Government Security News August Digital Edition
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
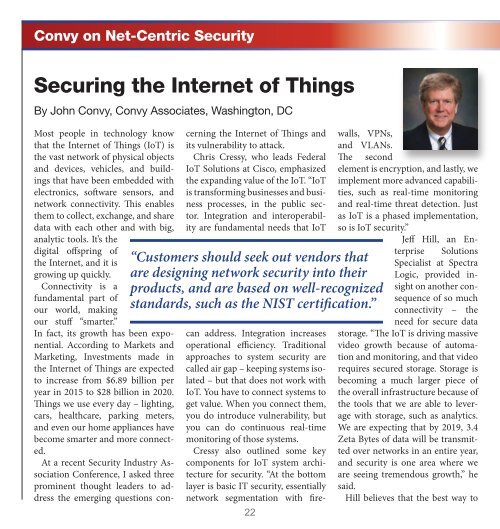
Convy on Net-Centric <strong>Security</strong><br />
Securing the Internet of Things<br />
By John Convy, Convy Associates, Washington, DC<br />
Most people in technology know<br />
that the Internet of Things (IoT) is<br />
the vast network of physical objects<br />
and devices, vehicles, and buildings<br />
that have been embedded with<br />
electronics, software sensors, and<br />
network connectivity. This enables<br />
them to collect, exchange, and share<br />
data with each other and with big,<br />
analytic tools. It’s the<br />
digital offspring of<br />
the Internet, and it is<br />
growing up quickly.<br />
Connectivity is a<br />
fundamental part of<br />
our world, making<br />
our stuff “smarter.”<br />
In fact, its growth has been exponential.<br />
According to Markets and<br />
Marketing, Investments made in<br />
the Internet of Things are expected<br />
to increase from $6.89 billion per<br />
year in 2015 to $28 billion in 2020.<br />
Things we use every day – lighting,<br />
cars, healthcare, parking meters,<br />
and even our home appliances have<br />
become smarter and more connected.<br />
At a recent <strong>Security</strong> Industry Association<br />
Conference, I asked three<br />
prominent thought leaders to address<br />
the emerging questions concerning<br />
the Internet of Things and<br />
its vulnerability to attack.<br />
Chris Cressy, who leads Federal<br />
IoT Solutions at Cisco, emphasized<br />
the expanding value of the IoT. “IoT<br />
is transforming businesses and business<br />
processes, in the public sector.<br />
Integration and interoperability<br />
are fundamental needs that IoT<br />
“Customers should seek out vendors that<br />
are designing network security into their<br />
products, and are based on well-recognized<br />
standards, such as the NIST certification.”<br />
22<br />
can address. Integration increases<br />
operational efficiency. Traditional<br />
approaches to system security are<br />
called air gap – keeping systems isolated<br />
– but that does not work with<br />
IoT. You have to connect systems to<br />
get value. When you connect them,<br />
you do introduce vulnerability, but<br />
you can do continuous real-time<br />
monitoring of those systems.<br />
Cressy also outlined some key<br />
components for IoT system architecture<br />
for security. “At the bottom<br />
layer is basic IT security, essentially<br />
network segmentation with firewalls,<br />
VPNs,<br />
and VLANs.<br />
The second<br />
element is encryption, and lastly, we<br />
implement more advanced capabilities,<br />
such as real-time monitoring<br />
and real-time threat detection. Just<br />
as IoT is a phased implementation,<br />
so is IoT security.”<br />
Jeff Hill, an Enterprise<br />
Solutions<br />
Specialist at Spectra<br />
Logic, provided insight<br />
on another consequence<br />
of so much<br />
connectivity – the<br />
need for secure data<br />
storage. “The IoT is driving massive<br />
video growth because of automation<br />
and monitoring, and that video<br />
requires secured storage. Storage is<br />
becoming a much larger piece of<br />
the overall infrastructure because of<br />
the tools that we are able to leverage<br />
with storage, such as analytics.<br />
We are expecting that by 2019, 3.4<br />
Zeta Bytes of data will be transmitted<br />
over networks in an entire year,<br />
and security is one area where we<br />
are seeing tremendous growth,” he<br />
said.<br />
Hill believes that the best way to