128-Bit Addressing in RISC-V and Security
Tue1530-128bit-Addr-RISC-V-Wallach-Micron
Tue1530-128bit-Addr-RISC-V-Wallach-Micron
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
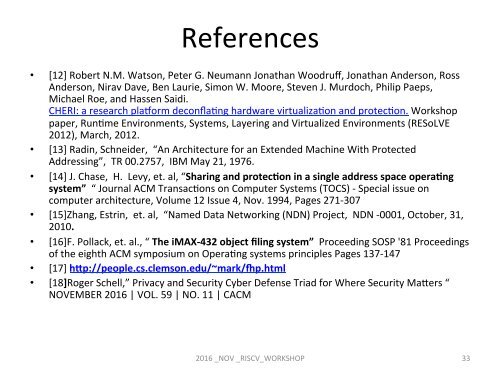
References<br />
• [12] Robert N.M. Watson, Peter G. Neumann Jonathan Woodruff, Jonathan Anderson, Ross<br />
Anderson, Nirav Dave, Ben Laurie, Simon W. Moore, Steven J. Murdoch, Philip Paeps,<br />
Michael Roe, <strong>and</strong> Hassen Saidi.<br />
CHERI: a research plaorm deconflaCng hardware virtualizaCon <strong>and</strong> protecCon. Workshop<br />
paper, RunCme Environments, Systems, Layer<strong>in</strong>g <strong>and</strong> Virtualized Environments (RESoLVE<br />
2012), March, 2012.<br />
• [13] Rad<strong>in</strong>, Schneider, “An Architecture for an Extended Mach<strong>in</strong>e With Protected<br />
<strong>Address<strong>in</strong>g</strong>”, TR 00.2757, IBM May 21, 1976.<br />
• [14] J. Chase, H. Levy, et. al, “Shar<strong>in</strong>g <strong>and</strong> protecRon <strong>in</strong> a s<strong>in</strong>gle address space operaRng<br />
system” “ Journal ACM TransacCons on Computer Systems (TOCS) - Special issue on<br />
computer architecture, Volume 12 Issue 4, Nov. 1994, Pages 271-307<br />
• [15]Zhang, Estr<strong>in</strong>, et. al, “Named Data Network<strong>in</strong>g (NDN) Project, NDN -0001, October, 31,<br />
2010.<br />
• [16]F. Pollack, et. al., “ The iMAX-432 object fil<strong>in</strong>g system” Proceed<strong>in</strong>g SOSP '81 Proceed<strong>in</strong>gs<br />
of the eighth ACM symposium on OperaCng systems pr<strong>in</strong>ciples Pages 137-147<br />
• [17] hlp://people.cs.clemson.edu/~mark/op.html<br />
• [18]Roger Schell,” Privacy <strong>and</strong> <strong>Security</strong> Cyber Defense Triad for Where <strong>Security</strong> Magers “<br />
NOVEMBER 2016 | VOL. 59 | NO. 11 | CACM<br />
2016 _NOV _<strong>RISC</strong>V_WORKSHOP<br />
33