128-Bit Addressing in RISC-V and Security
Tue1530-128bit-Addr-RISC-V-Wallach-Micron
Tue1530-128bit-Addr-RISC-V-Wallach-Micron
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
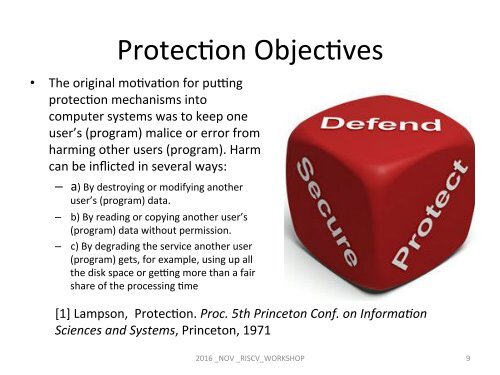
ProtecCon ObjecCves<br />
• The orig<strong>in</strong>al moCvaCon for puyng<br />
protecCon mechanisms <strong>in</strong>to<br />
computer systems was to keep one<br />
user’s (program) malice or error from<br />
harm<strong>in</strong>g other users (program). Harm<br />
can be <strong>in</strong>flicted <strong>in</strong> several ways:<br />
– a) By destroy<strong>in</strong>g or modify<strong>in</strong>g another<br />
user’s (program) data.<br />
– b) By read<strong>in</strong>g or copy<strong>in</strong>g another user’s<br />
(program) data without permission.<br />
– c) By degrad<strong>in</strong>g the service another user<br />
(program) gets, for example, us<strong>in</strong>g up all<br />
the disk space or geyng more than a fair<br />
share of the process<strong>in</strong>g Cme<br />
[1] Lampson, ProtecCon. Proc. 5th Pr<strong>in</strong>ceton Conf. on Informa2on<br />
Sciences <strong>and</strong> Systems, Pr<strong>in</strong>ceton, 1971<br />
2016 _NOV _<strong>RISC</strong>V_WORKSHOP 9