Legal Disclaimer
Hacking-For-Beginners-a-beginners-guide-for-learning-ethical-hacking
Hacking-For-Beginners-a-beginners-guide-for-learning-ethical-hacking
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Hacking For Beginners – Manthan Desai 2010<br />
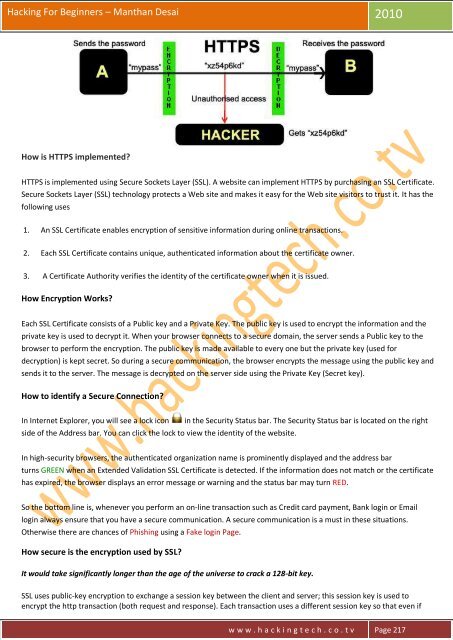
How is HTTPS implemented?<br />
HTTPS is implemented using Secure Sockets Layer (SSL). A website can implement HTTPS by purchasing an SSL Certificate.<br />
Secure Sockets Layer (SSL) technology protects a Web site and makes it easy for the Web site visitors to trust it. It has the<br />
following uses<br />
1. An SSL Certificate enables encryption of sensitive information during online transactions.<br />
2. Each SSL Certificate contains unique, authenticated information about the certificate owner.<br />
3. A Certificate Authority verifies the identity of the certificate owner when it is issued.<br />
How Encryption Works?<br />
Each SSL Certificate consists of a Public key and a Private Key. The public key is used to encrypt the information and the<br />
private key is used to decrypt it. When your browser connects to a secure domain, the server sends a Public key to the<br />
browser to perform the encryption. The public key is made available to every one but the private key (used for<br />
decryption) is kept secret. So during a secure communication, the browser encrypts the message using the public key and<br />
sends it to the server. The message is decrypted on the server side using the Private Key (Secret key).<br />
How to identify a Secure Connection?<br />
In Internet Explorer, you will see a lock icon<br />
side of the Address bar. You can click the lock to view the identity of the website.<br />
in the Security Status bar. The Security Status bar is located on the right<br />
In high-security browsers, the authenticated organization name is prominently displayed and the address bar<br />
turns GREEN when an Extended Validation SSL Certificate is detected. If the information does not match or the certificate<br />
has expired, the browser displays an error message or warning and the status bar may turn RED.<br />
So the bottom line is, whenever you perform an on-line transaction such as Credit card payment, Bank login or Email<br />
login always ensure that you have a secure communication. A secure communication is a must in these situations.<br />
Otherwise there are chances of Phishing using a Fake login Page.<br />
How secure is the encryption used by SSL?<br />
It would take significantly longer than the age of the universe to crack a 128-bit key.<br />
SSL uses public-key encryption to exchange a session key between the client and server; this session key is used to<br />
encrypt the http transaction (both request and response). Each transaction uses a different session key so that even if<br />
w w w . h a c k i n g t e c h . c o . t v Page 217