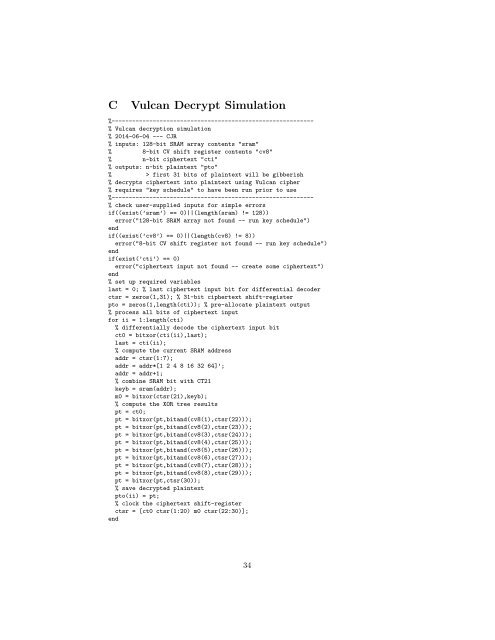
C Vulcan Decrypt Simulation %----------------------------------------------------------- % Vulcan decryption simulation % 2014-06-04 --- CJR % inputs: 128-bit SRAM array contents "sram" % 8-bit CV shift register contents "cv8" % n-bit ciphertext "cti" % outputs: n-bit plaintext "pto" % > first 31 bits of plaintext will be gibberish % decrypts ciphertext into plaintext using Vulcan cipher % requires "key schedule" to have been run prior to use %----------------------------------------------------------- % check user-supplied inputs for simple errors if((exist(’sram’) == 0)||(length(sram) != 128)) error("128-bit SRAM array not found -- run key schedule") end if((exist(’cv8’) == 0)||(length(cv8) != 8)) error("8-bit CV shift register not found -- run key schedule") end if(exist(’cti’) == 0) error("ciphertext input not found -- create some ciphertext") end % set up required variables last = 0; % last ciphertext input bit for differential decoder ctsr = zeros(1,31); % 31-bit ciphertext shift-register pto = zeros(1,length(cti)); % pre-allocate plaintext output % process all bits of ciphertext input for ii = 1:length(cti) % differentially decode the ciphertext input bit ct0 = bitxor(cti(ii),last); last = cti(ii); % compute the current SRAM address addr = ctsr(1:7); addr = addr*[1 2 4 8 16 32 64]’; addr = addr+1; % combine SRAM bit with CT21 keyb = sram(addr); m0 = bitxor(ctsr(21),keyb); % compute the XOR tree results pt = ct0; pt = bitxor(pt,bitand(cv8(1),ctsr(22))); pt = bitxor(pt,bitand(cv8(2),ctsr(23))); pt = bitxor(pt,bitand(cv8(3),ctsr(24))); pt = bitxor(pt,bitand(cv8(4),ctsr(25))); pt = bitxor(pt,bitand(cv8(5),ctsr(26))); pt = bitxor(pt,bitand(cv8(6),ctsr(27))); pt = bitxor(pt,bitand(cv8(7),ctsr(28))); pt = bitxor(pt,bitand(cv8(8),ctsr(29))); pt = bitxor(pt,ctsr(30)); % save decrypted plaintext pto(ii) = pt; % clock the ciphertext shift-register ctsr = [ct0 ctsr(1:20) m0 ctsr(22:30)]; end 34
D Vulcan Cryptanalysis Simulation %----------------------------------------------------------- % Vulcan <strong>cryptanalysis</strong> simulation % 2014-07-15 --- CJR % input: n-bit ciphertext "ct" % output: 71-bit cryptovariable "cv" % recovers Vulcan CV from ciphertext assuming all-0 plaintext %----------------------------------------------------------- % check user-supplied inputs for simple errors if(exist(’ct’) == 0) error("ciphertext not found -- create some ciphertext") end % table of 128-bit SRAM contents in terms of 64 CV bits (of 71-bit user CV) % each row represents the contents of the corresponding SRAM address from 000 to 127 % the columns are user CV bits v70 v69 v68 v67 ... v10 v09 v08 v05 % (note that rows containing more than a single 1 represent parity bits) % (note that user CV bits v07 v06 v04 v03 v02 v01 v00 are NOT stored in SRAM) sr = [... 