Denial-of-Service(DoS) Attacks
Denial-of-Service(DoS) Attacks
Denial-of-Service(DoS) Attacks
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
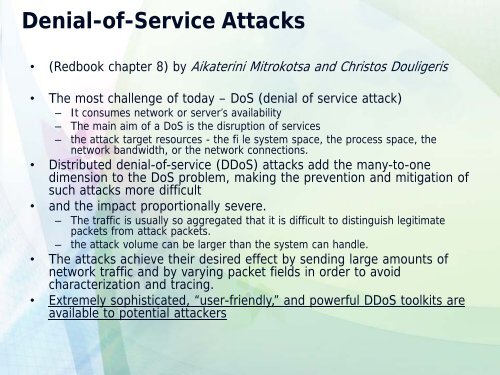
<strong>Denial</strong>-<strong>of</strong>-<strong>Service</strong> <strong>Attacks</strong><br />
• (Redbook chapter 8) by Aikaterini Mitrokotsa and Christos Douligeris<br />
• The most challenge <strong>of</strong> today – <strong>DoS</strong> (denial <strong>of</strong> service attack)<br />
– It consumes network or server’s availability<br />
– The main aim <strong>of</strong> a <strong>DoS</strong> is the disruption <strong>of</strong> services<br />
– the attack target resources - the fi le system space, the process space, the<br />
network bandwidth, or the network connections.<br />
• Distributed denial-<strong>of</strong>-service (D<strong>DoS</strong>) attacks add the many-to-one<br />
dimension to the <strong>DoS</strong> problem, making the prevention and mitigation <strong>of</strong><br />
such attacks more difficult<br />
• and the impact proportionally severe.<br />
– The traffic is usually so aggregated that it is difficult to distinguish legitimate<br />
packets from attack packets.<br />
– the attack volume can be larger than the system can handle.<br />
• The attacks achieve their desired effect by sending large amounts <strong>of</strong><br />
network traffic and by varying packet fields in order to avoid<br />
characterization and tracing.<br />
• Extremely sophisticated, “user-friendly,” and powerful D<strong>DoS</strong> toolkits are<br />
available to potential attackers