The-Accountant-Jan-Feb-2018
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
INFORMATION TECHNOLOGY<br />
Types of Cyber Attacks<br />
Cyber-attacks can be categorized into<br />
two distinct categories depending on the<br />
approach employed by the perpetrator;<br />
non-technical attacks and technical<br />
attacks.<br />
Non-technical attack – <strong>The</strong> person<br />
with the malicious intent of committing<br />
cybercrime uses some type of ruse to reel<br />
in the victim who is oblivious (Turban,<br />
2008). Through persuasion and nasty<br />
tricks they cause a person to divulge<br />
information that compromises their<br />
online security; they use the acquired<br />
data against the person.<br />
Technical Attack – When it comes<br />
to the technical approach of cybercrime,<br />
the offenders use software and highly<br />
skilled expertise to perform the offense.<br />
Technical attack has many sub-categories,<br />
some are listed below;<br />
1. Denial of Service (DOS) attack<br />
A person under such an attack may<br />
be unable to access admittance to use<br />
a resource like a webpage because of<br />
overloading. An attacker uses software<br />
that generates numerous data packets<br />
that are used on a targeted computer<br />
network hindering the access.<br />
2. Server/Webpage Hacking<br />
Hackers gain access to a server and then<br />
once infiltration is complete, they’ll<br />
configure the technology to redirect<br />
unsuspecting people to scamming sites<br />
(Turban, 2008). <strong>The</strong> illegal access may<br />
also be for harvesting of data to use later<br />
when they can monetize this information.<br />
3. Malicious Code<br />
This constitutes viruses, worms, and<br />
Trojan horses. Malicious code is<br />
commonly referred to as malware and<br />
may be classified according to how it<br />
spreads. Any form of malicious code<br />
threatens PC performance and can<br />
spread to other devices connected to<br />
the infected computer. This form of<br />
attack is usually meant to destabilize or<br />
completely incapacitate the target.<br />
4. Phishing<br />
A phishing attempt usually involves<br />
tricking on-line users into providing<br />
private information such as credit card<br />
numbers. This could be through sending<br />
spam email that alerts the target to a<br />
problem that requires information to<br />
fix. Phishing has developed into other<br />
sub-groups; spear phishing, vishing<br />
and smishing - that is the use of sms to<br />
infiltrate the system.<br />
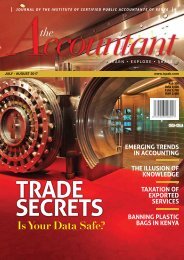
Phishing is among the types of<br />
attacks that boast of an upward positive<br />
graph over the years (Zappa, 2014). It<br />
is a key contributor to the demerits of<br />
cybercrime.<br />
Cybercrime has become a subject of<br />
immense interest worldwide since almost<br />
every facet of life is digitalized (Zappa,<br />
2014). Social media and world spread of<br />
information has helped the crime advance.<br />
Institutions and governments alike have to<br />
work at combating the act so as to avoid<br />
further losses that are predicted to rise even<br />
higher in coming years. It is paramount to<br />
keep ahead of the criminals and ensure<br />
internet security is upheld. An aggressive<br />
approach should be sponsored to develop<br />
a strategy that will combat cyber-crime<br />
and reduce the effects it imposes on the<br />
country and the world as a whole.<br />
JANUARY - FEBRUARY <strong>2018</strong> 47