1BO4r2U
1BO4r2U
1BO4r2U
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
155 156<br />
Web Application Penetration Testing<br />
Web Application Penetration Testing<br />
References<br />
• RFC2616] Hypertext Transfer Protocol -- HTTP/1.1<br />
• [ErrorDocument] Apache ErrorDocument Directive<br />
• [AllowOverride] Apache AllowOverride Directive<br />
• [ServerTokens] Apache ServerTokens Directive<br />
• [ServerSignature] Apache ServerSignature Directive<br />
Remediation<br />
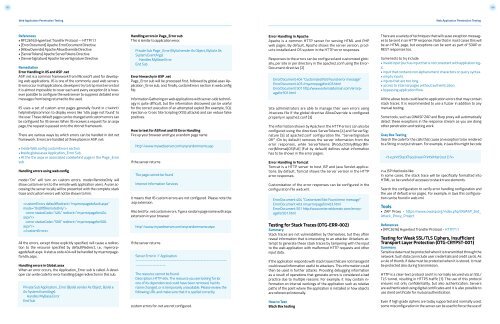
Error Handling in IIS and ASP .net<br />
ASP .net is a common framework from Microsoft used for developing<br />
web applications. IIS is one of the commonly used web servers.<br />
Errors occur in all applications, developers try to trap most errors but<br />
it is almost impossible to cover each and every exception (it is however<br />
possible to configure the web server to suppress detailed error<br />
messages from being returned to the user).<br />
IIS uses a set of custom error pages generally found in c:\winnt\<br />
help\iishelp\common to display errors like ‘404 page not found’ to<br />
the user. These default pages can be changed and custom errors can<br />
be configured for IIS server. When IIS receives a request for an aspx<br />
page, the request is passed on to the dot net framework.<br />
There are various ways by which errors can be handled in dot net<br />
framework. Errors are handled at three places in ASP .net:<br />
• Inside Web.config customErrors section<br />
• Inside global.asax Application_Error Sub<br />
• At the the aspx or associated codebehind page in the Page_Error<br />
sub<br />
Handling errors using web.config<br />
mode=”On” will turn on custom errors. mode=RemoteOnly will<br />
show custom errors to the remote web application users. A user accessing<br />
the server locally will be presented with the complete stack<br />
trace and custom errors will not be shown to him.<br />
<br />
<br />
<br />
<br />
All the errors, except those explicitly specified, will cause a redirection<br />
to the resource specified by defaultRedirect, i.e., myerrorpagedefault.aspx.<br />
A status code 404 will be handled by myerrorpagefor404.aspx.<br />
Handling errors in Global.asax<br />
When an error occurs, the Application_Error sub is called. A developer<br />
can write code for error handling/page redirection in this sub.<br />
Private Sub Application_Error (ByVal sender As Object, ByVal e<br />
As System.EventArgs)<br />
Handles MyBase.Error<br />
End Sub<br />
Handling errors in Page_Error sub<br />
This is similar to application error.<br />
Private Sub Page_Error (ByVal sender As Object, ByVal e As<br />
System.EventArgs)<br />
Handles MyBase.Error<br />
End Sub<br />
Error hierarchy in ASP .net<br />
Page_Error sub will be processed first, followed by global.asax Application_Error<br />
sub, and, finally, customErrors section in web.config<br />
file.<br />
Information Gathering on web applications with server-side technology<br />
is quite difficult, but the information discovered can be useful<br />
for the correct execution of an attempted exploit (for example, SQL<br />
injection or Cross Site Scripting (XSS) attacks) and can reduce false<br />
positives.<br />
How to test for ASP.net and IIS Error Handling<br />
Fire up your browser and type a random page name<br />
http:\\www.mywebserver.com\anyrandomname.asp<br />
If the server returns<br />
The page cannot be found<br />
Internet Information Services<br />
it means that IIS custom errors are not configured. Please note the<br />
.asp extension.<br />
Also test for .net custom errors. Type a random page name with aspx<br />
extension in your browser<br />
http:\\www.mywebserver.com\anyrandomname.aspx<br />
If the server returns<br />
Server Error in ‘/’ Application.<br />
------------------------------------------------------------<br />
--------------------<br />
The resource cannot be found.<br />
Description: HTTP 404. The resource you are looking for (or<br />
one of its dependencies) could have been removed, had its<br />
name changed, or is temporarily unavailable. Please review the<br />
following URL and make sure that it is spelled correctly.<br />
custom errors for .net are not configured.<br />
Error Handling in Apache<br />
Apache is a common HTTP server for serving HTML and PHP<br />
web pages. By default, Apache shows the server version, products<br />
installed and OS system in the HTTP error responses.<br />
Responses to the errors can be configured and customized globally,<br />
per site or per directory in the apache2.conf using the Error-<br />
Document directive [2]<br />
ErrorDocument 404 “Customized Not Found error message”<br />
