Security analysis of Dutch smart metering systems - Multiple Choices
Security analysis of Dutch smart metering systems - Multiple Choices
Security analysis of Dutch smart metering systems - Multiple Choices
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
4.1 Port P0 4 PRACTICAL ANALYSIS<br />
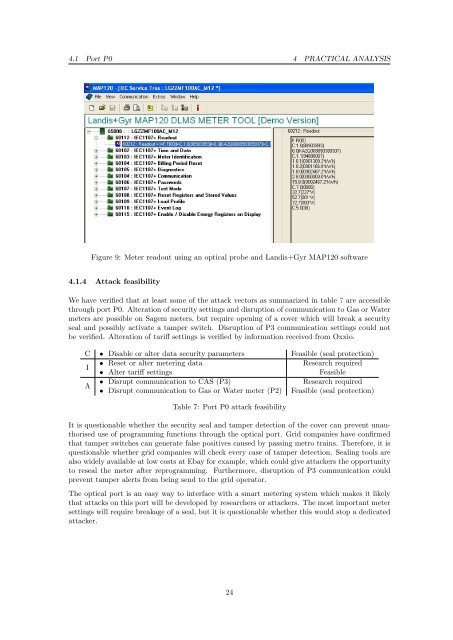
Figure 9: Meter readout using an optical probe and Landis+Gyr MAP120 s<strong>of</strong>tware<br />
4.1.4 Attack feasibility<br />
We have verified that at least some <strong>of</strong> the attack vectors as summarized in table 7 are accessible<br />
through port P0. Alteration <strong>of</strong> security settings and disruption <strong>of</strong> communication to Gas or Water<br />
meters are possible on Sagem meters, but require opening <strong>of</strong> a cover which will break a security<br />
seal and possibly activate a tamper switch. Disruption <strong>of</strong> P3 communication settings could not<br />
be verified. Alteration <strong>of</strong> tariff settings is verified by information received from Oxxio.<br />
C • Disable or alter data security parameters Feasible (seal protection)<br />
I<br />
• Reset or alter <strong>metering</strong> data<br />
• Alter tariff settings<br />
Research required<br />
Feasible<br />
A<br />
• Disrupt communication to CAS (P3)<br />
• Disrupt communication to Gas or Water meter (P2)<br />
Research required<br />
Feasible (seal protection)<br />
Table 7: Port P0 attack feasibility<br />
It is questionable whether the security seal and tamper detection <strong>of</strong> the cover can prevent unauthorised<br />
use <strong>of</strong> programming functions through the optical port. Grid companies have confirmed<br />
that tamper switches can generate false positives caused by passing metro trains. Therefore, it is<br />
questionable whether grid companies will check every case <strong>of</strong> tamper detection. Sealing tools are<br />
also widely available at low costs at Ebay for example, which could give attackers the opportunity<br />
to reseal the meter after reprogramming. Furthermore, disruption <strong>of</strong> P3 communication could<br />
prevent tamper alerts from being send to the grid operator.<br />
The optical port is an easy way to interface with a <strong>smart</strong> <strong>metering</strong> system which makes it likely<br />
that attacks on this port will be developed by researchers or attackers. The most important meter<br />
settings will require breakage <strong>of</strong> a seal, but it is questionable whether this would stop a dedicated<br />
attacker.<br />
24