vulcan-cryptanalysis
vulcan-cryptanalysis
vulcan-cryptanalysis
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
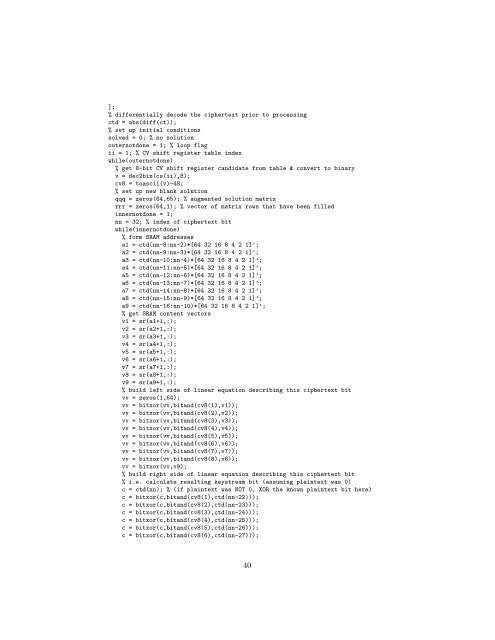
];<br />
% differentially decode the ciphertext prior to processing<br />
ctd = abs(diff(ct));<br />
% set up initial conditions<br />
solved = 0; % no solution<br />
outernotdone = 1; % loop flag<br />
ii = 1; % CV shift register table index<br />
while(outernotdone)<br />
% get 8-bit CV shift register candidate from table & convert to binary<br />
v = dec2bin(cs(ii),8);<br />
cv8 = toascii(v)-48;<br />
% set up new blank solution<br />
qqq = zeros(64,65); % augmented solution matrix<br />
rrr = zeros(64,1); % vector of matrix rows that have been filled<br />
innernotdone = 1;<br />
nn = 32; % index of ciphertext bit<br />
while(innernotdone)<br />
% form SRAM addresses<br />
a1 = ctd(nn-8:nn-2)*[64 32 16 8 4 2 1]’;<br />
a2 = ctd(nn-9:nn-3)*[64 32 16 8 4 2 1]’;<br />
a3 = ctd(nn-10:nn-4)*[64 32 16 8 4 2 1]’;<br />
a4 = ctd(nn-11:nn-5)*[64 32 16 8 4 2 1]’;<br />
a5 = ctd(nn-12:nn-6)*[64 32 16 8 4 2 1]’;<br />
a6 = ctd(nn-13:nn-7)*[64 32 16 8 4 2 1]’;<br />
a7 = ctd(nn-14:nn-8)*[64 32 16 8 4 2 1]’;<br />
a8 = ctd(nn-15:nn-9)*[64 32 16 8 4 2 1]’;<br />
a9 = ctd(nn-16:nn-10)*[64 32 16 8 4 2 1]’;<br />
% get SRAM content vectors<br />
v1 = sr(a1+1,:);<br />
v2 = sr(a2+1,:);<br />
v3 = sr(a3+1,:);<br />
v4 = sr(a4+1,:);<br />
v5 = sr(a5+1,:);<br />
v6 = sr(a6+1,:);<br />
v7 = sr(a7+1,:);<br />
v8 = sr(a8+1,:);<br />
v9 = sr(a9+1,:);<br />
% build left side of linear equation describing this ciphertext bit<br />
vv = zeros(1,64);<br />
vv = bitxor(vv,bitand(cv8(1),v1));<br />
vv = bitxor(vv,bitand(cv8(2),v2));<br />
vv = bitxor(vv,bitand(cv8(3),v3));<br />
vv = bitxor(vv,bitand(cv8(4),v4));<br />
vv = bitxor(vv,bitand(cv8(5),v5));<br />
vv = bitxor(vv,bitand(cv8(6),v6));<br />
vv = bitxor(vv,bitand(cv8(7),v7));<br />
vv = bitxor(vv,bitand(cv8(8),v8));<br />
vv = bitxor(vv,v9);<br />
% build right side of linear equation describing this ciphertext bit<br />
% i.e. calculate resulting keystream bit (assuming plaintext was 0)<br />
c = ctd(nn); % (if plaintext was NOT 0, XOR the known plaintext bit here)<br />
c = bitxor(c,bitand(cv8(1),ctd(nn-22)));<br />
c = bitxor(c,bitand(cv8(2),ctd(nn-23)));<br />
c = bitxor(c,bitand(cv8(3),ctd(nn-24)));<br />
c = bitxor(c,bitand(cv8(4),ctd(nn-25)));<br />
c = bitxor(c,bitand(cv8(5),ctd(nn-26)));<br />
c = bitxor(c,bitand(cv8(6),ctd(nn-27)));<br />
40