Legal Disclaimer
Hacking-For-Beginners-a-beginners-guide-for-learning-ethical-hacking
Hacking-For-Beginners-a-beginners-guide-for-learning-ethical-hacking
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Hacking For Beginners – Manthan Desai 2010<br />
Detecting ‘live’ systems on target network<br />
Why Detecting ‘live’ systems on tagret network ?<br />
<br />
<br />
<br />
To determine the perimeter of the target network /system<br />
To facilitate network mapping<br />
To build an inventory of accessible systems on target network<br />
Tools used for this<br />
<br />
<br />
War Dialers<br />
Ping Utilities<br />
War Dialers<br />
<br />
<br />
<br />
<br />
A war dialer is a tool used to scan a large pool of telephone numbers to detect vulnerable modems to provide<br />
access to the system.<br />
A demon dialer is a tool used to monitor a specific phone number and target its modem to gain access to the<br />
system.<br />
Threat is high in systems with poorly configured remote access products providing entry to larger networks.<br />
Tools include THC-Scan, ToneLoc, TBA etc.<br />
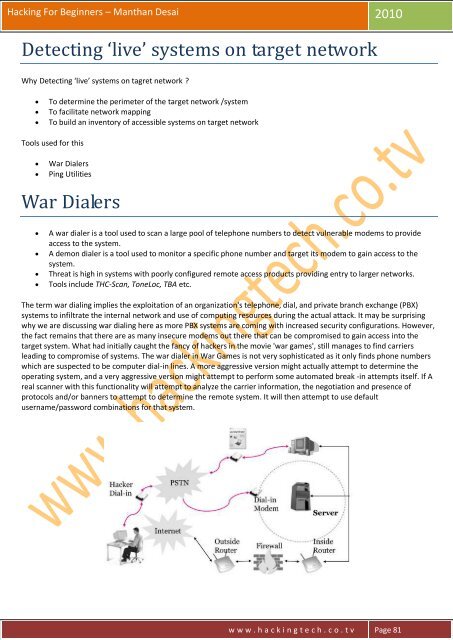
The term war dialing implies the exploitation of an organization's telephone, dial, and private branch exchange (PBX)<br />
systems to infiltrate the internal network and use of computing resources during the actual attack. It may be surprising<br />
why we are discussing war dialing here as more PBX systems are coming with increased security configurations. However,<br />
the fact remains that there are as many insecure modems out there that can be compromised to gain access into the<br />
target system. What had initially caught the fancy of hackers in the movie 'war games', still manages to find carriers<br />
leading to compromise of systems. The war dialer in War Games is not very sophisticated as it only finds phone numbers<br />
which are suspected to be computer dial-in lines. A more aggressive version might actually attempt to determine the<br />
operating system, and a very aggressive version might attempt to perform some automated break -in attempts itself. If A<br />
real scanner with this functionality will attempt to analyze the carrier information, the negotiation and presence of<br />
protocols and/or banners to attempt to determine the remote system. It will then attempt to use default<br />
username/password combinations for that system.<br />
w w w . h a c k i n g t e c h . c o . t v Page 81