The Accountant-May-June 2017
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
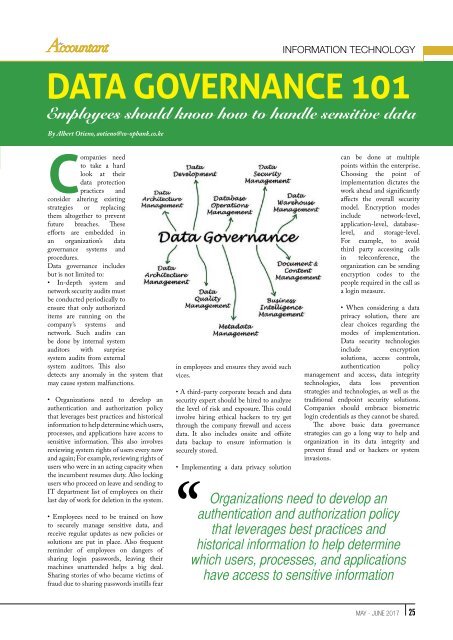
Information Technology<br />
DATA GOVERNANCE 101<br />
Employees should know how to handle sensitive data<br />
By Albert Otieno, aotieno@co-opbank.co.ke<br />
Companies need<br />
to take a hard<br />
look at their<br />
data protection<br />
practices and<br />
consider altering existing<br />
strategies or replacing<br />
them altogether to prevent<br />
future breaches. <strong>The</strong>se<br />
efforts are embedded in<br />
an organization’s data<br />
governance systems and<br />
procedures.<br />
Data governance includes<br />
but is not limited to:<br />
• In-depth system and<br />
network security audits must<br />
be conducted periodically to<br />
ensure that only authorized<br />
items are running on the<br />
company’s systems and<br />
network. Such audits can<br />
be done by internal system<br />
auditors with surprise<br />
system audits from external<br />
system auditors. This also<br />
detects any anomaly in the system that<br />
may cause system malfunctions.<br />
• Organizations need to develop an<br />
authentication and authorization policy<br />
that leverages best practices and historical<br />
information to help determine which users,<br />
processes, and applications have access to<br />
sensitive information. This also involves<br />
reviewing system rights of users every now<br />
and again; For example, reviewing rights of<br />
users who were in an acting capacity when<br />
the incumbent resumes duty. Also locking<br />
users who proceed on leave and sending to<br />
IT department list of employees on their<br />
last day of work for deletion in the system.<br />
• Employees need to be trained on how<br />
to securely manage sensitive data, and<br />
receive regular updates as new policies or<br />
solutions are put in place. Also frequent<br />
reminder of employees on dangers of<br />
sharing login passwords, leaving their<br />
machines unattended helps a big deal.<br />
Sharing stories of who became victims of<br />
fraud due to sharing passwords instills fear<br />
in employees and ensures they avoid such<br />
vices.<br />
• A third-party corporate breach and data<br />
security expert should be hired to analyze<br />
the level of risk and exposure. This could<br />
involve hiring ethical hackers to try get<br />
through the company firewall and access<br />
data. It also includes onsite and offsite<br />
data backup to ensure information is<br />
securely stored.<br />
• Implementing a data privacy solution<br />
can be done at multiple<br />
points within the enterprise.<br />
Choosing the point of<br />
implementation dictates the<br />
work ahead and significantly<br />
affects the overall security<br />
model. Encryption modes<br />
include network-level,<br />
application-level, databaselevel,<br />
and storage-level.<br />
For example, to avoid<br />
third party accessing calls<br />
in teleconference, the<br />
organization can be sending<br />
encryption codes to the<br />
people required in the call as<br />
a login measure.<br />
• When considering a data<br />
privacy solution, there are<br />
clear choices regarding the<br />
modes of implementation.<br />
Data security technologies<br />
include encryption<br />
solutions, access controls,<br />
authentication policy<br />
management and access, data integrity<br />
technologies, data loss prevention<br />
strategies and technologies, as well as the<br />
traditional endpoint security solutions.<br />
Companies should embrace biometric<br />
login credentials as they cannot be shared.<br />
<strong>The</strong> above basic data governance<br />
strategies can go a long way to help and<br />
organization in its data integrity and<br />
prevent fraud and or hackers or system<br />
invasions.<br />
Organizations need to develop an<br />
authentication and authorization policy<br />
that leverages best practices and<br />
historical information to help determine<br />
which users, processes, and applications<br />
have access to sensitive information<br />
MAY - JUNE <strong>2017</strong> 25