AM2: Protected-Mode Programming
AM2: Protected-Mode Programming
AM2: Protected-Mode Programming
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
ECP4166: Advanced Microprocessors<br />
<strong>AM2</strong><br />
Figure 1.1: Evaluating the Postfix Expression 5 6 * 4 – .<br />
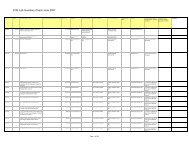
Table 1.1 contains some examples of translating infix to equivalent postfix expressions.<br />
Table 1.1 Infix to Postfix Examples<br />
Infix<br />
Postfix<br />
A + B A B +<br />
(A - B) / D A B - D /<br />
(A + B) * (C + D) A B + C D + *<br />
((A + B) / C) * (E - F) AB + C / EF - *<br />
1.2 FPU Data Registers<br />
The FPU has eight individually addressable 80-bit data registers named R0 through R7 (see<br />
Figure 2). Together, they are called a register stack. A three-bit field named TOP in the FPU<br />
status word identifies the register number that is currently the top of the stack. In Figure 1.2,<br />
for example, TOP equals binary 011, identifying R3 as the top of the stack. This stack<br />
location is also known as ST(0) (or simply ST) when writing floating-point instructions. The<br />
last register is ST(7).<br />
Figure 1.2: Floating-Point Data Register Stack.<br />
As we might expect, a push operation (also called load) decrements TOP by 1 and copies an<br />
operand into the register identified as ST(0). If TOP equals 0 before a push, TOP wraps<br />
around to register R7. A pop operation (also called store) copies the data at ST(0) into an<br />
operand, then adds 1 to TOP. If TOP equals 7 before the pop, it wraps around to register R0.<br />
Page 2 of 14