Understanding TCP/IP Model Internals and Interfaces
Understanding TCP/IP Model Internals and Interfaces
Understanding TCP/IP Model Internals and Interfaces
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
1508 <strong>Underst<strong>and</strong>ing</strong> <strong>TCP</strong>/<strong>IP</strong> <strong>Model</strong> <strong>Internals</strong> <strong>and</strong> <strong>Interfaces</strong><br />
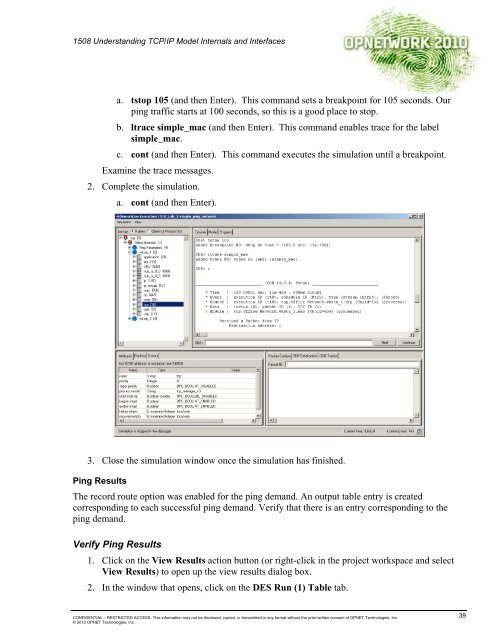
a. tstop 105 (<strong>and</strong> then Enter). This comm<strong>and</strong> sets a breakpoint for 105 seconds. Our<br />
ping traffic starts at 100 seconds, so this is a good place to stop.<br />
b. ltrace simple_mac (<strong>and</strong> then Enter). This comm<strong>and</strong> enables trace for the label<br />
simple_mac.<br />
c. cont (<strong>and</strong> then Enter). This comm<strong>and</strong> executes the simulation until a breakpoint.<br />
Examine the trace messages.<br />
2. Complete the simulation.<br />
a. cont (<strong>and</strong> then Enter).<br />
3. Close the simulation window once the simulation has finished.<br />
Ping Results<br />
The record route option was enabled for the ping dem<strong>and</strong>. An output table entry is created<br />
corresponding to each successful ping dem<strong>and</strong>. Verify that there is an entry corresponding to the<br />
ping dem<strong>and</strong>.<br />
Verify Ping Results<br />
1. Click on the View Results action button (or right-click in the project workspace <strong>and</strong> select<br />
View Results) to open up the view results dialog box.<br />
2. In the window that opens, click on the DES Run (1) Table tab.<br />
CONFIDENTIAL – RESTRICTED ACCESS: This information may not be disclosed, copied, or transmitted in any format without the prior written consent of OPNET Technologies, Inc.<br />
© 2010 OPNET Technologies, Inc.<br />
39