Perforce 2007.2 System Administrator's Guide
Perforce 2007.2 System Administrator's Guide
Perforce 2007.2 System Administrator's Guide
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
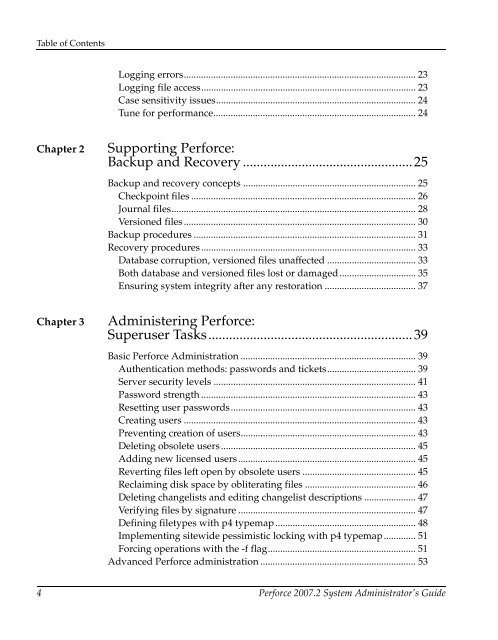
Table of ContentsLogging errors.............................................................................................. 23Logging file access....................................................................................... 23Case sensitivity issues................................................................................. 24Tune for performance.................................................................................. 24Chapter 2Supporting <strong>Perforce</strong>:Backup and Recovery .................................................25Backup and recovery concepts ...................................................................... 25Checkpoint files ........................................................................................... 26Journal files................................................................................................... 28Versioned files .............................................................................................. 30Backup procedures .......................................................................................... 31Recovery procedures ....................................................................................... 33Database corruption, versioned files unaffected .................................... 33Both database and versioned files lost or damaged............................... 35Ensuring system integrity after any restoration ..................................... 37Chapter 3Administering <strong>Perforce</strong>:Superuser Tasks...........................................................39Basic <strong>Perforce</strong> Administration ....................................................................... 39Authentication methods: passwords and tickets.................................... 39Server security levels .................................................................................. 41Password strength ....................................................................................... 43Resetting user passwords........................................................................... 43Creating users .............................................................................................. 43Preventing creation of users....................................................................... 43Deleting obsolete users............................................................................... 45Adding new licensed users........................................................................ 45Reverting files left open by obsolete users .............................................. 45Reclaiming disk space by obliterating files ............................................. 46Deleting changelists and editing changelist descriptions ..................... 47Verifying files by signature ........................................................................ 47Defining filetypes with p4 typemap......................................................... 48Implementing sitewide pessimistic locking with p4 typemap............. 51Forcing operations with the -f flag............................................................ 51Advanced <strong>Perforce</strong> administration ............................................................... 534 <strong>Perforce</strong> <strong>2007.2</strong> <strong>System</strong> Administrator’s <strong>Guide</strong>