128-Bit Addressing in RISC-V and Security
Tue1530-128bit-Addr-RISC-V-Wallach-Micron
Tue1530-128bit-Addr-RISC-V-Wallach-Micron
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
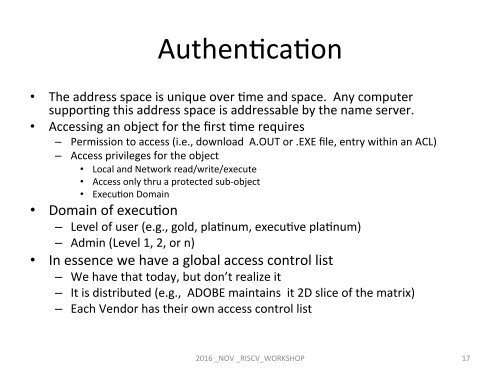
AuthenCcaCon<br />
• The address space is unique over Cme <strong>and</strong> space. Any computer<br />
supporCng this address space is addressable by the name server.<br />
• Access<strong>in</strong>g an object for the first Cme requires<br />
– Permission to access (i.e., download A.OUT or .EXE file, entry with<strong>in</strong> an ACL)<br />
– Access privileges for the object<br />
• Local <strong>and</strong> Network read/write/execute<br />
• Access only thru a protected sub-object<br />
• ExecuCon Doma<strong>in</strong><br />
• Doma<strong>in</strong> of execuCon<br />
– Level of user (e.g., gold, plaCnum, execuCve plaCnum)<br />
– Adm<strong>in</strong> (Level 1, 2, or n)<br />
• In essence we have a global access control list<br />
– We have that today, but don’t realize it<br />
– It is distributed (e.g., ADOBE ma<strong>in</strong>ta<strong>in</strong>s it 2D slice of the matrix)<br />
– Each Vendor has their own access control list<br />
2016 _NOV _<strong>RISC</strong>V_WORKSHOP<br />
17