Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
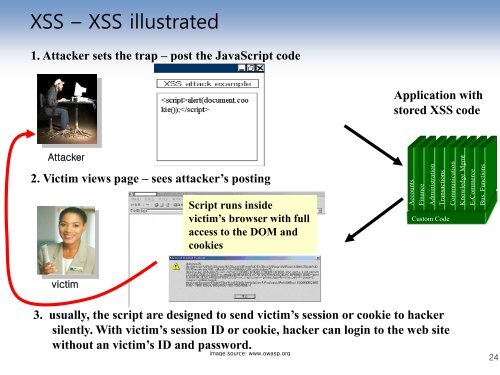
XSS – XSS illustrated<br />
1. Attacker sets <strong>the</strong> trap – post <strong>the</strong> JavaScript code<br />
Application with<br />
s<strong>to</strong>red XSS code<br />
Attacker<br />
2. Victim views page – sees attacker‟s posting<br />
Script runs inside<br />
victim‟s browser with full<br />
access <strong>to</strong> <strong>the</strong> DOM and<br />
cookies<br />
Accounts<br />
Finance<br />
Administration<br />
Transactions<br />
Cus<strong>to</strong>m Code<br />
Communication<br />
Knowledge Mgmt<br />
E-Commerce<br />
Bus. Functions<br />
victim<br />
3. usually, <strong>the</strong> script are designed <strong>to</strong> send victim‟s session or cookie <strong>to</strong> hacker<br />
silently. With victim‟s session ID or cookie, hacker can login <strong>to</strong> <strong>the</strong> web site<br />
without an victim‟s ID and password.<br />
image source: www.owasp.org<br />
24