425 WEP WPA (
- Page 429 and 430: Wireless LAN Security 427 TSC/IV hi
- Page 434 and 435: 432 Chapter 18 a common theme in mo
- Page 436: 434 Chapter 18 Therefore, TKIP uses
- Page 439 and 440: Wireless LAN Security 437 designing
- Page 441: Wireless LAN Security 439 To summar
- Page 445 and 446: Wireless LAN Security 443 more than
- Page 447: CHAPTER 19 Security in Wireless Ad
- Page 450 and 451: 448 Chapter 19 ● ● ● ● Conc
- Page 454 and 455: 452 Chapter 19 is optional. However
- Page 456 and 457: 454 Chapter 19 HigherLayer_KeyEst.
- Page 458 and 459: 456 Chapter 19 Device A: Verifier D
- Page 460 and 461: 458 Chapter 19 The process of gener
- Page 462 and 463: 460 Chapter 19 less than 128 bits.
- Page 464 and 465: 462 Chapter 19 identity it is clami
- Page 466 and 467: 464 Chapter 19 Device A: Master Dev
- Page 468 and 469: 466 Chapter 19 Initialize key strea
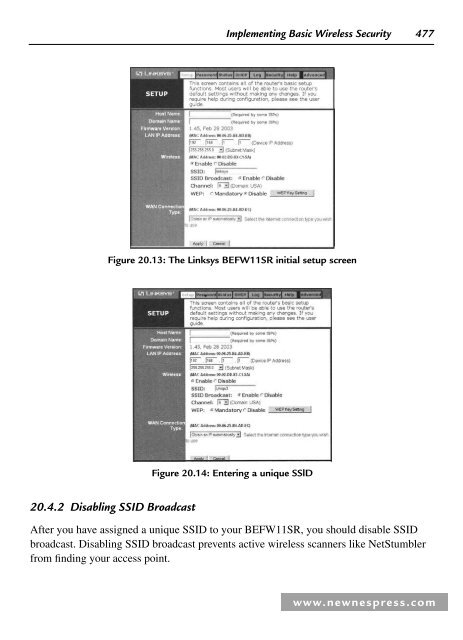
- Page 470 and 471: 468 Chapter 20 Figure 20.1 : The Li
- Page 472 and 473: 470 Chapter 20 Figure 20.3 : The ad
- Page 474 and 475: 472 Chapter 20 Figure 20.6 : The WE
- Page 480 and 481: 478 Chapter 20 Figure 20.15 : Disab
- Page 482 and 483: 480 Chapter 20 Figure 20.18 : The a
- Page 484 and 485: 482 Chapter 20 Figure 20.22 : The L
- Page 486 and 487: 484 Chapter 20 Figure 20.25 : Enabl
- Page 488 and 489: 486 Chapter 20 Figure 20.28 : The w
- Page 490 and 491: 488 Chapter 20 Figure 20.31 : The D
- Page 492 and 493: 490 Chapter 20 Figure 20.35 : Requi
- Page 494 and 495: 492 Chapter 20 Figure 20.39 : The M
- Page 496 and 497: 494 Chapter 20 Figure 20.43 : The W
- Page 498 and 499: 496 Chapter 20 Figure 20.45 : The c
- Page 500 and 501: 498 Chapter 20 Figure 20.49 : Enter
- Page 502 and 503: 500 Chapter 20 Figure 20.51 : Set t
- Page 504 and 505: 502 Chapter 20 ● ● ● broadcas
- Page 506 and 507: 504 Chapter 21 Figure 21.1 : The DI
- Page 508 and 509: 506 Chapter 21 Damage & Defense Kno
- Page 510 and 511: 508 Chapter 21 Figure 21.7 : The wi
- Page 512 and 513: 510 Chapter 21 Figure 21.11 : WPA C
- Page 514 and 515: 512 Chapter 21 SSL provides the thr
- Page 516 and 517: 514 Chapter 21 21.3.1 Installing Do
- Page 518 and 519: 516 Chapter 21 Figure 21.15 : Makin
- Page 520 and 521: 518 Chapter 21 Figure 21.18 : Loggi
- Page 522 and 523: 520 Chapter 21 Figure 21.21 : Chang
- Page 524 and 525: 522 Chapter 21 Figure 21.24 : Creat
- Page 526 and 527:
524 Chapter 21 4. Place the dolphin
- Page 528 and 529:
526 Chapter 21 can provide. The W-R
- Page 530 and 531:
528 Chapter 21 Figure 21.30 : Deact
- Page 532 and 533:
530 Chapter 21 Figure 21.34 : The I
- Page 534 and 535:
532 Chapter 21 Figure 21.37 : The r
- Page 536 and 537:
534 Chapter 21 Figure 21.41 : Selec
- Page 538 and 539:
536 Chapter 21 Figure 21.44 : The c
- Page 540 and 541:
538 Chapter 21 21.5.1 LEAP Features
- Page 542 and 543:
540 Chapter 21 Tools and Traps Noth
- Page 544 and 545:
542 Chapter 21 Figure 21.47 : Choos
- Page 546 and 547:
544 Chapter 21 Figure 21.50 : Confi
- Page 548 and 549:
546 Chapter 21 password, click the
- Page 550 and 551:
548 Chapter 21 Figure 21.57 : Confi
- Page 552 and 553:
550 Chapter 21 Figure 21.61 : Confi
- Page 554 and 555:
552 Chapter 21 Figure 21.64 : Loggi
- Page 556 and 557:
554 Chapter 21 Figure 21.68 : Addin
- Page 558 and 559:
556 Chapter 21 ● 802.1X. Provides
- Page 560 and 561:
558 Chapter 21 ● with a challenge
- Page 562 and 563:
560 Chapter 21 21.6.2.4 Advantages
- Page 564 and 565:
562 Chapter 21 the Certificates sna
- Page 566 and 567:
564 Chapter 21 Figure 21.71 : Certi
- Page 568 and 569:
566 Chapter 21 Figure 21.73 : Choos
- Page 570 and 571:
568 Chapter 21 Figure 21.74 : Reque
- Page 572 and 573:
570 Chapter 21 There are a number o
- Page 574 and 575:
572 Chapter 21 Figure 21.77 : Addin
- Page 576 and 577:
574 Chapter 21 Figure 21.79 : Addin
- Page 578 and 579:
576 Chapter 21 environment. A prima
- Page 580 and 581:
