- Page 1 and 2: Kerio Control Administrator’s Gui
- Page 3 and 4: Contents Installing Kerio Control .
- Page 5 and 6: Example of Kerio VPN configuration:
- Page 7 and 8: Deny . . . . . . . . . . . . . . .
- Page 9 and 10: Deleting user accounts . . . . . .
- Page 11 and 12: Variables . . . . . . . . . . . . .
- Page 13 and 14: FTP over Kerio Control proxy server
- Page 15 and 16: 1.3 Installing VMware Virtual Appli
- Page 17 and 18: Configuring the Activation Wizard C
- Page 19 and 20: 2.1 Configuring the Activation Wiza
- Page 21 and 22: 3.1 Configuration Assistant overvie
- Page 23 and 24: 3.1 Configuration Assistant overvie
- Page 25 and 26: 3.1 Configuration Assistant overvie
- Page 27 and 28: 4.3 Registering Kerio Control in th
- Page 29 and 30: 4.4 Registering Kerio Control via W
- Page 31 and 32: 5.3 Changing a SSL certificate To c
- Page 33 and 34: 6.4 Adding new interfaces • A Sin
- Page 35 and 36: 6.5 Configuring Ethernet ports 3. I
- Page 37 and 38: Configuring L2TP tunnel L2TP tunnel
- Page 39 and 40: 7.3 Configuring L2TP tunnel 6. Disa
- Page 41 and 42: 8.3 Removing VLAN interfaces 3. Ope
- Page 43 and 44: 9.4 Configuring Kerio VPN clients 3
- Page 45 and 46: 10.4 Configuring routing 5. Select
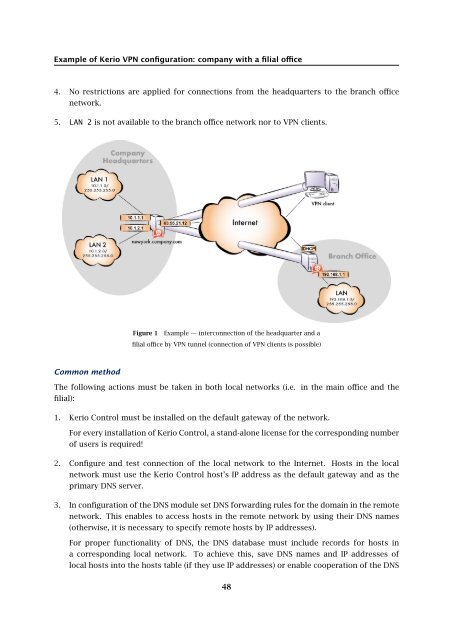
- Page 47: Example of Kerio VPN configuration:
- Page 51 and 52: 11.1 Overview free subnet. The VPN
- Page 53 and 54: Example of Kerio VPN configuration:
- Page 55 and 56: 12.1 Overview Set routing (define c
- Page 57 and 58: 12.1 Overview On the Advanced tab,
- Page 59 and 60: 12.1 Overview 5. Create an active e
- Page 61 and 62: 12.1 Overview • No DNS server wil
- Page 63 and 64: Configuring IPsec VPN IPsec overvie
- Page 65 and 66: 13.3 Configuring IPsec server with
- Page 67 and 68: Configuring IPsec VPN tunnel IPsec
- Page 69 and 70: 14.5 Configuring VPN failover 5. Se
- Page 71 and 72: Support for IPv6 protocol Support f
- Page 73 and 74: Configuring traffic rules How traff
- Page 75 and 76: 16.3 User accounts and groups in tr
- Page 77 and 78: 16.4 Demilitarized zone (DMZ) In th
- Page 79 and 80: 17.2 Configuring IP address transla
- Page 81 and 82: 17.3 A default NAT rule description
- Page 83 and 84: 18.1 Multihoming overview 8. Double
- Page 85 and 86: 19.1 Limiting Internet Access This
- Page 87 and 88: Configuring Demilitarized Zone (DMZ
- Page 89 and 90: Configuring policy routing Policy r
- Page 91 and 92: 22.3 Configuring an optimization of
- Page 93 and 94: 23.3 Configuring ignored intrusions
- Page 95 and 96: Filtering MAC addresses Filtering M
- Page 97 and 98: 25.2 Configuring the UPnP support 1
- Page 99 and 100:
26.4 Configuring bandwidth manageme
- Page 101 and 102:
Configuring the Content Filter Cont
- Page 103 and 104:
27.4 Adding content rules 3. In tab
- Page 105 and 106:
27.4 Adding content rules The user
- Page 107 and 108:
27.5 Examples Figure 5 The first pa
- Page 109 and 110:
27.5 Examples 11. Select Skip Forbi
- Page 111 and 112:
28.2 Configuring HTTP cache Configu
- Page 113 and 114:
29.1 Why use a proxy server in Keri
- Page 115 and 116:
Filtering web content by word occur
- Page 117 and 118:
Using Kerio Control Web Filter Keri
- Page 119 and 120:
31.3 Using Web Filter in URL rules
- Page 121 and 122:
32.2 Configuring antivirus protecti
- Page 123 and 124:
33.3 Manual definition of Scopes an
- Page 125 and 126:
33.4 Leases and Reservations Exampl
- Page 127 and 128:
