Click to download Ethernet Basics manual - Grant Industrial Controls
Click to download Ethernet Basics manual - Grant Industrial Controls
Click to download Ethernet Basics manual - Grant Industrial Controls
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
TCP/IP 44<br />
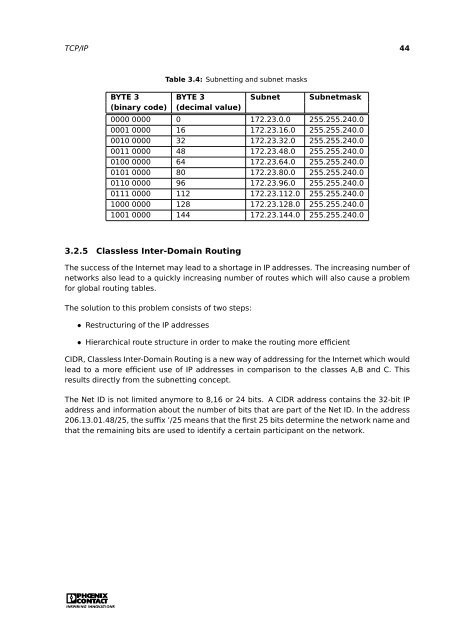
Table 3.4: Subnetting and subnet masks<br />
BYTE 3 BYTE 3 Subnet Subnetmask<br />
(binary code) (decimal value)<br />
0000 0000 0 172.23.0.0 255.255.240.0<br />
0001 0000 16 172.23.16.0 255.255.240.0<br />
0010 0000 32 172.23.32.0 255.255.240.0<br />
0011 0000 48 172.23.48.0 255.255.240.0<br />
0100 0000 64 172.23.64.0 255.255.240.0<br />
0101 0000 80 172.23.80.0 255.255.240.0<br />
0110 0000 96 172.23.96.0 255.255.240.0<br />
0111 0000 112 172.23.112.0 255.255.240.0<br />
1000 0000 128 172.23.128.0 255.255.240.0<br />
1001 0000 144 172.23.144.0 255.255.240.0<br />
3.2.5 Classless Inter-Domain Routing<br />
The success of the Internet may lead <strong>to</strong> a shortage in IP addresses. The increasing number of<br />
networks also lead <strong>to</strong> a quickly increasing number of routes which will also cause a problem<br />
for global routing tables.<br />
The solution <strong>to</strong> this problem consists of two steps:<br />
• Restructuring of the IP addresses<br />
• Hierarchical route structure in order <strong>to</strong> make the routing more efficient<br />
CIDR, Classless Inter-Domain Routing is a new way of addressing for the Internet which would<br />
lead <strong>to</strong> a more efficient use of IP addresses in comparison <strong>to</strong> the classes A,B and C. This<br />
results directly from the subnetting concept.<br />
The Net ID is not limited anymore <strong>to</strong> 8,16 or 24 bits. A CIDR address contains the 32-bit IP<br />
address and information about the number of bits that are part of the Net ID. In the address<br />
206.13.01.48/25, the suffix ’/25 means that the first 25 bits determine the network name and<br />
that the remaining bits are used <strong>to</strong> identify a certain participant on the network.