578 Chapter 21 Figure 21.83 : Confi
- Page 582 and 583:
580 Chapter 21 authenticated by an
- Page 584 and 585:
582 Chapter 21 21.8.5 Understanding
- Page 586 and 587:
CHAPTER 22 Home Network Security To
- Page 588 and 589:
Home Network Security 587 Wireless
- Page 590 and 591:
Home Network Security 589 802.16e,
- Page 592 and 593:
Home Network Security 591 new wirel
- Page 594 and 595:
Home Network Security 593 Figure 22
- Page 596 and 597:
Home Network Security 595 22.3.7 Us
- Page 598 and 599:
Home Network Security 597 22.4.1 Ve
- Page 600 and 601:
Home Network Security 599 22.4.6 Us
- Page 602 and 603:
CHAPTER 23 Wireless Embedded System
- Page 605 and 606:
604 Chapter 23 One of the largest b
- Page 607 and 608:
606 Chapter 23 enterprise networks,
- Page 609 and 610:
608 Chapter 23 will likely need to
- Page 611:
610 Chapter 23 It should suffice fo
- Page 615 and 616:
614 Chapter 23 reasons, ZigBee will
- Page 617 and 618:
616 Chapter 24 ● ● ● ● ●
- Page 619 and 620:
618 Chapter 24 Figure 24.1 : Variou
- Page 621 and 622:
620 Chapter 24 IFF has expanded sin
- Page 623 and 624:
622 Chapter 24 Tools and Traps …
- Page 626 and 627:
RFID Security 625 where λ is the w
- Page 628:
RFID Security 627 The data carried
- Page 631 and 632:
630 Chapter 24 Figure 24.1 shows th
- Page 633 and 634:
632 Chapter 24 The ExxonMobil Speed
- Page 635 and 636:
634 Chapter 24 Figure 24.10 : E-ZPa
- Page 637 and 638:
636 Chapter 24 Spoofing Spoofi ng a
- Page 639 and 640:
638 Chapter 24 Figure 24.11 : RF du
- Page 641 and 642:
640 Chapter 24 person at risk if th
- Page 643 and 644:
642 Chapter 24 conveyor belt, they
- Page 645 and 646:
644 Chapter 24 Let’s look back at
- Page 647 and 648:
646 Chapter 24 24.9.3 Threat Manage
- Page 649 and 650:
648 Chapter 24 of the potential att
- Page 651 and 652:
650 Appendix A Two new wireless sec
- Page 653 and 654:
652 Appendix A APs is still in the
- Page 655 and 656:
654 Appendix A Author:_____________
- Page 657 and 658:
656 Appendix A 1.0 Overview Informa
- Page 659 and 660:
658 Appendix A Employees must use e
- Page 661 and 662:
660 Appendix A ● ● ● ● ●
- Page 663 and 664:
662 Appendix A this policy and asso
- Page 665 and 666:
664 Appendix A 7. In networks where
- Page 667 and 668:
666 Appendix A A.6 ABC Inc. InfoSec
- Page 669 and 670:
668 Appendix A 3. DMZs should be in
- Page 671 and 672:
670 Appendix A 7.0 Revision History
- Page 673 and 674:
672 Appendix A 6.0 Exceptions Excep
- Page 675 and 676:
674 Appendix A and is responsible f
- Page 677 and 678:
676 Appendix A A.9 ABC Inc. InfoSec
- Page 679 and 680:
678 Appendix A 7. Frame Relay must
- Page 681 and 682:
680 Appendix A 6.0 Exceptions Excep
- Page 683 and 684:
682 Appendix A 5.0 Definitions 6.0
- Page 685 and 686:
684 Appendix A 4.0 Enforcement Any
- Page 687 and 688:
686 Appendix A 5.0 Definitions User
- Page 689 and 690:
688 Appendix A ● ● ● ● ●
- Page 691 and 692:
690 Appendix A or management, and w
- Page 693 and 694:
692 Appendix A ● The password is
- Page 695 and 696:
694 Appendix A ● ● should suppo
- Page 697 and 698:
696 Appendix A 3.0 Policy 3.1 Gener
- Page 699 and 700:
698 Appendix A Hash: An algorithmic
- Page 701 and 702:
700 Appendix A 7.0 Revision History
- Page 703 and 704:
702 Appendix B Application Gateway:
- Page 705 and 706:
704 Appendix B device that is confi
- Page 707 and 708:
706 Appendix B HTML: HTML is the ba
- Page 709 and 710:
708 Appendix B IP Spoofing: IP spoo
- Page 711 and 712:
710 Appendix B Packet sniffing is u
- Page 713 and 714:
712 Appendix B SMTP: Simple Mail Tr
- Page 715 and 716:
Index A 802.11 enhancements , 159 m
- Page 717 and 718:
Index 717 fraud and theft , 194-5 i
- Page 719 and 720:
Index 719 I i.Link , see FireWire I
- Page 721 and 722:
Index 721 Path loss , 84-6 Payload
- Page 723 and 724:
Index 723 Threat and target identif
- Page 725 and 726:
Index 725 routing , 28-9 operating