BOX B, SYMMETRIC KEY SYSTEMSGood symmetric key systems are consideredto be secure against (essentially) all but bruteforce,exhaustive key searches. The mostwidespread symmetric system is the dataencryption standard (DES), which was developedby IBM in the mid-1970s. The DES has akey size of 56 bits. With recent hardware developments,however, a 56-bit key size is nolonger considered secure. In fact, specialpurposemachines have been built that cansearch the entire key space in just a few hours.For this reason, the National Institute of Standardsand Technology (NIST) initiated thedevelopment of the advanced encryption standard(AES), which supports 128- to 256-bitkeys. Moreover, unlike the development ofDES, the AES design process is open to thepublic. From an initial set of 15 algorithms, theNIST has selected a set of five finalists. Thefinal AES algorithm is to be selected later thisyear, see http://www.nist.gov/aes/. A similarwork—the NESSIE project—is under way inEurope, see http://www.cryptonessie.org.Wireless networks add yet another dimensionto this scenario, making it necessary tosupport mobile virtual private networks(VPN) for mobile or remote employees.Communication securitymechanismsBasic cryptographyThe two main purposes of cryptography are• to maintain the confidentiality of messages;and• to guarantee the integrity of messages.Confidentiality is provided by encryption,whereas integrity can be provided by authenticationcodes or digital signatures.EncryptionThe encryption of packets protects IP traffic(Figure 2). Before sending a message (m)the sender uses a key (kl) to encrypt it. Theciphertext (c) is then sent over a public channelthat is open to eavesdroppers. To readthe message, the recipient uses a key (k2) todecrypt the ciphertext, thereby retrieving m.Although active adversaries can insert packetsand modify <strong>com</strong>munication, for this discussionwe assume only passive listening.If kl and k2 are equal, the system is symmetric.Otherwise, it is said to be asymmetric.To guarantee security, k2 must alwaysbe kept secret, whereas kl can be madepublic—provided it is infeasible to derivek2 from kl. If indeed this is the case, thenthe system is called a public key system.Public key systems offer many interestingpossibilities; for instance, anyone can sendan encrypted credit card number to an onlineshop using the shop's public kl. Sinceonly the shop possesses k2, no one but theshop can determine the number. If a symmetricsystem were used, the shop wouldhave to exchange unique keys—privatelyand in advance—with every potential customer.The security of public key systems isalways based on the difficulty of solving certainmathematical problems, whereas symmetricschemes are more ad hoc in nature.The main drawback of public key systemsis that their mathematical nature alwaysmakes them less efficient than symmetricsystems; in particular, because the size ofkeys in public key systems is measured inkilobits—the keys of symmetrical systemsare only one tenth as large. Thus, the choiceof encryption method depends on the intendedapplication.Figure 2Use of encryption to protect a messagefrom eavesdropping.98 Ericsson Review No. 2, 2000
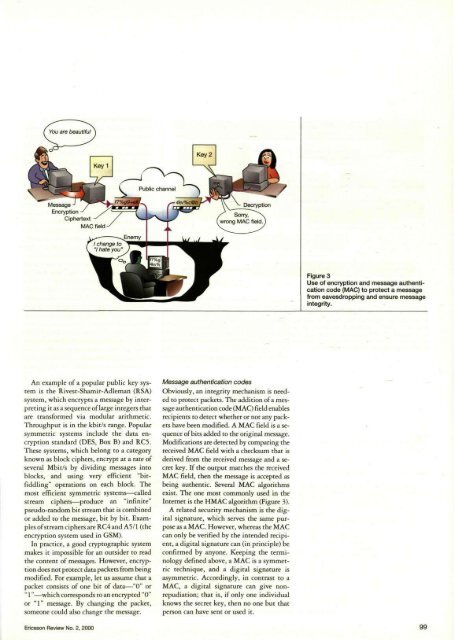
Figure 3Use of encryption and message authenticationcode (MAC) to protect a messagefrom eavesdropping and ensure messageintegrity.An example of a popular public key systemis the Rivest-Shamir-Adleman (RSA)system, which encrypts a message by interpretingit as a sequence of large integers thatare transformed via modular arithmetic.Throughput is in the kbit/s tange. Popularsymmetric systems include the data encryptionstandard (DES, Box B) and RC5.These systems, which belong to a categoryknown as block ciphers, encrypt at a rate ofseveral Mbit/s by dividing messages intoblocks, and using very efficient "bitfiddling"operations on each block. Themost efficient symmetric systems—calledstream ciphers—produce an "infinite"pseudo-random bit stream that is <strong>com</strong>binedor added to the message, bit by bit. Examplesof stream ciphers are RC4 and A5/1 (theencryption system used in GSM).In practice, a good cryptographic systemmakes it impossible for an outsider to readthe content of messages. However, encryptiondoes not protect data packets from beingmodified. For example, let us assume that apacket consists of one bit of data—"0" or" 1"—which corresponds to an encrypted "0"or "1" message. By changing the packet,someone could also change the message.Message authentication codesObviously, an integrity mechanism is neededto protect packets. The addition of a messageauthentication code (MAC) field enablesrecipients to detect whether or not any packetshave been modified. A MAC field is a sequenceof bits added to the original message.Modifications are detected by <strong>com</strong>paring thereceived MAC field with a checksum that isderived from the received message and a secretkey. If the output matches the teceivedMAC field, then the message is accepted asbeing authentic. Several MAC algorithmsexist. The one most <strong>com</strong>monly used in theInternet is the HMAC algorithm (Figure 3).A related security mechanism is the digitalsignature, which serves the same purposeas a MAC. However, whereas the MACcan only be verified by the intended recipient,a digital signatute can (in principle) beconfirmed by anyone. Keeping the terminologydefined above, a MAC is a symmetrictechnique, and a digital signature isasymmetric. Accordingly, in contrast to aMAC, a digital signature can give nonrepudiation;that is, if only one individualknows the secrer key, then no one but thatperson can have sent or used it.Ericsson Review No. 2, 2000 99