1BO4r2U
1BO4r2U
1BO4r2U
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
35 36<br />
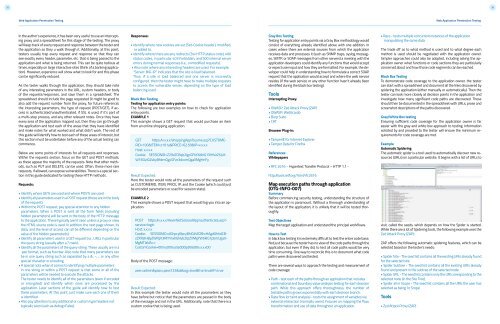
Web Application Penetration Testing<br />
Web Application Penetration Testing<br />
In the author’s experience, it has been very useful to use an intercepting<br />
proxy and a spreadsheet for this stage of the testing. The proxy<br />
will keep track of every request and response between the tester and<br />
the application as they u walk through it. Additionally, at this point,<br />
testers usually trap every request and response so that they can<br />
see exactly every header, parameter, etc. that is being passed to the<br />
application and what is being returned. This can be quite tedious at<br />
times, especially on large interactive sites (think of a banking application).<br />
However, experience will show what to look for and this phase<br />
can be significantly reduced.<br />
As the tester walks through the application, they should take note<br />
of any interesting parameters in the URL, custom headers, or body<br />
of the requests/responses, and save them in a spreadsheet. The<br />
spreadsheet should include the page requested (it might be good to<br />
also add the request number from the proxy, for future reference),<br />
the interesting parameters, the type of request (POST/GET), if access<br />
is authenticated/unauthenticated, if SSL is used, if it’s part of<br />
a multi-step process, and any other relevant notes. Once they have<br />
every area of the application mapped out, then they can go through<br />
the application and test each of the areas that they have identified<br />
and make notes for what worked and what didn’t work. The rest of<br />
this guide will identify how to test each of these areas of interest, but<br />
this section must be undertaken before any of the actual testing can<br />
commence.<br />
Below are some points of interests for all requests and responses.<br />
Within the requests section, focus on the GET and POST methods,<br />
as these appear the majority of the requests. Note that other methods,<br />
such as PUT and DELETE, can be used. Often, these more rare<br />
requests, if allowed, can expose vulnerabilities. There is a special section<br />
in this guide dedicated for testing these HTTP methods.<br />
Requests:<br />
• Identify where GETs are used and where POSTs are used.<br />
• Identify all parameters used in a POST request (these are in the body<br />
of the request).<br />
• Within the POST request, pay special attention to any hidden<br />
parameters. When a POST is sent all the form fields (including<br />
hidden parameters) will be sent in the body of the HTTP message<br />
to the application. These typically aren’t seen unless a proxy or view<br />
the HTML source code is used. In addition, the next page shown, its<br />
data, and the level of access can all be different depending on the<br />
value of the hidden parameter(s).<br />
• Identify all parameters used in a GET request (i.e., URL), in particular<br />
the query string (usually after a ? mark).<br />
• Identify all the parameters of the query string. These usually are in a<br />
pair format, such as foo=bar. Also note that many parameters can<br />
be in one query string such as separated by a &, ~, :, or any other<br />
special character or encoding.<br />
• A special note when it comes to identifying multiple parameters<br />
in one string or within a POST request is that some or all of the<br />
parameters will be needed to execute the attacks.<br />
The tester needs to identify all of the parameters (even if encoded<br />
or encrypted) and identify which ones are processed by the<br />
application. Later sections of the guide will identify how to test<br />
these parameters. At this point, just make sure each one of them<br />
is identified.<br />
• Also pay attention to any additional or custom type headers not<br />
typically seen (such as debug=False).<br />
Responses:<br />
• Identify where new cookies are set (Set-Cookie header), modified,<br />
or added to.<br />
• Identify where there are any redirects (3xx HTTP status code), 400<br />
status codes, in particular 403 Forbidden, and 500 internal server<br />
errors during normal responses (i.e., unmodified requests).<br />
• Also note where any interesting headers are used. For example,<br />
“Server: BIG-IP” indicates that the site is load balanced.<br />
Thus, if a site is load balanced and one server is incorrectly<br />
configured, then the tester might have to make multiple requests<br />
to access the vulnerable server, depending on the type of load<br />
balancing used.<br />
Black Box Testing<br />
Testing for application entry points:<br />
The following are two examples on how to check for application<br />
entry points.<br />
EXAMPLE 1<br />
This example shows a GET request that would purchase an item<br />
from an online shopping application.<br />
GET https:/x.x.x.x/shoppingApp/buyme.asp?CUSTOME-<br />
RID=100&ITEM=z101a&PRICE=62.50&IP=x.x.x.x<br />
Host: x.x.x.x<br />
Cookie: SESSIONID=Z29vZCBqb2IgcGFkYXdhIG15IHVzZXJuY-<br />
W1lIGlzIGZvbyBhbmQgcGFzc3dvcmQgaXMgYmFy<br />
Result Expected:<br />
Here the tester would note all the parameters of the request such<br />
as CUSTOMERID, ITEM, PRICE, IP, and the Cookie (which could just<br />
be encoded parameters or used for session state).<br />
EXAMPLE 2<br />
This example shows a POST request that would log you into an application.<br />
