Download - D-Link
Download - D-Link
Download - D-Link
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
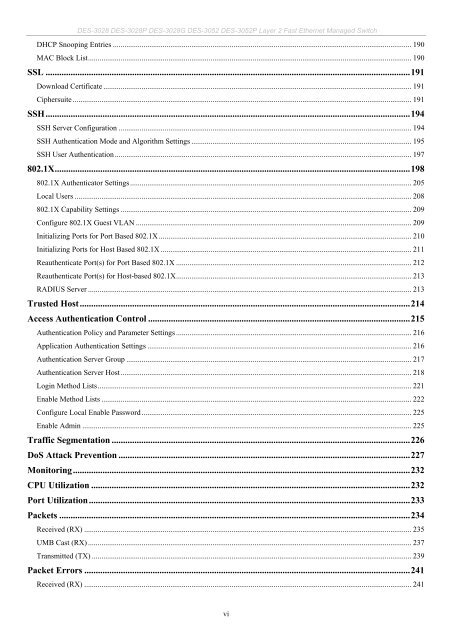
DES-3028 DES-3028P DES-3028G DES-3052 DES-3052P Layer 2 Fast Ethernet Managed Switch<br />
DHCP Snooping Entries ............................................................................................................................................................ 190<br />
MAC Block List......................................................................................................................................................................... 190<br />
SSL ................................................................................................................................................................191<br />
<strong>Download</strong> Certificate ................................................................................................................................................................. 191<br />
Ciphersuite ................................................................................................................................................................................. 191<br />
SSH................................................................................................................................................................194<br />
SSH Server Configuration ......................................................................................................................................................... 194<br />
SSH Authentication Mode and Algorithm Settings ................................................................................................................... 195<br />
SSH User Authentication ........................................................................................................................................................... 197<br />
802.1X............................................................................................................................................................198<br />
802.1X Authenticator Settings ................................................................................................................................................... 205<br />
Local Users ................................................................................................................................................................................ 208<br />
802.1X Capability Settings ........................................................................................................................................................ 209<br />
Configure 802.1X Guest VLAN ................................................................................................................................................ 209<br />
Initializing Ports for Port Based 802.1X .................................................................................................................................... 210<br />
Initializing Ports for Host Based 802.1X ................................................................................................................................... 211<br />
Reauthenticate Port(s) for Port Based 802.1X ........................................................................................................................... 212<br />
Reauthenticate Port(s) for Host-based 802.1X........................................................................................................................... 213<br />
RADIUS Server ......................................................................................................................................................................... 213<br />
Trusted Host.................................................................................................................................................214<br />
Access Authentication Control ...................................................................................................................215<br />
Authentication Policy and Parameter Settings ........................................................................................................................... 216<br />
Application Authentication Settings .......................................................................................................................................... 216<br />
Authentication Server Group ..................................................................................................................................................... 217<br />
Authentication Server Host........................................................................................................................................................ 218<br />
Login Method Lists.................................................................................................................................................................... 221<br />
Enable Method Lists .................................................................................................................................................................. 222<br />
Configure Local Enable Password ............................................................................................................................................. 225<br />
Enable Admin ............................................................................................................................................................................ 225<br />
Traffic Segmentation ...................................................................................................................................226<br />
DoS Attack Prevention ................................................................................................................................227<br />
Monitoring....................................................................................................................................................232<br />
CPU Utilization ............................................................................................................................................232<br />
Port Utilization.............................................................................................................................................233<br />
Packets ..........................................................................................................................................................234<br />
Received (RX) ........................................................................................................................................................................... 235<br />
UMB Cast (RX) ......................................................................................................................................................................... 237<br />
Transmitted (TX) ....................................................................................................................................................................... 239<br />
Packet Errors ...............................................................................................................................................241<br />
Received (RX) ........................................................................................................................................................................... 241<br />
vi