Footwear Industry Footwear Industry - empirica
Footwear Industry Footwear Industry - empirica
Footwear Industry Footwear Industry - empirica
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
<strong>Footwear</strong><br />
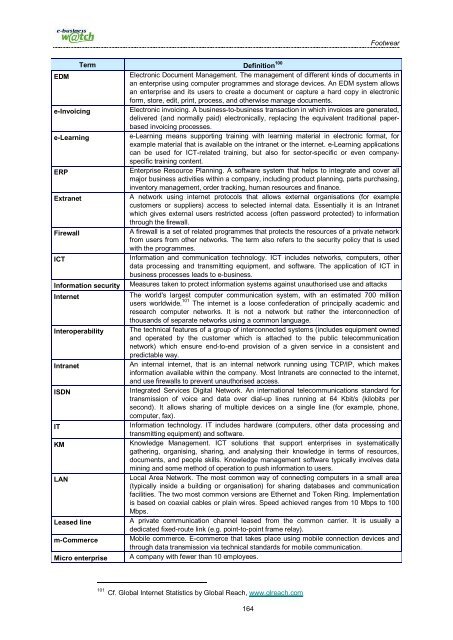
EDM<br />
e-Invoicing<br />
e-Learning<br />
ERP<br />
Extranet<br />
Firewall<br />
ICT<br />
Term Definition 100<br />
Information security<br />
Internet<br />
Interoperability<br />
Intranet<br />
ISDN<br />
IT<br />
KM<br />
LAN<br />
Leased line<br />
m-Commerce<br />
Micro enterprise<br />
Electronic Document Management. The management of different kinds of documents in<br />
an enterprise using computer programmes and storage devices. An EDM system allows<br />
an enterprise and its users to create a document or capture a hard copy in electronic<br />
form, store, edit, print, process, and otherwise manage documents.<br />
Electronic invoicing. A business-to-business transaction in which invoices are generated,<br />
delivered (and normally paid) electronically, replacing the equivalent traditional paperbased<br />
invoicing processes.<br />
e-Learning means supporting training with learning material in electronic format, for<br />
example material that is available on the intranet or the internet. e-Learning applications<br />
can be used for ICT-related training, but also for sector-specific or even companyspecific<br />
training content.<br />
Enterprise Resource Planning. A software system that helps to integrate and cover all<br />
major business activities within a company, including product planning, parts purchasing,<br />
inventory management, order tracking, human resources and finance.<br />
A network using internet protocols that allows external organisations (for example<br />
customers or suppliers) access to selected internal data. Essentially it is an Intranet<br />
which gives external users restricted access (often password protected) to information<br />
through the firewall.<br />
A firewall is a set of related programmes that protects the resources of a private network<br />
from users from other networks. The term also refers to the security policy that is used<br />
with the programmes.<br />
Information and communication technology. ICT includes networks, computers, other<br />
data processing and transmitting equipment, and software. The application of ICT in<br />
business processes leads to e-business.<br />
Measures taken to protect information systems against unauthorised use and attacks<br />
The world's largest computer communication system, with an estimated 700 million<br />
users worldwide. 101 The internet is a loose confederation of principally academic and<br />
research computer networks. It is not a network but rather the interconnection of<br />
thousands of separate networks using a common language.<br />
The technical features of a group of interconnected systems (includes equipment owned<br />
and operated by the customer which is attached to the public telecommunication<br />
network) which ensure end-to-end provision of a given service in a consistent and<br />
predictable way.<br />
An internal internet, that is an internal network running using TCP/IP, which makes<br />
information available within the company. Most Intranets are connected to the internet,<br />
and use firewalls to prevent unauthorised access.<br />
Integrated Services Digital Network. An international telecommunications standard for<br />
transmission of voice and data over dial-up lines running at 64 Kbit/s (kilobits per<br />
second). It allows sharing of multiple devices on a single line (for example, phone,<br />
computer, fax).<br />
Information technology. IT includes hardware (computers, other data processing and<br />
transmitting equipment) and software.<br />
Knowledge Management. ICT solutions that support enterprises in systematically<br />
gathering, organising, sharing, and analysing their knowledge in terms of resources,<br />
documents, and people skills. Knowledge management software typically involves data<br />
mining and some method of operation to push information to users.<br />
Local Area Network. The most common way of connecting computers in a small area<br />
(typically inside a building or organisation) for sharing databases and communication<br />
facilities. The two most common versions are Ethernet and Token Ring. Implementation<br />
is based on coaxial cables or plain wires. Speed achieved ranges from 10 Mbps to 100<br />
Mbps.<br />
A private communication channel leased from the common carrier. It is usually a<br />
dedicated fixed-route link (e.g. point-to-point frame relay).<br />
Mobile commerce. E-commerce that takes place using mobile connection devices and<br />
through data transmission via technical standards for mobile communication.<br />
A company with fewer than 10 employees.<br />
101 Cf. Global Internet Statistics by Global Reach, www.glreach.com<br />
164