Incentives, Pressures, and OpportunitiesMotives for committing <strong>fraud</strong> are numerous and diverse. One executive may believe that the organization’s businessstrategy will ultimately be successful, but interim negative results need to be concealed to give the strategy time.Another needs just a few more pennies per share of income to qualify for a bonus or to meet analysts’ estimates.The third executive purposefully understates income to save for a rainy day.The <strong>fraud</strong> risk identification process should include an assessment of the incentives, pressures, and opportunities tocommit <strong>fraud</strong>. Incentive programs should be evaluated — by the board for senior management and by managementfor others — as to how they may affect employees’ behavior when conducting business or applying professionaljudgment (e.g., estimating bad debt allowances or revenue recognition). Financial incentives and the metrics onwhich they are based can provide a map to where <strong>fraud</strong> is most likely to occur. There may also be nonfinancialincentives, such as when an employee records a fictitious transaction so he or she does not have to explain anotherwise unplanned variance. Even maintaining the status quo is sometimes a powerful enough incentive forpersonnel to commit <strong>fraud</strong>.Also important, and often harder to quantify, are the pressures on individuals to achieve performance or othertargets. Some organizations are transparent, setting specific targets and metrics on which personnel will bemeasured. Other organizations are more indirect and subtle, relying on corporate culture to influence behavior.Individuals may not have any incremental monetary incentive to <strong>fraud</strong>ulently adjust a transaction, but there may beample pressure — real or perceived — on an employee to act <strong>fraud</strong>ulently.Meanwhile, opportunities to commit <strong>fraud</strong> exist throughout organizations and may be reason enough to commit<strong>fraud</strong>. These opportunities are greatest in areas with weak internal controls and a lack of segregation of duties.However, some <strong>fraud</strong>s, especially those committed by management, may be difficult to detect because managementcan often override the controls. Such opportunities are why appropriate monitoring of senior management by astrong board and audit committee, s<strong>up</strong>ported by internal auditing, is critical to <strong>fraud</strong> risk management.Risk of Management’s Override of ControlsAs part of the risk identification process, it is important to consider the potential for management override ofcontrols established to prevent or detect <strong>fraud</strong>. Personnel within the organization generally know the controls andstandard operating procedures that are in place to prevent <strong>fraud</strong>. It is reasonable to assume that individuals whoare intent on committing <strong>fraud</strong> will use their knowledge of the organization’s controls to do it in a manner thatwill conceal their actions. For example, a manager who has the authority to approve new vendors may create andapprove a fictitious vendor and then submit invoices for payment, rather than just submit false invoices for payment.Hence, it is also important to keep the risk of management’s override of controls in mind when evaluating theeffectiveness of controls; an anti-<strong>fraud</strong> control is not effective if it can be overridden easily.Population of Fraud RisksThe <strong>fraud</strong> risk identification process requires an understanding of the universe of <strong>fraud</strong> risks and the subset of risksspecific to the organization. This may involve obtaining information from external sources such as industry news;criminal, civil, and regulatory complaints and settlements; and organizations such as The IIA, AICPA, ACFE, and CICA.23
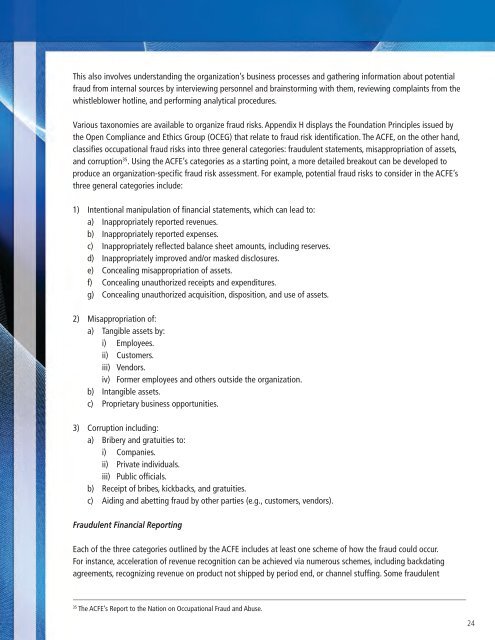
This also involves understanding the organization’s business processes and gathering information about potential<strong>fraud</strong> from internal sources by interviewing personnel and brainstorming with them, reviewing complaints from thewhistleblower hotline, and performing analytical procedures.Various taxonomies are available to organize <strong>fraud</strong> risks. Appendix H displays the Foundation Principles issued bythe Open Compliance and Ethics Gro<strong>up</strong> (OCEG) that relate to <strong>fraud</strong> risk identification. The ACFE, on the other hand,classifies occ<strong>up</strong>ational <strong>fraud</strong> risks into three general categories: <strong>fraud</strong>ulent statements, misappropriation of assets,and corr<strong>up</strong>tion 35 . Using the ACFE’s categories as a starting point, a more detailed breakout can be developed toproduce an organization-specific <strong>fraud</strong> risk