128-Bit Addressing in RISC-V and Security
Tue1530-128bit-Addr-RISC-V-Wallach-Micron
Tue1530-128bit-Addr-RISC-V-Wallach-Micron
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
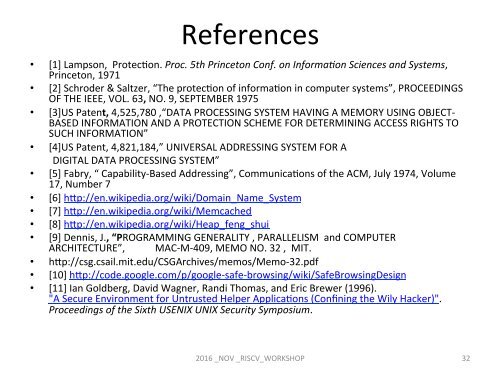
References<br />
• [1] Lampson, ProtecCon. Proc. 5th Pr<strong>in</strong>ceton Conf. on Informa2on Sciences <strong>and</strong> Systems,<br />
Pr<strong>in</strong>ceton, 1971<br />
• [2] Schroder & Saltzer, “The protecCon of <strong>in</strong>formaCon <strong>in</strong> computer systems”, PROCEEDINGS<br />
OF THE IEEE, VOL. 63, NO. 9, SEPTEMBER 1975<br />
• [3]US Patent, 4,525,780 ,“DATA PROCESSING SYSTEM HAVING A MEMORY USING OBJECT-<br />
BASED INFORMATION AND A PROTECTION SCHEME FOR DETERMINING ACCESS RIGHTS TO<br />
SUCH INFORMATION”<br />
• [4]US Patent, 4,821,184,” UNIVERSAL ADDRESSING SYSTEM FOR A<br />
DIGITAL DATA PROCESSING SYSTEM”<br />
• [5] Fabry, “ Capability-Based <strong>Address<strong>in</strong>g</strong>”, CommunicaCons of the ACM, July 1974, Volume<br />
17, Number 7<br />
• [6] hgp://en.wikipedia.org/wiki/Doma<strong>in</strong>_Name_System<br />
• [7] hgp://en.wikipedia.org/wiki/Memcached<br />
• [8] hgp://en.wikipedia.org/wiki/Heap_feng_shui<br />
• [9] Dennis, J., “PROGRAMMING GENERALITY , PARALLELISM <strong>and</strong> COMPUTER<br />
ARCHITECTURE”, MAC-M-409, MEMO NO. 32 , MIT.<br />
• hgp://csg.csail.mit.edu/CSGArchives/memos/Memo-32.pdf<br />
• [10] hgp://code.google.com/p/google-safe-brows<strong>in</strong>g/wiki/SafeBrows<strong>in</strong>gDesign<br />
• [11] Ian Goldberg, David Wagner, R<strong>and</strong>i Thomas, <strong>and</strong> Eric Brewer (1996).<br />
"A Secure Environment for Untrusted Helper ApplicaCons (Conf<strong>in</strong><strong>in</strong>g the Wily Hacker)".<br />
Proceed<strong>in</strong>gs of the Sixth USENIX UNIX <strong>Security</strong> Symposium.<br />
2016 _NOV _<strong>RISC</strong>V_WORKSHOP<br />
32