1,0,1,1,1,0,1,0,1,0,0,1,1,1,0,1,1,0,1,0,1,0,0,0,0,1,1,1,0,1,0,0,... 1,1,1,0,1,1,1,0,1,1,1,1,0,0,0,0,0,0,0,1,1,0,0,0,0,0,1,1,1,0,1,0;... 0,1,0,1,0,1,0,1,1,0,1,1,1,0,0,1,0,1,0,1,1,0,0,1,1,1,0,0,1,0,0,1,... 1,1,0,0,1,1,1,1,1,1,1,0,0,0,0,1,0,0,0,1,0,0,0,0,1,1,1,0,0,1,0,1;... 0,0,1,1,0,0,0,1,0,1,1,1,1,1,0,1,0,1,0,1,0,0,1,0,1,1,1,0,0,0,1,1,... 1,1,1,0,0,0,0,1,0,0,1,1,1,0,1,1,0,0,0,1,1,0,0,1,1,1,1,1,0,0,0,0;... 1,0,1,0,1,0,1,0,1,0,1,1,0,1,1,1,0,1,0,1,0,0,1,0,0,1,0,0,0,0,0,1,... 0,0,1,0,1,0,0,0,0,0,1,1,0,1,1,0,1,1,1,1,1,1,0,0,0,1,0,0,0,0,0,1;... 0,1,0,0,0,0,1,0,1,1,1,0,1,0,1,0,1,1,1,0,1,1,0,0,1,1,0,0,0,1,1,1,... 0,1,0,1,0,0,1,0,0,0,1,1,1,1,1,1,0,0,0,1,0,0,1,1,1,1,1,0,0,0,1,0;... 0,0,1,0,1,0,1,0,1,0,0,1,0,1,1,1,0,0,0,1,0,0,1,1,1,1,1,1,1,1,1,0,... 0,1,0,1,1,0,1,0,1,0,0,1,0,1,1,1,0,1,0,0,0,1,0,0,0,1,0,1,1,1,0,0;... 1,1,1,0,1,1,1,1,1,1,1,0,0,0,0,1,0,0,0,0,0,1,0,0,1,1,1,1,0,1,1,0,... 1,0,1,0,1,1,1,0,1,0,0,1,0,1,0,1,1,1,1,0,0,1,0,0,1,0,1,1,1,0,0,0;... 0,1,1,0,0,0,1,0,0,0,0,0,0,1,0,1,1,0,1,0,0,1,0,1,1,1,0,0,1,1,0,1,... 0,1,0,0,1,0,0,0,0,1,0,0,0,0,0,0,1,1,0,1,0,0,1,1,1,1,0,0,0,0,1,0;... 1,0,0,0,0,0,0,1,0,1,0,1,0,1,1,1,1,1,0,1,0,0,0,1,1,0,1,0,1,1,1,0,... 0,0,1,1,0,1,1,0,0,0,1,1,0,1,1,1,0,0,1,0,0,0,1,1,1,1,0,1,0,1,1,0;... 1,0,1,0,0,0,1,0,1,0,0,1,1,1,1,0,1,0,0,0,1,0,0,1,0,0,0,0,0,0,1,1,... 0,0,1,0,1,1,1,0,1,0,1,0,1,0,0,0,0,0,0,0,1,0,0,0,1,1,0,0,1,0,0,1;... 0,1,0,1,0,0,0,1,0,0,1,1,1,1,0,0,0,0,1,0,1,1,1,0,1,1,0,1,1,1,0,0,... 1,0,1,1,0,1,1,1,0,1,1,0,0,1,1,0,1,0,1,0,1,0,0,0,0,0,1,0,1,0,1,1;... 0,0,0,0,0,0,0,1,1,0,1,1,1,0,1,1,1,0,0,0,1,1,1,0,0,0,1,1,1,0,1,1,... 1,1,0,0,0,1,1,0,1,1,1,0,0,0,0,0,1,1,0,1,1,0,1,1,0,1,1,1,0,0,0,1;... 1,1,0,1,1,1,1,1,0,1,0,1,0,0,1,0,0,0,0,0,1,0,0,0,1,1,1,0,1,1,0,1,... 1,1,0,1,1,1,0,1,0,1,1,0,0,0,1,0,1,1,1,0,1,1,0,1,0,1,1,0,0,0,0,1;... 0,1,0,0,1,1,0,1,0,0,1,1,0,0,1,1,0,1,0,0,0,0,0,0,1,1,0,0,0,0,1,0,... 0,1,1,0,1,0,0,1,1,1,0,0,0,0,0,1,0,1,1,1,1,1,0,1,0,0,0,0,0,0,0,0;... 1,1,0,0,0,0,0,0,0,0,0,1,1,0,0,1,0,0,0,0,1,0,1,1,1,0,1,1,1,1,1,0,... 0,0,0,0,0,0,1,0,1,1,0,0,0,0,0,0,1,0,0,0,0,1,1,1,1,0,0,1,0,1,1,0;... 1,1,0,1,1,0,0,1,0,1,0,1,0,1,1,1,0,0,0,1,1,1,0,0,1,1,1,0,0,1,1,1,... 1,1,1,0,0,0,0,0,0,1,1,0,0,1,0,1,1,0,1,1,1,1,0,0,1,0,1,0,0,0,0,0;... 0,0,0,0,0,1,1,0,0,0,1,0,1,1,1,1,1,0,1,0,1,0,1,0,0,1,0,1,1,1,0,0,... 0,1,1,1,1,1,0,0,0,0,1,0,0,1,1,1,0,1,1,0,0,0,1,1,0,0,1,1,1,1,1,0;... 0,0,0,1,1,0,1,1,0,0,1,0,1,0,1,0,1,1,1,0,0,0,1,1,1,0,0,1,1,1,0,0,... 1,1,1,1,1,1,0,0,0,0,0,0,1,1,0,0,1,0,1,1,0,1,1,1,1,0,0,1,0,1,0,0;... 1,1,1,1,1,1,1,1,1,0,1,0,0,0,0,0,1,1,1,1,1,0,1,0,0,1,1,1,0,1,1,0,... 1,0,1,1,0,0,1,1,1,0,1,0,0,0,0,1,0,0,0,0,1,0,0,1,0,0,1,1,1,0,0,1;... 0,1,1,1,0,0,0,0,1,0,0,1,0,1,1,1,1,1,0,1,1,0,1,0,0,0,0,0,1,0,1,0,... 35