ErrorDocument 403 /myerrorpagefor403.html<br />
ErrorDocument 501 http:/www.externaldomain.com/errorpagefor501.html<br />
Site administrators are able to manage their own errors using<br />
.htaccess file if the global directive AllowOverride is configured<br />
properly in apache2.conf [3]<br />
The information shown by Apache in the HTTP errors can also be<br />
configured using the directives ServerTokens [4] and ServerSignature<br />
[5] at apache2.conf configuration file. “ServerSignature<br />
Off” (On by default) removes the server information from the<br />
error responses, while ServerTokens [ProductOnly|Major|Minor|Minimal|OS|Full]<br />
(Full by default) defines what information<br />
has to be shown in the error pages.<br />
Error Handling in Tomcat<br />
Tomcat is a HTTP server to host JSP and Java Servlet applications.<br />
By default, Tomcat shows the server version in the HTTP<br />
error responses.<br />
Customization of the error responses can be configured in the<br />
configuration file web.xml.<br />
ErrorDocument 404 “Customized Not Found error message”<br />
ErrorDocument 403 /myerrorpagefor403.html<br />
ErrorDocument 501 http:/www.externaldomain.com/errorpagefor501.html<br />
Testing for Stack Traces (OTG-ERR-002)<br />
Summary<br />
Stack traces are not vulnerabilities by themselves, but they often<br />
reveal information that is interesting to an attacker. Attackers attempt<br />
to generate these stack traces by tampering with the input<br />
to the web application with malformed HTTP requests and other<br />
input data.<br />
If the application responds with stack traces that are not managed it<br />
could reveal information useful to attackers. This information could<br />
then be used in further attacks. Providing debugging information<br />
as a result of operations that generate errors is considered a bad<br />
practice due to multiple reasons. For example, it may contain information<br />
on internal workings of the application such as relative<br />
paths of the point where the application is installed or how objects<br />
are referenced internally.<br />
How to Test<br />
Black Box testing<br />
There are a variety of techniques that will cause exception messages<br />
to be sent in an HTTP response. Note that in most cases this will<br />
be an HTML page, but exceptions can be sent as part of SOAP or<br />
REST responses too.<br />
Some tests to try include:<br />
• invalid input (such as input that is not consistent with application logic.<br />
• input that contains non alphanumeric characters or query syntax.<br />
• empty inputs.<br />
• inputs that are too long.<br />
• access to internal pages without authentication.<br />
• bypassing application flow.<br />
All the above tests could lead to application errors that may contain<br />
stack traces. It is recommended to use a fuzzer in addition to any<br />
manual testing.<br />
Some tools, such as OWASP ZAP and Burp proxy will automatically<br />
detect these exceptions in the response stream as you are doing<br />
other penetration and testing work.<br />
Gray Box Testing<br />
Search the code for the calls that cause an exception to be rendered<br />
to a String or output stream. For example, in Java this might be code<br />
<br />
in a JSP that looks like:<br />
In some cases, the stack trace will be specifically formatted into<br />
HTML, so be careful of accesses to stack trace elements.<br />
Search the configuration to verify error handling configuration and<br />
the use of default error pages. For example, in Java this configuration<br />
can be found in web.xml.<br />
Tools<br />
• ZAP Proxy - https://www.owasp.org/index.php/OWASP_Zed_<br />
Attack_Proxy_Project<br />
References<br />
• [RFC2616] Hypertext Transfer Protocol - HTTP/1.1<br />
Testing for Weak SSL/TLS Ciphers, Insufficient<br />
Transport Layer Protection (OTG-CRYPST-001)<br />
Summary<br />
Sensitive data must be protected when it is transmitted through the<br />
network. Such data can include user credentials and credit cards. As<br />
a rule of thumb, if data must be protected when it is stored, it must<br />
be protected also during transmission.<br />
HTTP is a clear-text protocol and it is normally secured via an SSL/<br />
TLS tunnel, resulting in HTTPS traffic [1]. The use of this protocol<br />
ensures not only confidentiality, but also authentication. Servers<br />
are authenticated using digital certificates and it is also possible to<br />
use client certificate for mutual authentication.<br />
Even if high grade ciphers are today supported and normally used,<br />
some misconfiguration in the server can be used to force the use of