Ad Hoc Networks : Technologies and Protocols - University of ...
Ad Hoc Networks : Technologies and Protocols - University of ...
Ad Hoc Networks : Technologies and Protocols - University of ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
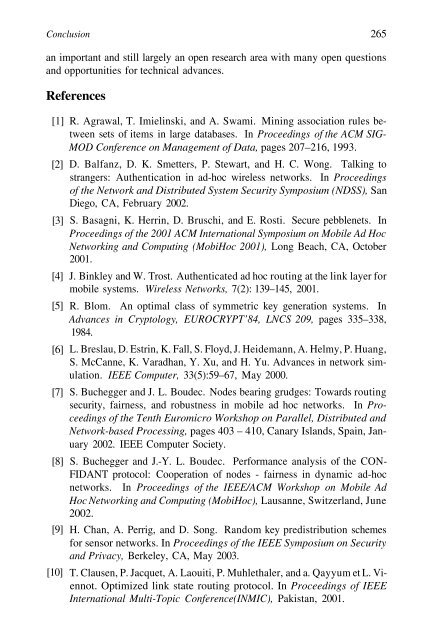
Conclusion 265<br />
an important <strong>and</strong> still largely an open research area with many open questions<br />
<strong>and</strong> opportunities for technical advances.<br />
References<br />
[1]<br />
[2]<br />
[3]<br />
[4]<br />
[5]<br />
[6]<br />
[7]<br />
[8]<br />
[9]<br />
[10]<br />
R. Agrawal, T. Imielinski, <strong>and</strong> A. Swami. Mining association rules between<br />
sets <strong>of</strong> items in large databases. In Proceedings <strong>of</strong> the ACM SIG-<br />
MOD Conference on Management <strong>of</strong> Data, pages 207–216, 1993.<br />
D. Balfanz, D. K. Smetters, P. Stewart, <strong>and</strong> H. C. Wong. Talking to<br />
strangers: Authentication in ad-hoc wireless networks. In Proceedings<br />
<strong>of</strong> the Network <strong>and</strong> Distributed System Security Symposium (NDSS), San<br />
Diego, CA, February 2002.<br />
S. Basagni, K. Herrin, D. Bruschi, <strong>and</strong> E. Rosti. Secure pebblenets. In<br />
Proceedings <strong>of</strong> the 2001 ACM International Symposium on Mobile <strong>Ad</strong> <strong>Hoc</strong><br />
Networking <strong>and</strong> Computing (Mobi<strong>Hoc</strong> 2001), Long Beach, CA, October<br />
2001.<br />
J. Binkley <strong>and</strong> W. Trost. Authenticated ad hoc routing at the link layer for<br />
mobile systems. Wireless <strong>Networks</strong>, 7(2): 139–145, 2001.<br />
R. Blom. An optimal class <strong>of</strong> symmetric key generation systems. In<br />
<strong>Ad</strong>vances in Cryptology, EUROCRYPT’84, LNCS 209, pages 335–338,<br />
1984.<br />
L. Breslau, D. Estrin, K. Fall, S. Floyd, J. Heidemann, A. Helmy, P. Huang,<br />
S. McCanne, K. Varadhan, Y. Xu, <strong>and</strong> H. Yu. <strong>Ad</strong>vances in network simulation.<br />
IEEE Computer, 33(5):59–67, May 2000.<br />
S. Buchegger <strong>and</strong> J. L. Boudec. Nodes bearing grudges: Towards routing<br />
security, fairness, <strong>and</strong> robustness in mobile ad hoc networks. In Proceedings<br />
<strong>of</strong> the Tenth Euromicro Workshop on Parallel, Distributed <strong>and</strong><br />
Network-based Processing, pages 403 – 410, Canary Isl<strong>and</strong>s, Spain, January<br />
2002. IEEE Computer Society.<br />
S. Buchegger <strong>and</strong> J.-Y. L. Boudec. Performance analysis <strong>of</strong> the CON-<br />
FIDANT protocol: Cooperation <strong>of</strong> nodes - fairness in dynamic ad-hoc<br />
networks. In Proceedings <strong>of</strong> the IEEE/ACM Workshop on Mobile <strong>Ad</strong><br />
<strong>Hoc</strong> Networking <strong>and</strong> Computing (Mobi<strong>Hoc</strong>), Lausanne, Switzerl<strong>and</strong>, June<br />
2002.<br />
H. Chan, A. Perrig, <strong>and</strong> D. Song. R<strong>and</strong>om key predistribution schemes<br />
for sensor networks. In Proceedings <strong>of</strong> the IEEE Symposium on Security<br />
<strong>and</strong> Privacy, Berkeley, CA, May 2003.<br />
T. Clausen, P. Jacquet, A. Laouiti, P. Muhlethaler, <strong>and</strong> a. Qayyum et L. Viennot.<br />
Optimized link state routing protocol. In Proceedings <strong>of</strong> IEEE<br />
International Multi-Topic Conference(INMIC), Pakistan, 2001.