Ad Hoc Networks : Technologies and Protocols - University of ...
Ad Hoc Networks : Technologies and Protocols - University of ...
Ad Hoc Networks : Technologies and Protocols - University of ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
256 Security in Mobile <strong>Ad</strong>-<strong>Hoc</strong> <strong>Networks</strong><br />
9.4 Intrusion Detection Techniques<br />
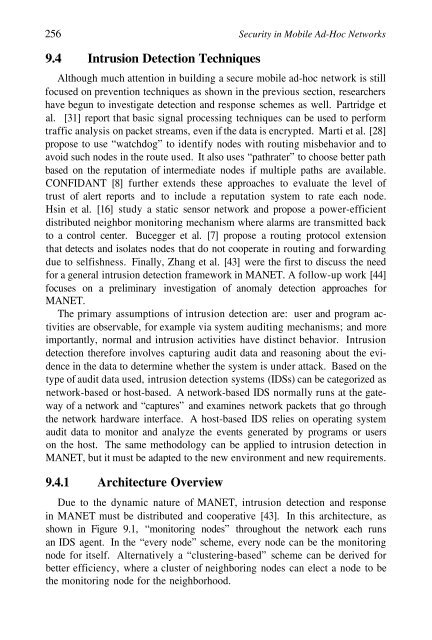
Although much attention in building a secure mobile ad-hoc network is still<br />
focused on prevention techniques as shown in the previous section, researchers<br />
have begun to investigate detection <strong>and</strong> response schemes as well. Partridge et<br />
al. [31] report that basic signal processing techniques can be used to perform<br />
traffic analysis on packet streams, even if the data is encrypted. Marti et al. [28]<br />
propose to use “watchdog” to identify nodes with routing misbehavior <strong>and</strong> to<br />
avoid such nodes in the route used. It also uses “pathrater” to choose better path<br />
based on the reputation <strong>of</strong> intermediate nodes if multiple paths are available.<br />
CONFIDANT [8] further extends these approaches to evaluate the level <strong>of</strong><br />
trust <strong>of</strong> alert reports <strong>and</strong> to include a reputation system to rate each node.<br />
Hsin et al. [16] study a static sensor network <strong>and</strong> propose a power-efficient<br />
distributed neighbor monitoring mechanism where alarms are transmitted back<br />
to a control center. Bucegger et al. [7] propose a routing protocol extension<br />
that detects <strong>and</strong> isolates nodes that do not cooperate in routing <strong>and</strong> forwarding<br />
due to selfishness. Finally, Zhang et al. [43] were the first to discuss the need<br />
for a general intrusion detection framework in MANET. A follow-up work [44]<br />
focuses on a preliminary investigation <strong>of</strong> anomaly detection approaches for<br />
MANET.<br />
The primary assumptions <strong>of</strong> intrusion detection are: user <strong>and</strong> program activities<br />
are observable, for example via system auditing mechanisms; <strong>and</strong> more<br />
importantly, normal <strong>and</strong> intrusion activities have distinct behavior. Intrusion<br />
detection therefore involves capturing audit data <strong>and</strong> reasoning about the evidence<br />
in the data to determine whether the system is under attack. Based on the<br />
type <strong>of</strong> audit data used, intrusion detection systems (IDSs) can be categorized as<br />
network-based or host-based. A network-based IDS normally runs at the gateway<br />
<strong>of</strong> a network <strong>and</strong> “captures” <strong>and</strong> examines network packets that go through<br />
the network hardware interface. A host-based IDS relies on operating system<br />
audit data to monitor <strong>and</strong> analyze the events generated by programs or users<br />
on the host. The same methodology can be applied to intrusion detection in<br />
MANET, but it must be adapted to the new environment <strong>and</strong> new requirements.<br />
9.4.1 Architecture Overview<br />
Due to the dynamic nature <strong>of</strong> MANET, intrusion detection <strong>and</strong> response<br />
in MANET must be distributed <strong>and</strong> cooperative [43]. In this architecture, as<br />
shown in Figure 9.1, “monitoring nodes” throughout the network each runs<br />
an IDS agent. In the “every node” scheme, every node can be the monitoring<br />
node for itself. Alternatively a “clustering-based” scheme can be derived for<br />
better efficiency, where a cluster <strong>of</strong> neighboring nodes can elect a node to be<br />
the monitoring node for the neighborhood.