Download - D-Link
Download - D-Link
Download - D-Link
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
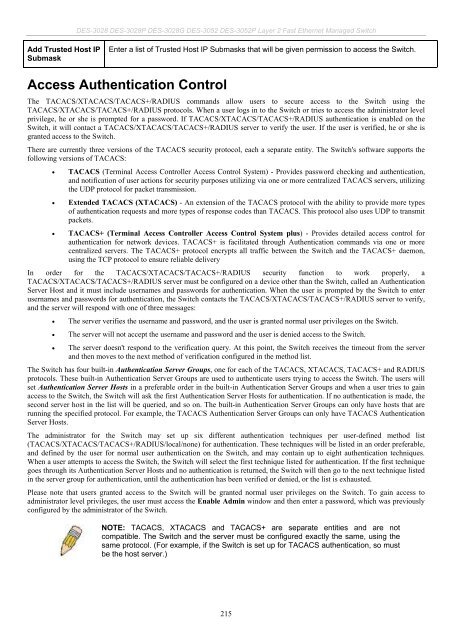
Add Trusted Host IP<br />
Submask<br />
DES-3028 DES-3028P DES-3028G DES-3052 DES-3052P Layer 2 Fast Ethernet Managed Switch<br />
Enter a list of Trusted Host IP Submasks that will be given permission to access the Switch.<br />
Access Authentication Control<br />
The TACACS/XTACACS/TACACS+/RADIUS commands allow users to secure access to the Switch using the<br />
TACACS/XTACACS/TACACS+/RADIUS protocols. When a user logs in to the Switch or tries to access the administrator level<br />
privilege, he or she is prompted for a password. If TACACS/XTACACS/TACACS+/RADIUS authentication is enabled on the<br />
Switch, it will contact a TACACS/XTACACS/TACACS+/RADIUS server to verify the user. If the user is verified, he or she is<br />
granted access to the Switch.<br />
There are currently three versions of the TACACS security protocol, each a separate entity. The Switch's software supports the<br />
following versions of TACACS:<br />
TACACS (Terminal Access Controller Access Control System) - Provides password checking and authentication,<br />
and notification of user actions for security purposes utilizing via one or more centralized TACACS servers, utilizing<br />
the UDP protocol for packet transmission.<br />
Extended TACACS (XTACACS) - An extension of the TACACS protocol with the ability to provide more types<br />
of authentication requests and more types of response codes than TACACS. This protocol also uses UDP to transmit<br />
packets.<br />
TACACS+ (Terminal Access Controller Access Control System plus) - Provides detailed access control for<br />
authentication for network devices. TACACS+ is facilitated through Authentication commands via one or more<br />
centralized servers. The TACACS+ protocol encrypts all traffic between the Switch and the TACACS+ daemon,<br />
using the TCP protocol to ensure reliable delivery<br />
In order for the TACACS/XTACACS/TACACS+/RADIUS security function to work properly, a<br />
TACACS/XTACACS/TACACS+/RADIUS server must be configured on a device other than the Switch, called an Authentication<br />
Server Host and it must include usernames and passwords for authentication. When the user is prompted by the Switch to enter<br />
usernames and passwords for authentication, the Switch contacts the TACACS/XTACACS/TACACS+/RADIUS server to verify,<br />
and the server will respond with one of three messages:<br />
The server verifies the username and password, and the user is granted normal user privileges on the Switch.<br />
The server will not accept the username and password and the user is denied access to the Switch.<br />
The server doesn't respond to the verification query. At this point, the Switch receives the timeout from the server<br />
and then moves to the next method of verification configured in the method list.<br />
The Switch has four built-in Authentication Server Groups, one for each of the TACACS, XTACACS, TACACS+ and RADIUS<br />
protocols. These built-in Authentication Server Groups are used to authenticate users trying to access the Switch. The users will<br />
set Authentication Server Hosts in a preferable order in the built-in Authentication Server Groups and when a user tries to gain<br />
access to the Switch, the Switch will ask the first Authentication Server Hosts for authentication. If no authentication is made, the<br />
second server host in the list will be queried, and so on. The built-in Authentication Server Groups can only have hosts that are<br />
running the specified protocol. For example, the TACACS Authentication Server Groups can only have TACACS Authentication<br />
Server Hosts.<br />
The administrator for the Switch may set up six different authentication techniques per user-defined method list<br />
(TACACS/XTACACS/TACACS+/RADIUS/local/none) for authentication. These techniques will be listed in an order preferable,<br />
and defined by the user for normal user authentication on the Switch, and may contain up to eight authentication techniques.<br />
When a user attempts to access the Switch, the Switch will select the first technique listed for authentication. If the first technique<br />
goes through its Authentication Server Hosts and no authentication is returned, the Switch will then go to the next technique listed<br />
in the server group for authentication, until the authentication has been verified or denied, or the list is exhausted.<br />
Please note that users granted access to the Switch will be granted normal user privileges on the Switch. To gain access to<br />
administrator level privileges, the user must access the Enable Admin window and then enter a password, which was previously<br />
configured by the administrator of the Switch.<br />
NOTE: TACACS, XTACACS and TACACS+ are separate entities and are not<br />
compatible. The Switch and the server must be configured exactly the same, using the<br />
same protocol. (For example, if the Switch is set up for TACACS authentication, so must<br />
be the host server.)<br />
215