Using the DNS module DNS forwarding
- Page 129 and 130:
34.3 Configuring custom DNS Forward
- Page 131 and 132:
Configuring a routing table Routing
- Page 133 and 134:
35.1 Routing table overview If this
- Page 135 and 136:
36.3 Gathering of statistical infor
- Page 137 and 138:
36.4 Settings for statistics, repor
- Page 139 and 140:
36.5 Logging on the web interface a
- Page 141 and 142:
37.4 Configuring the server name Co
- Page 143 and 144:
38.3 Upgrade with USB tools 4. Clic
- Page 145 and 146:
Dynamic DNS for public IP address o
- Page 147 and 148:
Saving configuration to Samepage Sa
- Page 149 and 150:
Creating user accounts User account
- Page 151 and 152:
42.4 Automatic login on static IP a
- Page 153 and 154:
42.6 Troubleshooting Troubleshootin
- Page 155 and 156:
43.2 What levels of access rights a
- Page 157 and 158:
44.4 Connecting to Apple Open Direc
- Page 159 and 160:
44.7 Collision of directory service
- Page 161 and 162:
45.2 Firewall User Authentication
- Page 163 and 164:
Protecting users against password g
- Page 165 and 166:
Configuring SSL certificates in Ker
- Page 167 and 168:
48.5 Intermediate certificates The
- Page 169 and 170:
49.2 Configuring IP address group
- Page 171 and 172:
50.2 Defining time ranges 4. You ca
- Page 173 and 174:
Using services Services Services ar
- Page 175 and 176:
52.3 Protocol inspectors Figure 1 D
- Page 177 and 178:
53.1 Status - Active Hosts overview
- Page 179 and 180:
53.1 Status - Active Hosts overview
- Page 181 and 182:
53.1 Status - Active Hosts overview
- Page 183 and 184:
54.1 Status - Active Connections ov
- Page 185 and 186:
Using Status - VPN Clients Status -
- Page 187 and 188:
56.1 Status - Alert Messages overvi
- Page 189 and 190:
56.1 Status - Alert Messages overvi
- Page 191 and 192:
57.2 Volume of transferred data and
- Page 193 and 194:
57.3 Traffic Charts Interface Stati
- Page 195 and 196:
Using System Health in Kerio Contro
- Page 197 and 198:
59.3 Log highlighting • Format
- Page 199 and 200:
59.4 Logs Settings 3. Type a number
- Page 201 and 202:
Logging packets Packet logging This
- Page 203 and 204:
60.2 Configuring packet logging if
- Page 205 and 206:
Log packet formatting Log packet fo
- Page 207 and 208:
Using the Config log Config log ove
- Page 209 and 210:
Using the Connection log Connection
- Page 211 and 212:
Using the Debug log Debug log overv
- Page 213 and 214:
Using the Dial log Dial log overvie
- Page 215 and 216:
Using the Error log Error log overv
- Page 217 and 218:
Using the Filter log Filter log ove
- Page 219 and 220:
67.2 Reading the Filter log • fla
- Page 221 and 222:
68.2 Reading the Http log • GET
- Page 223 and 224:
69.2 Reading the Security log name
- Page 225 and 226:
Using the Warning log Warning log o
- Page 227 and 228:
Using the Web log Web log overview
- Page 229 and 230:
72.3 Traceroute Traceroute The trac
- Page 231 and 232:
SNMP monitoring Configuring Kerio C
- Page 233 and 234:
Generating a Software Appliance ins
- Page 235 and 236:
Automatic user authentication using
- Page 237 and 238:
75.5 NTLM authentication process
- Page 239 and 240:
76.1 FTP over proxy server overview
- Page 241 and 242:
Configuration files Configuration f
- Page 243 and 244:
Configuring backup and transfer Bac
- Page 245 and 246:
Legal Notices Trademarks and regist
- Page 247 and 248:
80.2 Used open source software http
- Page 249 and 250:
80.2 Used open source software PHP