Network Coding and Wireless Physical-layer ... - Jacobs University
Network Coding and Wireless Physical-layer ... - Jacobs University
Network Coding and Wireless Physical-layer ... - Jacobs University
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
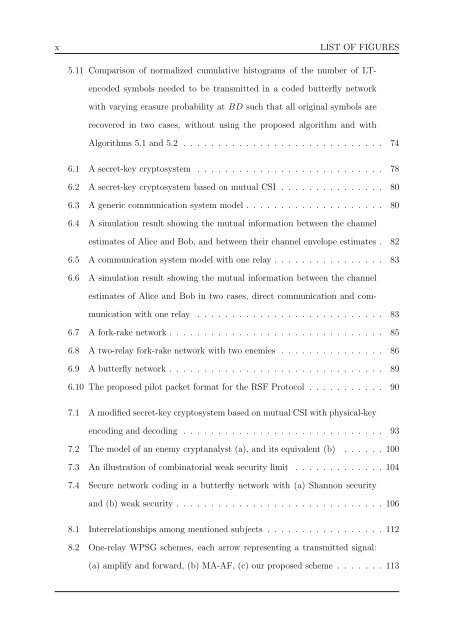
x<br />
LIST OF FIGURES<br />
5.11 Comparison of normalized cumulative histograms of the number of LTencoded<br />
symbols needed to be transmitted in a coded butterfly network<br />
with varying erasure probability at BD such that all original symbols are<br />
recovered in two cases, without using the proposed algorithm <strong>and</strong> with<br />
Algorithms 5.1 <strong>and</strong> 5.2 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 74<br />
6.1 A secret-key cryptosystem . . . . . . . . . . . . . . . . . . . . . . . . . . . 78<br />
6.2 A secret-key cryptosystem based on mutual CSI . . . . . . . . . . . . . . . 80<br />
6.3 A generic communication system model . . . . . . . . . . . . . . . . . . . . 80<br />
6.4 A simulation result showing the mutual information between the channel<br />
estimates of Alice <strong>and</strong> Bob, <strong>and</strong> between their channel envelope estimates . 82<br />
6.5 A communication system model with one relay . . . . . . . . . . . . . . . . 83<br />
6.6 A simulation result showing the mutual information between the channel<br />
estimates of Alice <strong>and</strong> Bob in two cases, direct communication <strong>and</strong> communication<br />
with one relay . . . . . . . . . . . . . . . . . . . . . . . . . . . 83<br />
6.7 A fork-rake network . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 85<br />
6.8 A two-relay fork-rake network with two enemies . . . . . . . . . . . . . . . 86<br />
6.9 A butterfly network . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 89<br />
6.10 The proposed pilot packet format for the RSF Protocol . . . . . . . . . . . 90<br />
7.1 A modified secret-key cryptosystem based on mutual CSI with physical-key<br />
encoding <strong>and</strong> decoding . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 93<br />
7.2 The model of an enemy cryptanalyst (a), <strong>and</strong> its equivalent (b) . . . . . . 100<br />
7.3 An illustration of combinatorial weak security limit . . . . . . . . . . . . . 104<br />
7.4 Secure network coding in a butterfly network with (a) Shannon security<br />
<strong>and</strong> (b) weak security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 106<br />
8.1 Interrelationships among mentioned subjects . . . . . . . . . . . . . . . . . 112<br />
8.2 One-relay WPSG schemes, each arrow representing a transmitted signal:<br />
(a) amplify <strong>and</strong> forward, (b) MA-AF, (c) our proposed scheme . . . . . . . 113