assessment. For example, potential <strong>fraud</strong> risks to consider in the ACFE’sthree general categories include:1) Intentional manipulation of financial statements, which can lead to:a) Inappropriately reported revenues.b) Inappropriately reported expenses.c) Inappropriately reflected balance sheet amounts, including reserves.d) Inappropriately improved and/or masked disclosures.e) Concealing misappropriation of assets.f) Concealing unauthorized receipts and expenditures.g) Concealing unauthorized acquisition, disposition, and use of assets.2) Misappropriation of:a) Tangible assets by:i) Employees.ii) Customers.iii) Vendors.iv) Former employees and others outside the organization.b) Intangible assets.c) Proprietary business opportunities.3) Corr<strong>up</strong>tion including:a) Bribery and gratuities to:i) Companies.ii) Private individuals.iii) Public officials.b) Receipt of bribes, kickbacks, and gratuities.c) Aiding and abetting <strong>fraud</strong> by other parties (e.g., customers, vendors).Fraudulent Financial ReportingEach of the three categories outlined by the ACFE includes at least one scheme of how the <strong>fraud</strong> could occur.For instance, acceleration of revenue recognition can be achieved via numerous schemes, including backdatingagreements, recognizing revenue on product not shipped by period end, or channel stuffing. Some <strong>fraud</strong>ulent35The ACFE’s Report to the Nation on Occ<strong>up</strong>ational Fraud and Abuse.24
- Page 1 and 2: ACFE FRAUD PREVENTIONCHECK-UP
- Page 3 and 4: ACFE FRAUD PREVENTIONCHECK-UPThe Be
- Page 5 and 6: ACFE FRAUD PREVENTIONCHECK-UPACFE F
- Page 7 and 8: ACFE FRAUD PREVENTIONCHECK-UPACFE F
- Page 9 and 10: ACFE FRAUD PREVENTIONCHECK-UPACFE F
- Page 11 and 12: ACFE FRAUD PREVENTIONCHECK-UPACFE F
- Page 13 and 14: Sponsored by:The Institute of Inter
- Page 15 and 16: Team Members:Toby J.F. Bishop, CPA,
- Page 17 and 18: Managing the Business Risk of Fraud
- Page 19 and 20: establish their own fraud risk mana
- Page 21 and 22: Fraud risk identification may inclu
- Page 23 and 24: Thus, to properly address fraud ris
- Page 25 and 26: The board also has the responsibili
- Page 27 and 28: • Implementing adequate internal
- Page 29 and 30: Fraud Risk Management Program Compo
- Page 31 and 32: ecently been hired in the purchasin
- Page 33 and 34: Organizations can identify and asse
- Page 35: The Risk Assessment TeamA good risk
- Page 39 and 40: - Invoices for goods not received o
- Page 41 and 42: Other RisksRegulatory and Legal Mis
- Page 43 and 44: SECTION 3: FRAUD PREVENTIONPrincipl
- Page 45 and 46: An organization’s HR group is oft
- Page 47 and 48: SECTION 4: FRAUD DETECTIONPrinciple
- Page 49 and 50: Process ControlsProcess controls sp
- Page 51 and 52: keep such information confidential.
- Page 53 and 54: will vary depending on the nature,
- Page 55 and 56: Conducting the InvestigationPlannin
- Page 57 and 58: • Extended investigation — Cond
- Page 59 and 60: Fraud ControlsDeloitte Forensic Cen
- Page 61 and 62: APPENDIX B: SAMPLE FRAMEWORK FOR A
- Page 63 and 64: APPENDIX C: SAMPLE FRAUD POLICY 41N
- Page 65 and 66: CONFIDENTIALITYThe ______________ U
- Page 67 and 68: Sample Fraud Policy Decision Matrix
- Page 69 and 70: Identified Fraud Risksand Schemes (
- Page 71 and 72: 2) Misappropriation of:a) Tangible
- Page 73 and 74: ) Embezzlement(1) False accounting
- Page 75 and 76: Fraud Prevention Area, Factor, or C
- Page 77 and 78: Fraud Prevention Area, Factor, or C
- Page 79 and 80: Fraud Prevention Area, Factor, or C
- Page 81 and 82: Fraud Prevention Area, Factor, or C
- Page 83 and 84: O-Organization / PersonnelO1-Leader
- Page 85 and 86: O4.3 Enhance Operational Skills & C
- Page 87 and 88:
PR-Prevent, Protect & PreparePR1-Ge
- Page 89 and 90:
E-Periodic EvaluationE1-Evaluation
- Page 91 and 92:
I2-CommunicationI2.1 Develop Commun
- Page 93 and 94:
CriminologyFraud Prevention Program
- Page 95 and 96:
CriminologyFraud Prevention Program
- Page 97 and 98:
CriminologyFraud Prevention Program
- Page 99 and 100:
CriminologyFraud Prevention Program
- Page 101 and 102:
CriminologyFraud Prevention Program
- Page 103 and 104:
CriminologyFraud Prevention Program
- Page 105 and 106:
CriminologyFraud Prevention Program
- Page 107 and 108:
CriminologyFraud Prevention Program
- Page 109 and 110:
CriminologyFraud Prevention Program
- Page 111 and 112:
CriminologyFraud Prevention Program
- Page 113 and 114:
CriminologyFraud Prevention Program
- Page 115 and 116:
CriminologyFraud Prevention Program
- Page 117 and 118:
Sample Fraud PolicyAssociation of C
- Page 119 and 120:
Sample Fraud PolicyCONFIDENTIALITYT
- Page 121 and 122:
Sample Fraud PolicyFraud Policy Dec
- Page 123 and 124:
Fraud’s Worst Enemyhttp://www.fra
- Page 125 and 126:
ACFE Insights - ACFE Insightshttp:/
- Page 127:
ACFE Insights - ACFE Insightshttp:/