- Page 1 and 2: Vulcan: A Proprietary Cipher of the
- Page 3 and 4: As a final comment concerning Motor
- Page 5 and 6: known how vulnerable this cipher ac
- Page 7 and 8: 7 Figure 3: SC76807 Die Shot
- Page 9 and 10: of the SC76807 in a later section,
- Page 11 and 12: At the far right side of the chip i
- Page 13 and 14: signal. The WE input on Pin 9 and t
- Page 15 and 16: its and are always set to 0 by the
- Page 17 and 18: 4 DVP Key Loader Based on our analy
- Page 19 and 20: 4.2 Reverse Engineering Understandi
- Page 21 and 22: 5.1 Key Schedule We created an Octa
- Page 23 and 24: plaintext bit (i.e. we are mounting
- Page 25 and 26: cryptovariable in real time solely
- Page 27 and 28: exposed, it would be enlightening i
- Page 29 and 30: [6] Motorola Encryption Topics, htt
- Page 31 and 32: % form 8-bit data word from 7 bits
- Page 33: B Vulcan Encrypt Simulation %------
- Page 37 and 38: 0,1,0,0,1,0,0,0,0,1,0,0,0,1,0,1,0,1
- Page 39 and 40: 0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0
- Page 41 and 42: c = bitxor(c,bitand(cv8(7),ctd(nn-2
- Page 43 and 44: E DVP Key Loader Firmware Disassemb
- Page 45 and 46: F09A : BD F1 C0 " " jsr $F1C0 put t
- Page 47 and 48: F166 : 5C "\" incb F167 : 20 F9 " "
- Page 49 and 50: F22C : CE FF 9D " " ldx #$FF9D Load
- Page 51 and 52: -----------------------------------
- Page 53 and 54: F3B9 : 81 04 " " cmpa #$04 F3BB : 2
- Page 55 and 56: F48B : 39 "9" rts -----------------
- Page 57 and 58: F553 : 39 "9" rts -----------------
- Page 59 and 60: F62C : 8E F8 E2 " " lds #$F8E2 tab:
- Page 61 and 62: F707 : 7E F9 10 "~ " jmp $F910 disp
- Page 63 and 64: F7CA : 97 82 " " staa PB F7CC : 96
- Page 65 and 66: F87F : 08 " " inx F880 : D6 74 " t"
- Page 67 and 68: F947 : 97 82 " " staa PB F949 : 88
- Page 69 and 70: FA05 : 5A "Z" decb FA06 : 26 F4 "&
- Page 71 and 72: FAE4 : 27 03 "’ " beq $FAE9 FAE6
- Page 73 and 74: FBC8 : 27 05 "’ " beq $FBCF . . .
- Page 75 and 76: FC80 : 01 " " nop FC81 : D6 74 " t"
- Page 77 and 78: FD31 : 20 08 " " bra $FD3B --------
- Page 79 and 80: . . . . . . . . . . . . . . . . FE0
- Page 81 and 82: FEAD : 27 04 "’ " beq $FEB3 FEAF
- Page 83 and 84: FF61 : BD F1 70 " p" jsr $F170 writ