1BO4r2U
1BO4r2U
1BO4r2U
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
101 102<br />
Web Application Penetration Testing<br />
Web Application Penetration Testing<br />
BeEF is the browser exploitation framework. A professional tool<br />
to demonstrate the real-time impact of browser vulnerabilities.<br />
• XSS-Proxy - http: /xss-proxy.sourceforge.net/<br />
XSS-Proxy is an advanced Cross-Site-Scripting (XSS) attack tool.<br />
• Backframe - http: /www.gnucitizen.org/projects/backframe/<br />
Backframe is a full-featured attack console for exploiting WEB<br />
browsers, WEB users, and WEB applications.<br />
• WebScarab<br />
WebScarab is a framework for analyzing applications that communicate<br />
using the HTTP and HTTPS protocols.<br />
• Burp - http: /portswigger.net/burp/<br />
Burp Proxy is an interactive HTTP/S proxy server for attacking and<br />
testing web applications.<br />
• XSS Assistant - http: /www.greasespot.net/<br />
Greasemonkey script that allow users to easily test any web application<br />
for cross-site-scripting flaws.<br />
• OWASP Zed Attack Proxy (ZAP) - OWASP_Zed_Attack_Proxy_<br />
Project<br />
ZAP is an easy to use integrated penetration testing tool for finding<br />
vulnerabilities in web applications. It is designed to be used<br />
by people with a wide range of security experience and as such is<br />
ideal for developers and functional testers who are new to penetration<br />
testing. ZAP provides automated scanners as well as a set<br />
of tools that allow you to find security vulnerabilities manually.<br />
References<br />
OWASP Resources<br />
• XSS Filter Evasion Cheat Sheet<br />
Books<br />
• Joel Scambray, Mike Shema, Caleb Sima - “Hacking Exposed<br />
Web Applications”, Second Edition, McGraw-Hill, 2006 - ISBN<br />
0-07-226229-0<br />
• Dafydd Stuttard, Marcus Pinto - “The Web Application’s Handbook<br />
- Discovering and Exploiting Security Flaws”, 2008, Wiley,<br />
ISBN 978-0-470-17077-9<br />
• Jeremiah Grossman, Robert “RSnake” Hansen, Petko “pdp” D.<br />
Petkov, Anton Rager, Seth Fogie - “Cross Site Scripting Attacks:<br />
XSS Exploits and Defense”, 2007, Syngress, ISBN-10: 1-59749-<br />
154-3<br />
MIME%20Types.pdf<br />
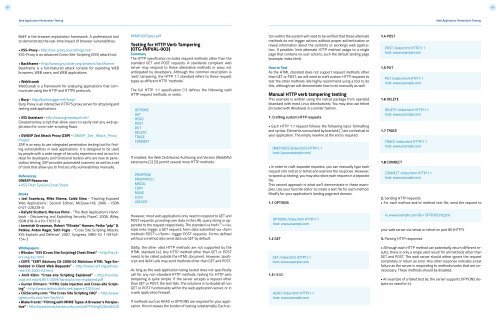
Testing for HTTP Verb Tampering<br />
(OTG-INPVAL-003)<br />
Summary<br />
The HTTP specification includes request methods other than the<br />
standard GET and POST requests. A standards compliant web<br />
server may respond to these alternative methods in ways not<br />
anticipated by developers. Although the common description is<br />
‘verb’ tampering, the HTTP 1.1 standard refers to these request<br />
types as different HTTP ‘methods.’<br />
The full HTTP 1.1 specification [1] defines the following valid<br />
HTTP request methods, or verbs:<br />
OPTIONS<br />
GET<br />
HEAD<br />
POST<br />
PUT<br />
DELETE<br />
TRACE<br />
CONNECT<br />
If enabled, the Web Distributed Authoring and Version (WebDAV)<br />
extensions [2] [3] permit several more HTTP methods:<br />
PROPFIND<br />
PROPPATCH<br />
MKCOL<br />
COPY<br />
MOVE<br />
LOCK<br />
UNLOCK<br />
However, most web applications only need to respond to GET and<br />
POST requests, providing user data in the URL query string or appended<br />
to the request respectively. The standard <br />
style links trigger a GET request; form data submitted via trigger POST requests. Forms defined<br />
without a method also send data via GET by default.<br />
tion within the system will need to be verified that these alternate<br />
methods do not trigger actions without proper authentication or<br />
reveal information about the contents or workings web application.<br />
If possible, limit alternate HTTP method usage to a single<br />
page that contains no user actions, such the default landing page<br />
(example: index.html).<br />
How to Test<br />
As the HTML standard does not support request methods other<br />
than GET or POST, we will need to craft custom HTTP requests to<br />
