PUNE
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
6<br />
SECURITY TECH<br />
With contribution from Maneesh Bhandari, Ex Sena Systems / Angel Investor<br />
and Milind Borate, Druva.<br />
nforma on Security, some mes shortened to InfoSec, is the prac ce of defending informa on from unauthorised access, use,<br />
Idisclosure, disrup on, modifica on, perusal, inspec on, recording or destruc on. It is a general term that can be used regardless<br />
of the form the data may take (electronic, physical, etc.)<br />
India surpassed Japan (a er the US and China) as the third largest internet user last year and according to advisory firm KPMG, its<br />
internet protocol (IP) traffic is to grow six-fold from 2012 to 2017 at a Compound Annual Growth Rate (CAGR) of 44%.<br />
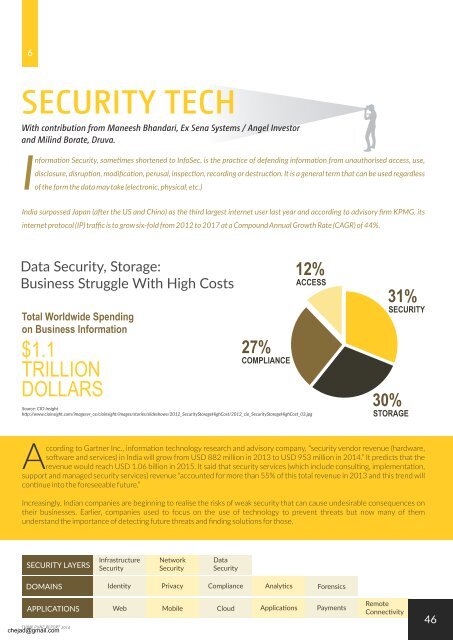
Data Security, Storage:<br />
Business Struggle With High Costs<br />
Total Worldwide Spending<br />
on Business Information<br />
$1.1<br />
TRILLION<br />
DOLLARS<br />
27%<br />
COMPLIANCE<br />
12%<br />
ACCESS<br />
Source: CIO Insight<br />
h p://www.cioinsight.com/imagesvr_ce/cioinsight/images/stories/slideshows/2012_SecurityStorageHighCost/2012_cio_SecurityStorageHighCost_03.jpg<br />
31%<br />
SECURITY<br />
30%<br />
STORAGE<br />
ccording to Gartner Inc., informa on technology research and advisory company, “security vendor revenue (hardware,<br />
Aso ware and services) in India will grow from USD 882 million in 2013 to USD 953 million in 2014.” It predicts that the<br />
revenue would reach USD 1.06 billion in 2015. It said that security services (which include consul ng, implementa on,<br />
support and managed security services) revenue “accounted for more than 55% of this total revenue in 2013 and this trend will<br />
con nue into the foreseeable future.”<br />
Increasingly, Indian companies are beginning to realise the risks of weak security that can cause undesirable consequences on<br />
their businesses. Earlier, companies used to focus on the use of technology to prevent threats but now many of them<br />
understand the importance of detec ng future threats and finding solu ons for those.<br />
SECURITY LAYERS<br />
Infrastructure<br />
Security<br />
Network<br />
Security<br />
Data<br />
Security<br />
DOMAINS<br />
Iden ty Privacy Compliance Analy cs Forensics<br />
APPLICATIONS<br />
THINK <strong>PUNE</strong> REPORT 2014<br />
chejad@gmail.com<br />
Web Mobile Cloud Applica ons Payments<br />
Remote<br />
Connec vity<br />
46