POST https:/x.x.x.x/KevinNotSoGoodApp/authenticate.asp?-<br />
service=login<br />
Host: x.x.x.x<br />
Cookie: SESSIONID=dGhpcyBpcyBhIGJhZCBhcHAgdGhhdCB-<br />
zZXRzIHByZWRpY3RhYmxlIGNvb2tpZXMgYW5kIG1pbmUgaX-<br />
MgMTIzNA==<br />
CustomCookie=00my00trusted00ip00is00x.x.x.x00<br />
Body of the POST message:<br />
user=admin&pass=pass123&debug=true&fromtrustIP=true<br />
Result Expected:<br />
In this example the tester would note all the parameters as they<br />
have before but notice that the parameters are passed in the body<br />
of the message and not in the URL. Additionally, note that there is a<br />
custom cookie that is being used.<br />
Gray Box Testing<br />
Testing for application entry points via a Gray Box methodology would<br />
consist of everything already identified above with one addition. In<br />
cases where there are external sources from which the application<br />
receives data and processes it (such as SNMP traps, syslog messages,<br />
SMTP, or SOAP messages from other servers) a meeting with the<br />
application developers could identify any functions that would accept<br />
or expect user input and how they are formatted. For example, the developer<br />
could help in understanding how to formulate a correct SOAP<br />
request that the application would accept and where the web service<br />
resides (if the web service or any other function hasn’t already been<br />
identified during the black box testing).<br />
Tools<br />
Intercepting Proxy:<br />
• OWASP: Zed Attack Proxy (ZAP)<br />
• OWASP: WebScarab<br />
• Burp Suite<br />
• CAT<br />
Browser Plug-in:<br />
• TamperIE for Internet Explorer<br />
• Tamper Data for Firefox<br />
References<br />
Whitepapers<br />
• RFC 2616 – Hypertext Transfer Protocol – HTTP 1.1 -<br />
http:/tools.ietf.org/html/rfc2616<br />
Map execution paths through application<br />
(OTG-INFO-007)<br />
Summary<br />
Before commencing security testing, understanding the structure of<br />
the application is paramount. Without a thorough understanding of<br />
the layout of the application, it is unlkely that it will be tested thoroughly.<br />
Test Objectives<br />
Map the target application and understand the principal workflows.<br />
How to Test<br />
In black box testing it is extremely difficult to test the entire code base.<br />
Not just because the tester has no view of the code paths through the<br />
application, but even if they did, to test all code paths would be very<br />
time consuming. One way to reconcile this is to document what code<br />
paths were discovered and tested.<br />
There are several ways to approach the testing and measurement of<br />
code coverage:<br />
• Path - test each of the paths through an application that includes<br />
combinatorial and boundary value analysis testing for each decision<br />
path. While this approach offers thoroughness, the number of<br />
testable paths grows exponentially with each decision branch.<br />
• Data flow (or taint analysis) - tests the assignment of variables via<br />
external interaction (normally users). Focuses on mapping the flow,<br />
transformation and use of data throughout an application.<br />
• Race - tests multiple concurrent instances of the application<br />
manipulating the same data.<br />
The trade off as to what method is used and to what degree each<br />
method is used should be negotiated with the application owner.<br />
Simpler approaches could also be adopted, including asking the application<br />
owner what functions or code sections they are particularly<br />
concerned about and how those code segments can be reached.<br />
Black Box Testing<br />
To demonstrate code coverage to the application owner, the tester<br />
can start with a spreadsheet and document all the links discovered by<br />
spidering the application (either manually or automatically). Then the<br />
tester can look more closely at decision points in the application and<br />
investigate how many significant code paths are discovered. These<br />
should then be documented in the spreadsheet with URLs, prose and<br />
screenshot descriptions of the paths discovered.<br />
Gray/White Box testing<br />
Ensuring sufficient code coverage for the application owner is far<br />
easier with the gray and white box approach to testing. Information<br />
solicited by and provided to the tester will ensure the minimum requirements<br />
for code coverage are met.<br />
Example<br />
Automatic Spidering<br />
The automatic spider is a tool used to automatically discover new resources<br />
(URLs) on a particular website. It begins with a list of URLs to<br />
visit, called the seeds, which depends on how the Spider is started.<br />
While there are a lot of Spidering tools, the following example uses the<br />
Zed Attack Proxy (ZAP):<br />
ZAP offers the following automatic spidering features, which can be<br />
selected based on the tester’s needs:<br />
• Spider Site - The seed list contains all the existing URIs already found<br />
for the selected site.<br />
• Spider Subtree - The seed list contains all the existing URIs already<br />
found and present in the subtree of the selected node.<br />
• Spider URL - The seed list contains only the URI corresponding to the<br />
selected node (in the Site Tree).<br />
• Spider all in Scope - The seed list contains all the URIs the user has<br />
selected as being ‘In Scope’.<br />
Tools<br />
• Zed Attack Proxy (ZAP)