test the other methods. We highly recommend using a tool to do<br />
this, although we will demonstrate how to do manually as well.<br />
Manual HTTP verb tampering testing<br />
This example is written using the netcat package from openbsd<br />
(standard with most Linux distributions). You may also use telnet<br />
(included with Windows) in a similar fashion.<br />
1. Crafting custom HTTP requests<br />
• Each HTTP 1.1 request follows the following basic formatting<br />
and syntax. Elements surrounded by brackets [ ] are contextual to<br />
your application. The empty newline at the end is required.<br />
[METHOD] /[index.htm] HTTP/1.1<br />
host: [www.example.com]<br />
• In order to craft separate requests, you can manually type each<br />
request into netcat or telnet and examine the response. However,<br />
to speed up testing, you may also store each request in a separate<br />
file.<br />
This second approach is what we’ll demonstrate in these examples.<br />
Use your favorite editor to create a text file for each method.<br />
Modify for your application’s landing page and domain.<br />
1.1 OPTIONS<br />
OPTIONS /index.html HTTP/1.1<br />
host: www.example.com<br />
1.2 GET<br />
1.4 POST<br />
POST /index.html HTTP/1.1<br />
host: www.example.com<br />
1.5 PUT<br />
PUT /index.html HTTP/1.1<br />
host: www.example.com<br />
1.6 DELETE<br />
DELETE /index.html HTTP/1.1<br />
host: www.example.com<br />
1.7 TRACE<br />
TRACE /index.html HTTP/1.1<br />
host: www.example.com<br />
1.8 CONNECT<br />
CONNECT /index.html HTTP/1.1<br />
host: www.example.com<br />
2. Sending HTTP requests<br />
• For each method and/or method text file, send the request to<br />
nc www.example.com 80 < OPTIONS.http.txt<br />
your web server via netcat or telnet on port 80 (HTTP):<br />
3. Parsing HTTP responses<br />
Whitepapers<br />
• RSnake: “XSS (Cross Site Scripting) Cheat Sheet” - http: /ha.ckers.org/xss.html<br />
• CERT: “CERT Advisory CA-2000-02 Malicious HTML Tags Embedded<br />
in Client Web Requests” - http: /www.cert.org/advisories/CA-2000-02.html<br />
• Amit Klein: “Cross-site Scripting Explained” - http: /courses.<br />
csail.mit.edu/6.857/2009/handouts/css-explained.pdf<br />
• Gunter Ollmann: “HTML Code Injection and Cross-site Scripting”<br />
- http: /www.technicalinfo.net/papers/CSS.html<br />
• CGISecurity.com: “The Cross Site Scripting FAQ” - http: /www.<br />
cgisecurity.com/xss-faq.html<br />
• Blake Frantz: “Flirting with MIME Types: A Browser’s Perspective”<br />
- http: /www.leviathansecurity.com/pdf/Flirting%20with%20<br />
Oddly, the other valid HTTP methods are not supported by the<br />
HTML standard [4]. Any HTTP method other than GET or POST<br />
needs to be called outside the HTML document. However, JavaScript<br />
and AJAX calls may send methods other than GET and POST.<br />
As long as the web application being tested does not specifically<br />
call for any non-standard HTTP methods, testing for HTTP verb<br />
tampering is quite simple. If the server accepts a request other<br />
than GET or POST, the test fails. The solutions is to disable all non<br />
GET or POST functionality within the web application server, or in<br />
a web application firewall.<br />
If methods such as HEAD or OPTIONS are required for your application,<br />
this increases the burden of testing substantially. Each ac-<br />
GET /index.html HTTP/1.1<br />
host: www.example.com<br />
1.3 HEAD<br />
HEAD /index.html HTTP/1.1<br />
host: www.example.com<br />
• Although each HTTP method can potentially return different results,<br />
there is only a single valid result for all methods other than<br />
GET and POST. The web server should either ignore the request<br />
completely or return an error. Any other response indicates a test<br />
failure as the server is responding to methods/verbs that are unnecessary.<br />
These methods should be disabled.<br />
• An example of a failed test (ie, the server supports OPTIONS despite<br />
no need for it):