SCHOOL THESIS
?view&did=788526
?view&did=788526
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
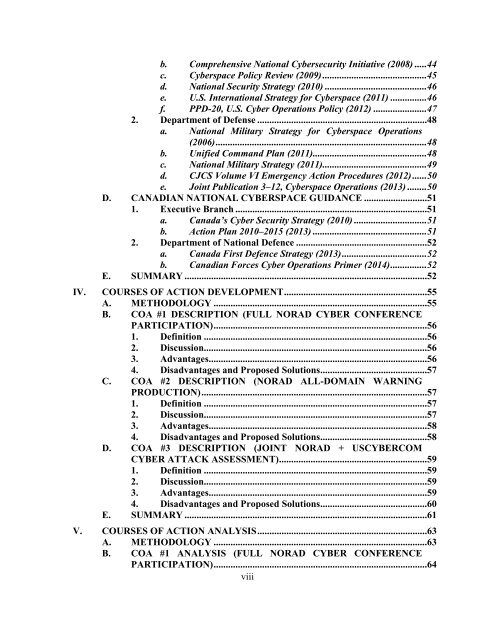
. Comprehensive National Cybersecurity Initiative (2008) .....44<br />
c. Cyberspace Policy Review (2009)...........................................45<br />
d. National Security Strategy (2010) ..........................................46<br />
e. U.S. International Strategy for Cyberspace (2011) ...............46<br />
f. PPD-20, U.S. Cyber Operations Policy (2012) ......................47<br />
2. Department of Defense ......................................................................48<br />
a. National Military Strategy for Cyberspace Operations<br />
(2006).......................................................................................48<br />
b. Unified Command Plan (2011)...............................................48<br />
c. National Military Strategy (2011)...........................................49<br />
d. CJCS Volume VI Emergency Action Procedures (2012)......50<br />
e. Joint Publication 3–12, Cyberspace Operations (2013) ........50<br />
D. CANADIAN NATIONAL CYBERSPACE GUIDANCE ..........................51<br />
1. Executive Branch ...............................................................................51<br />
a. Canada’s Cyber Security Strategy (2010) ..............................51<br />
b. Action Plan 2010–2015 (2013) ...............................................51<br />
2. Department of National Defence ......................................................52<br />
a. Canada First Defence Strategy (2013)...................................52<br />
b. Canadian Forces Cyber Operations Primer (2014)...............52<br />
E. SUMMARY ....................................................................................................52<br />
IV. COURSES OF ACTION DEVELOPMENT ...........................................................55<br />
A. METHODOLOGY ........................................................................................55<br />
B. COA #1 DESCRIPTION (FULL NORAD CYBER CONFERENCE<br />
PARTICIPATION) ........................................................................................56<br />
1. Definition ............................................................................................56<br />
2. Discussion............................................................................................56<br />
3. Advantages..........................................................................................56<br />
4. Disadvantages and Proposed Solutions ............................................57<br />
C. COA #2 DESCRIPTION (NORAD ALL-DOMAIN WARNING<br />
PRODUCTION) .............................................................................................57<br />
1. Definition ............................................................................................57<br />
2. Discussion............................................................................................57<br />
3. Advantages..........................................................................................58<br />
4. Disadvantages and Proposed Solutions ............................................58<br />
D. COA #3 DESCRIPTION (JOINT NORAD + USCYBERCOM<br />
CYBER ATTACK ASSESSMENT) .............................................................59<br />
1. Definition ............................................................................................59<br />
2. Discussion............................................................................................59<br />
3. Advantages..........................................................................................59<br />
4. Disadvantages and Proposed Solutions ............................................60<br />
E. SUMMARY ....................................................................................................61<br />
V. COURSES OF ACTION ANALYSIS ......................................................................63<br />
A. METHODOLOGY ........................................................................................63<br />
B. COA #1 ANALYSIS (FULL NORAD CYBER CONFERENCE<br />
PARTICIPATION) ........................................................................................64<br />
viii