AUDIT ANALYTICS AUDIT
1JWn3ix
1JWn3ix
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>AUDIT</strong> <strong>ANALYTICS</strong> AND CONTINUOUS <strong>AUDIT</strong>:LOOKING TOWARD THE FUTURE<br />
operational reasons. The need to monitor and assure control settings and<br />
the nature of overrides generated a new type of audit objective and<br />
process.<br />
Data<br />
Data is in general stored in ERPs, in files for legacy systems, or in more<br />
recent times in large repositories external to the organization that are<br />
called big data (Vasarhelyi, Kogan, and Tuttle; 2015). The access to these<br />
data for observation, monitoring, or mass retrieval requires the auditor’s<br />
knowledge and extensive use of software tools. This access is not only<br />
technically challenging but also organizationally difficult (Vasarhelyi,<br />
Romero, Kuenkaikaew, and Littley; 2012).<br />
1.2 Conceptualizing Various Elements of CA<br />
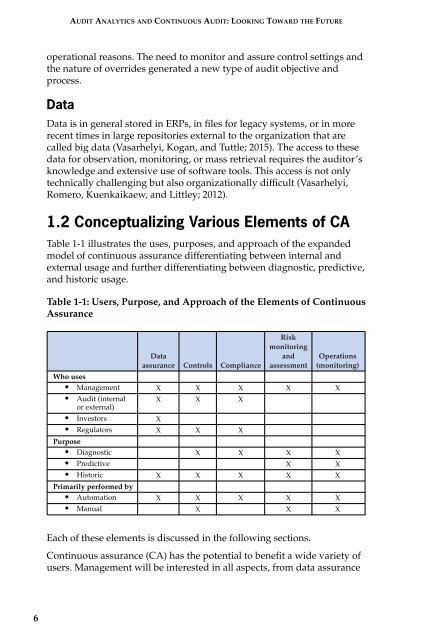
Table 1-1 illustrates the uses, purposes, and approach of the expanded<br />
model of continuous assurance differentiating between internal and<br />
external usage and further differentiating between diagnostic, predictive,<br />
and historic usage.<br />
Table 1-1: Users, Purpose, and Approach of the Elements of Continuous<br />
Assurance<br />
Data<br />
assurance Controls Compliance<br />
Risk<br />
monitoring<br />
and<br />
assessment<br />
Operations<br />
(monitoring)<br />
Who uses<br />
• Management X X X X X<br />
• Audit (internal X X X<br />
or external)<br />
• Investors<br />
X<br />
• Regulators X X X<br />
Purpose<br />
• Diagnostic X X X X<br />
• Predictive X X<br />
• Historic X X X X X<br />
Primarily performed by<br />
• Automation X X X X X<br />
• Manual X X X<br />
Each of these elements is discussed in the following sections.<br />
Continuous assurance (CA) has the potential to benefit a wide variety of<br />
users. Management will be interested in all aspects, from data assurance<br />
6