Transaction Security
H017WR70
H017WR70
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
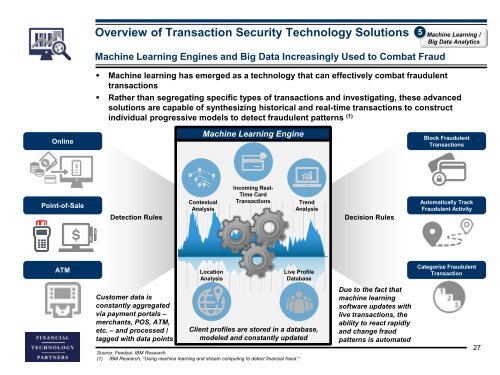
Overview of <strong>Transaction</strong> <strong>Security</strong> Technology Solutions<br />
5 Machine Learning /<br />
Big Data Analytics<br />
Machine Learning Engines and Big Data Increasingly Used to Combat Fraud<br />
• Machine learning has emerged as a technology that can effectively combat fraudulent<br />
transactions<br />
• Rather than segregating specific types of transactions and investigating, these advanced<br />
solutions are capable of synthesizing historical and real-time transactions to construct<br />
individual progressive models to detect fraudulent patterns (1)<br />
Online<br />
Machine Learning Engine<br />
Block Fraudulent<br />
<strong>Transaction</strong>s<br />
Point-of-Sale<br />
Detection Rules<br />
Contextual<br />
Analysis<br />
Incoming Real-<br />
Time Card<br />
<strong>Transaction</strong>s<br />
Trend<br />
Analysis<br />
Decision Rules<br />
Automatically Track<br />
Fraudulent Activity<br />
ATM<br />
Location<br />
Analysis<br />
Live Profile<br />
Database<br />
Categorize Fraudulent<br />
<strong>Transaction</strong><br />
Customer data is<br />
constantly aggregated<br />
via payment portals –<br />
merchants, POS, ATM,<br />
etc. – and processed /<br />
tagged with data points<br />
Client profiles are stored in a database,<br />
modeled and constantly updated<br />
Source: Feedzai, IBM Research.<br />
(1) IBM Research, “Using machine learning and stream computing to detect financial fraud.”<br />
Due to the fact that<br />
machine learning<br />
software updates with<br />
live transactions, the<br />
ability to react rapidly<br />
and change fraud<br />
patterns is automated<br />
27